Ensuring Data Integrity in Autonomous Experimentation: A Framework for Trustworthy AI-Driven Research
This article provides a comprehensive framework for researchers, scientists, and drug development professionals to ensure data integrity in autonomous experimentation.
Ensuring Data Integrity in Autonomous Experimentation: A Framework for Trustworthy AI-Driven Research
Abstract
This article provides a comprehensive framework for researchers, scientists, and drug development professionals to ensure data integrity in autonomous experimentation. As AI and automated systems transform biomedical research, maintaining data accuracy, consistency, and reliability from collection through analysis becomes paramount. We explore the foundational principles of data integrity, present actionable methodological strategies for implementation, address common troubleshooting and optimization challenges, and detail robust validation techniques. By synthesizing best practices from experimental design, AI validation, and regulatory science, this guide aims to equip professionals with the knowledge to build trustworthy, reproducible, and compliant autonomous research systems.
The Cornerstones of Trust: Why Data Integrity is Non-Negotiable in Autonomous Research
Defining Data Integrity in the Context of Autonomous Experimentation
Technical Support Center
Troubleshooting Guides
Issue 1: Inconsistent or Erroneous Experimental Results
- Problem: Automated systems are producing results that cannot be replicated or that deviate significantly from expected outcomes.
- Solution:
- Verify Input Integrity: Confirm the authenticity and quality of all source data. Check for correct sensor calibration and ensure all data streams are properly authenticated and cryptographically signed [1].
- Review Processing Integrity: Examine the automated scripts or AI models for errors. Use formally verified algorithms where possible and monitor systems for anomalous behavior during data transformation [1].
- Check System Integration: Ensure seamless communication between all laboratory systems (e.g., LIMS, ELNs, robotics). Inconsistent data across platforms can lead to flawed experimental execution [2].
- Prevention: Implement robust data validation checks at the point of data entry and establish regular calibration schedules for all laboratory equipment [2].
Issue 2: Audit Trail Gaps or Unexplained Data Modifications
- Problem: The electronic record of who, what, and when for data changes is incomplete, or data has been altered without a documented, valid reason.
- Solution:
- Enable Secure Audit Trails: Ensure all systems generating electronic records have a secure, computer-generated, time-stamped audit trail that tracks creation, modification, and deletion of records [3] [4].
- Enforce ALCOA++ Principles: Verify that all data is Attributable, Legible, Contemporaneous, Original, and Accurate, as well as Complete, Consistent, Enduring, and Available [3] [4].
- Review User Access Controls: Restrict system access to authorized personnel only to prevent unauthorized data changes [4].
- Prevention: Provide regular staff training on Good Documentation Practices (GDP) and the importance of contemporaneous record-keeping [3].
Issue 3: AI Model Producing Biased or Unreliable Predictions
- Problem: An AI/ML component of the autonomous experimentation platform is generating skewed outputs or failing to adapt to new data.
- Solution:
- Assess Training Data: Scrutinize the dataset used to train the model for completeness, accuracy, and potential biases. Biased input data will lead to biased and inaccurate outputs [5] [6].
- Implement Anomaly Detection: Integrate AI-powered validation tools that can identify data inconsistencies and outliers in real-time, preventing corrupted data from influencing the model [6].
- Ensure Model Transparency: Where possible, use explainable AI (XAI) techniques to understand the model's decision-making process, moving beyond the "black box" effect [5] [7].
- Prevention: Establish a continuous monitoring and validation protocol for all AI models used in research, including periodic retraining with updated, high-quality data [6].
Issue 4: Data Silos and Incompatible Systems
- Problem: Data is trapped in isolated systems (e.g., a single instrument's software), making it inaccessible for integrated analysis and compromising a unified view of the experiment.
- Solution:
- Implement Interoperability Standards: Utilize application programming interfaces (APIs) and data standards to enable communication between different instruments and software [2].
- Deploy a Unified Data Platform: Consider architectures like an Enterprise Data Fabric, which integrates disparate data sources into a unified, intelligent layer to ensure data is accessible and consistent [8].
- Adopt a Laboratory Information Management System (LIMS): A LIMS can centralize data storage and sample tracking, breaking down silos and providing a single source of truth [2].
- Prevention: During the procurement of new laboratory equipment or software, prioritize open standards and compatibility with existing infrastructure.
Frequently Asked Questions (FAQs)
Q1: What is data integrity and why is it critical for autonomous experimentation? A1: Data integrity is the maintenance and assurance of data's accuracy, consistency, and reliability throughout its entire lifecycle [4]. In autonomous experimentation, where AI agents and robotic systems execute complex workflows with minimal human oversight, integrity is the foundation of trust. Compromised data can lead to erroneous conclusions, invalidate research, and in fields like drug development, pose direct risks to patient safety [1] [3].
Q2: What are the ALCOA+ principles and how do I apply them? A2: ALCOA+ is a framework of principles for ensuring data integrity. It is a cornerstone of regulatory compliance in life sciences [3] [4]. The principles are:
- Attributable: Who created the data and when?
- Legible: Is the data readable and understandable?
- Contemporaneous: Was it recorded at the time of the activity?
- Original: Is this the first record or a certified true copy?
- Accurate: Is the data error-free and truthful? The "+" adds that data must also be Complete, Consistent, Enduring, Available, and that the process has integrity and transparency [3]. Apply them by designing experimental workflows and electronic systems that enforce these principles by default, for example, through automated metadata capture and immutable audit trails.
Q3: What are the most common data integrity failures in automated systems? A3: Common failures can be categorized by where they occur in the data lifecycle:
- Input Integrity Failures: Faulty sensor data or unvalidated data sources entering the system [1].
- Processing Integrity Failures: Software bugs, algorithm errors, or incorrect data transformations during analysis [1].
- Storage Integrity Failures: Data corruption, unauthorized modification, or cybersecurity breaches during storage [1].
- Contextual Integrity Failures: Data collected for one purpose being used in an inappropriate or non-transparent context [1].
Q4: How can I ensure our AI models maintain data integrity? A4:
- Quality Data In: Rigorously validate, clean, and check training data for biases to ensure the model learns from accurate information [5] [6].
- Transparent Processing: Prioritize model interpretability to understand how outputs are generated [5].
- Continuous Monitoring: Deploy anomaly detection to identify model drift or performance degradation in real-time [6].
- Robust Governance: Maintain clear documentation and audit trails for the model's development, training data, and performance history [6].
Data Integrity Failure Case Studies
The following table summarizes real-world examples of data integrity failures, highlighting the critical consequence of lapses in automated and computational systems.
| Case | Type of Failure | Consequence | Relevant Principle Violated |
|---|---|---|---|
| Boeing 737 MAX (2018) [1] | Input Integrity | Faulty sensor data caused an automated system to repeatedly force the airplane's nose down, leading to a fatal crash. | Accuracy, Consistency |
| NASA Mars Climate Orbiter (1999) [1] | Processing Integrity | A unit conversion error (pound-seconds vs. newton-seconds) between software systems caused the spacecraft to burn up in the Mars atmosphere. | Accuracy, Consistency |
| SolarWinds Supply-Chain Attack (2020) [1] | Storage Integrity | Hackers compromised a software update package, injecting malicious code that was distributed to 18,000 customers and remained undetected for months. | Availability, Security, Completeness |
| ChatGPT Data Leak (2023) [1] | Storage Integrity | A software bug mixed different users' conversation histories, exposing private data and making it impossible for users to prove which conversations were theirs. | Attributable, Original, Confidentiality |
Experimental Protocol: Validating an Autonomous Data Workflow
Objective: To establish a standardized methodology for verifying the end-to-end integrity of data generated by an autonomous experimental platform.
1. Materials and Reagents
- Reference Standard: A certified material with known, stable properties (e.g., a specific chemical compound with a known spectral signature).
- Calibration Standards: A set of standards for calibrating all sensors and instruments involved in the workflow.
- Data Integrity Assessment Software: Tools capable of generating checksums (e.g., SHA-256 hashes) and analyzing audit trails.
2. Methodology 1. System Preparation: Calibrate all instruments using the calibration standards. Document all procedures contemporaneously. 2. Sample Run: Process the reference standard through the entire autonomous workflow, from sample introduction to data analysis and report generation. 3. Data Capture and Hashing: At each stage of the workflow (input, processing, output), automatically generate a cryptographic hash (checksum) of the data. 4. Audit Trail Review: Upon completion, export and review the system's audit trail. Verify that all steps are recorded, attributable to the system or responsible user, and time-stamped. 5. Result Verification: Compare the final output generated by the autonomous system against the expected result for the reference standard. 6. Hash Verification: Recompute the hashes for stored data and compare them to the original hashes generated during the run to ensure data has not been altered.
3. Data Analysis
- The test is considered a PASS if:
- The final result matches the expected value within a pre-defined acceptance range.
- All cryptographic hashes match, confirming data has not been corrupted or modified.
- The audit trail provides a complete, gap-free record of the entire process, compliant with ALCOA+ principles.
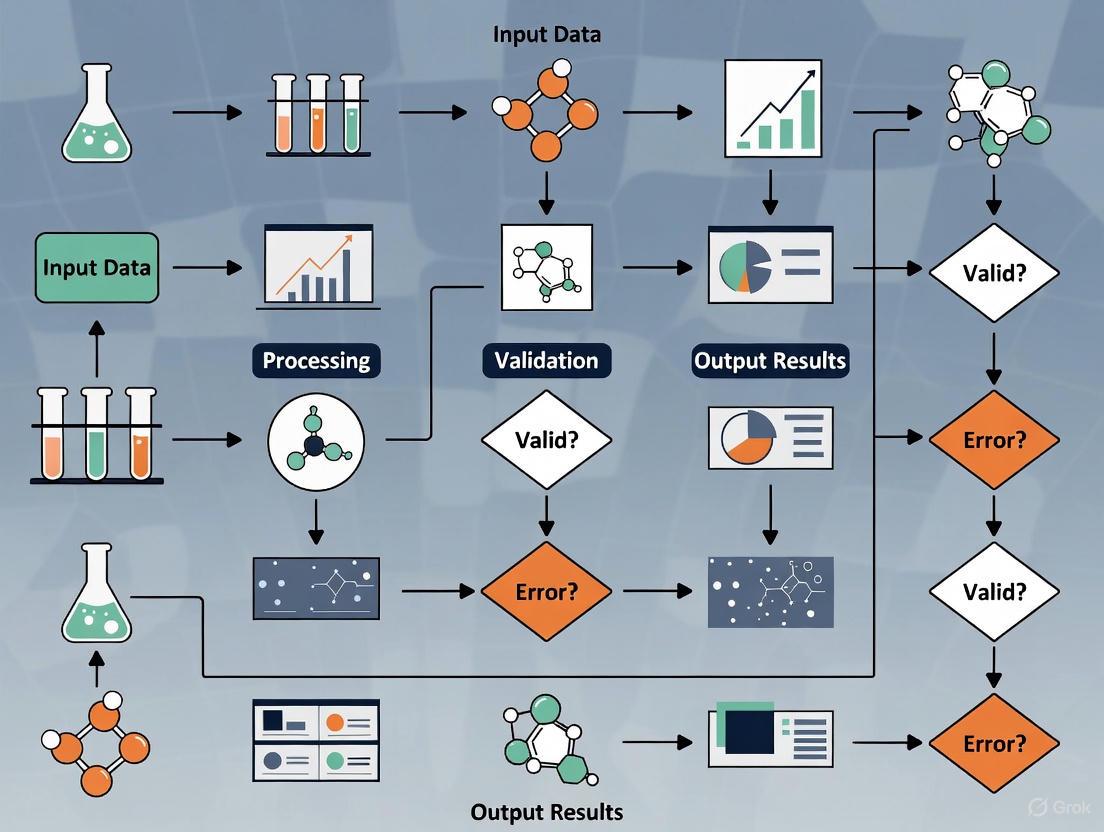
Data Integrity Workflow for Autonomous Experimentation
The Scientist's Toolkit: Research Reagent Solutions for Data Integrity
The following table details key system and software solutions essential for maintaining data integrity in an automated research environment.
| Tool / Solution | Function | Key Feature for Integrity |
|---|---|---|
| Laboratory Information Management System (LIMS) [2] | Centralizes sample and data tracking, connecting instruments and data sources. | Breaks down data silos, ensures data is original and complete. |
| Electronic Lab Notebook (ELN) | Provides a digital platform for recording experimental procedures and results. | Ensures records are attributable, legible, and contemporaneous. |
| AI-Powered Anomaly Detection [6] | Uses machine learning to identify outliers and irregular patterns in data streams in real-time. | Protects accuracy by flagging potential errors or fabrication. |
| Cryptographic Hashing Tool | Generates a unique digital fingerprint (hash) for a dataset at a specific point in time. | Verifies that data has not been altered, ensuring accuracy and consistency. |
| Automated Audit Trail System [3] [4] | Logs all data-related actions (create, modify, delete) with a user and timestamp. | Provides a complete, consistent, and enduring record for accountability. |
In modern pharmaceutical and clinical research, data is the fundamental asset upon which critical decisions about patient safety and product efficacy are made. Data integrity—the maintenance and assurance of data accuracy and consistency throughout its lifecycle—is not merely a regulatory hurdle but a scientific and ethical imperative [3]. In the context of autonomous experimentation, where automated systems generate and process vast datasets, ensuring data integrity becomes both more complex and more crucial. Compromised data can derail research, invalidate clinical trials, and most alarmingly, pose direct risks to patient health. This technical support center provides a practical framework for researchers and scientists to troubleshoot common data integrity issues, understand their high-stakes consequences, and implement robust preventive measures.
Understanding the Threat Landscape and Consequences
The pharmaceutical sector is a high-priority target for cyber adversaries, dominated by data-centric cybercrime aimed at monetizing valuable research and intellectual property [9]. Understanding this landscape is the first step in building effective defenses.
The table below summarizes the dominant cyber threats facing the pharmaceutical industry, based on an analysis of 172 recorded incidents from January to late September 2025 [9].
| Threat Category | Percentage of Attacks | Primary Motivation |
|---|---|---|
| Ransomware | 29.1% | Financial gain via data encryption and theft |
| Data Breaches | 26.7% | Theft of intellectual property and sensitive data |
| DDoS Attacks | 16.9% | Disruption of operations and services |
| Sale of Initial Access | 14.0% | Providing entry points for other threat actors |
| Website Defacements | 13.4% | Ideological or political statements |
Consequences of Data Integrity Failures
The repercussions of data compromise extend far beyond operational inconvenience, impacting every stakeholder from the research institution to the end-patient.
- Regulatory and Compliance Repercussions: Regulatory bodies like the FDA and EMA issue warning letters, fines, and product recalls. In severe cases, data integrity lapses can lead to the rejection of marketing applications, nullifying years of research and investment [10] [3]. Manufacturers remain responsible for the integrity of all data they submit, even when generated by third-party labs [10].
- Direct Risks to Patient Safety: The most severe consequence is the potential harm to patients. Inaccurate data from biocompatibility studies or clinical trials can lead to the approval and use of unsafe or ineffective drugs and medical devices, directly jeopardizing public health [10] [3].
- Operational and Financial Impact: Data integrity incidents can halt production lines, necessitate costly batch recalls, and trigger massive re-testing requirements. The resulting drug shortages also have a broader negative impact on the healthcare system [11].
- Reputational Damage and Loss of Trust: A loss of credibility with regulators, investors, and the public can be devastating and long-lasting, damaging an organization's reputation and eroding stakeholder confidence [12].
Frequently Asked Questions (FAQs) on Data Integrity
Q1: What is ALCOA+ and why is it a cornerstone of data integrity?
A: ALCOA+ is an acronym representing the core principles for ensuring data is trustworthy and reliable. It is a foundational framework for data integrity in regulated environments [12] [3].
- Attributable: Data must clearly show who created it and when.
- Legible: Data must be readable and permanent.
- Contemporaneous: Data must be recorded at the time the work is performed.
- Original: The first recorded capture of the data must be preserved.
- Accurate: Data must be error-free, truthful, and reflect actual observations.
The "plus" principles include:
- Complete: All data must be present, including any repeats or reanalyses.
- Consistent: Data should be chronologically sequenced and any changes should not obscure the original record.
- Enduring: Data must be recorded in a permanent medium that lasts for the required retention period.
- Available: Data must be accessible for review, audit, or inspection throughout its retention period.
Q2: We use electronic lab notebooks (ELNs). How do audit trails work?
A: An audit trail is a secure, computer-generated, time-stamped electronic record that allows for the reconstruction of the course of events relating to the creation, modification, or deletion of an electronic record [3]. In an ELN, it automatically records:
- Who accessed a record and when.
- What changes were made (the old and new values).
- Why a change was made (if a reason is provided). Audit trails are crucial for demonstrating record compliance and are a key focus during regulatory inspections. The principle is simple: if a task or event is not documented, it is considered not to have happened [3].
Q3: What are the most common data integrity violations we should avoid?
A: Common violations cited by regulators include [10] [3]:
- Deletion or manipulation of data without justification.
- Aborting sample analyses arbitrarily without a documented, scientifically sound reason.
- Invalidating results without proper justification.
- Failure to document work at the time it is performed (non-contemporaneous recording).
- Using uncontrolled documentation, such as loose paper or unvalidated spreadsheets.
- Lack of traceability in test records, making it impossible to reconstruct the study.
Troubleshooting Guides for Common Experimental Scenarios
Guide 1: Troubleshooting a Failed TR-FRET Assay
Problem: There is no assay window in your Time-Resolved Förster Resonance Energy Transfer (TR-FRET) experiment.
Investigation and Resolution Workflow:
Detailed Troubleshooting Steps:
- Confirm Instrument Setup: The most common reason for a complete lack of an assay window is improper instrument configuration. Always consult your instrument's setup guide for TR-FRET measurements before beginning any experimental work [13].
- Verify Emission Filters: Unlike other fluorescence assays, TR-FRET is highly sensitive to the emission filters used. Using an incorrect filter can "make or break the assay." Ensure you are using the exact filters recommended for your specific microplate reader model and the specific TR-FRET assay (e.g., Terbium vs. Europium) [13].
- Test the System: Before using valuable experimental compounds, test your microplate reader's TR-FRET setup using the reagents provided with your assay kit. This helps isolate the problem to either the instrument or the specific assay conditions [13].
Data Analysis Considerations:
- Use Ratios: Always use the acceptor/donor emission ratio (e.g., 520 nm/495 nm for Tb) for data analysis, not raw Relative Fluorescence Units (RFU). This ratio accounts for pipetting variances and lot-to-lot reagent variability [13].
- Assess Robustness with Z'-factor: A large assay window alone is not sufficient. Calculate the Z'-factor to statistically evaluate assay robustness. An assay with a Z'-factor > 0.5 is considered excellent for screening. It considers both the assay window size and the data variation (noise) [13].
Guide 2: Addressing Particle Contamination in Manufacturing
Problem: Unexpected particulate matter is discovered in a drug product during manufacturing.
Investigation and Resolution Workflow:
Detailed Troubleshooting Steps:
- Information Gathering (The "What, When, Who"): Immediately document all relevant information: a description of the particles, the batch and time of occurrence, and the personnel, equipment, and raw materials involved [11].
- Initial Physical Analysis: Use fast, non-destructive techniques first.
- SEM-EDX (Scanning Electron Microscopy with Energy Dispersive X-ray Spectroscopy): Ideal for identifying inorganic compounds (e.g., metal abrasion from equipment, rust) and analyzing surface topography [11].
- Raman Spectroscopy: Effectively identifies organic particles by comparing their spectral signature to databases and reference materials [11].
- Advanced Chemical Analysis (if required): If physical methods are inconclusive, proceed to chemical structure elucidation.
- Perform qualitative solubility tests to understand the contaminant's nature.
- Use powerful techniques like LC-HRMS (Liquid Chromatography-High Resolution Mass Spectrometry) or NMR (Nuclear Magnetic Resonance) to identify the molecular structure of the contaminant, which is critical for understanding its origin and potential impact [11].
Guide 3: Ensuring Data Integrity in EHR-to-EDC Integration
Problem: How to prevent data integrity issues when transferring electronic health record (EHR) data to an electronic data capture (EDC) system for clinical trials.
Investigation and Resolution Workflow:
Detailed Troubleshooting and Prevention Steps:
- Move Beyond Manual Entry: Avoid manual transcription of data from EHRs to EDC systems, as this is a primary source of errors and increases audit risk [14].
- Implement Automated, Real-Time Integration: Use solutions that leverage standardized interfaces like FHIR (Fast Healthcare Interoperability Resources) APIs to pull data directly from EHRs into the EDC in real-time, minimizing delay and manual intervention [14].
- Ensure Full Traceability: The system must provide a complete audit trail that links every data point in the EDC back to its original source in the EHR, including the data originator and element identifiers. This is essential for audit readiness and compliance with FDA guidance [14].
- Incorporate Built-in Validation: Automated checks for data type, range, and logical consistency should be performed during the transfer to preemptively catch and flag discrepancies [14].
The Scientist's Toolkit: Essential Research Reagent Solutions
The following table details key reagents and materials used in the experiments and troubleshooting guides featured above.
| Item | Function / Application | Key Considerations |
|---|---|---|
| LanthaScreen TR-FRET Reagents | Used in kinase binding and cellular assays. Provides a sensitive, ratiometric readout for studying biomolecular interactions. | Contains lanthanide donors (Tb or Eu); requires specific instrument filters. Lot-to-lot variability is normalized by using acceptor/donor ratios [13]. |
| Z'-LYTE Assay Kit | A fluorescence-based kinase activity assay. Measures percent phosphorylation of a peptide substrate. | Output is a blue/green ratio. The assay is non-linear between 0% and 100% phosphorylation; requires specific controls for interpretation [13]. |
| Development Reagent | Used in Z'-LYTE kits to cleave non-phosphorylated peptide substrate, generating the assay signal. | Concentration is critical; over- or under-development can eliminate the assay window. Pre-titrated for consistency [13]. |
| FHIR-Enabled eSource Solution | Software that automates the transfer of clinical data from EHR systems to EDC systems. | Ensures data integrity by eliminating manual transcription, providing real-time integration, and maintaining a full audit trail for regulatory compliance [14]. |
Proactive Measures: Building a Culture of Data Integrity
Preventing data integrity issues is more effective than troubleshooting them. Key strategies include:
- Implement Robust Quality Management Systems (QMS): Establish and enforce clear policies and procedures that embed data integrity principles into everyday workflows [12].
- Invest in Continuous Training: Regularly train all personnel, from researchers to technicians, on Good Documentation Practices (GDP), ALCOA+ principles, and the specific operational procedures of your data systems [12] [3].
- Leverage Validated Computer Systems: Ensure all computerized systems used for data generation and handling, including those for autonomous experimentation, undergo rigorous Computer System Validation (CSV). This confirms the systems operate correctly and produce reliable, accurate results [12].
- Conduct Regular Audits and Reviews: Perform both internal and external audits to proactively identify and rectify potential data integrity gaps before they become critical failures [12].
In the realm of autonomous experimentation, ensuring the trustworthiness of data is paramount. The ALCOA++ and FAIR principles provide complementary frameworks to achieve robust data integrity and reuse. ALCOA++, originating from highly regulated life sciences environments, provides a foundational framework for ensuring data credibility and regulatory compliance throughout its lifecycle [15] [16]. The FAIR principles (Findable, Accessible, Interoperable, and Reusable) emphasize machine-actionability, aiming to optimize the reuse of digital assets by both humans and computational systems [17]. When applied to automated systems, these frameworks work in concert to create data that is both intrinsically reliable and optimally usable for advanced analysis and decision-making.
Understanding the ALCOA++ Framework
ALCOA++ has evolved from the original ALCOA (Attributable, Legible, Contemporaneous, Original, Accurate) to include additional principles that address modern digital data challenges [15] [16]. The table below summarizes the core components and their applications in automated systems.
Table: ALCOA++ Principles and Their Application in Automated Systems
| Principle | Core Meaning | Application in Automated Systems |
|---|---|---|
| Attributable | Data linked to creator/source [15] | Unique user IDs, device metadata, audit trails [15] |
| Legible | Permanently readable [15] | Durable data formats, reversible encoding [15] |
| Contemporaneous | Recorded in real-time [15] | Automated timestamps synchronized to external standards (e.g., UTC) [15] |
| Original | First capture preserved [15] | Secure, dynamic source data (e.g., device waveforms, event logs) [15] |
| Accurate | Error-free and truthful [15] | Validated systems, calibrated instruments, amendment controls [15] |
| Complete | No deletions, all data present [15] | Immutable audit trails, retention of all metadata for event reconstruction [15] |
| Consistent | Chronological and uniform [15] | Standardized units, sequential timestamps, contradiction detection [15] |
| Enduring | Lasting and usable [15] | Long-term viable formats, backups, disaster recovery plans [15] |
| Available | Retrievable when needed [15] | Indexed, searchable storage for timely retrieval during retention period [15] |
| Traceable | Full history reconstructable [15] | Audit trails capturing "who, what, when, why" of all changes [15] |
Understanding the FAIR Principles
The FAIR principles provide a structured approach to enhancing data utility, focusing on machine-actionability to manage the increasing volume and complexity of research data [17] [18].
Table: The FAIR Principles for Research Data Management
| Principle | Core Objective | Key Technical Requirements |
|---|---|---|
| Findable | Easy discovery by humans and computers [17] | Rich metadata, globally unique and persistent identifiers, data indexing in searchable resources [17] |
| Accessible | Clarity on data retrieval methods [17] | Standardized, open protocols for metadata and data access, authentication/authorization where necessary [17] |
| Interoperable | Seamless integration with other data and workflows [17] | Use of formal, accessible, shared languages and vocabularies, qualified references to other metadata [17] |
| Reusable | Optimization for future replication and combination [17] | Plurality of accurate and relevant attributes, clear usage licenses, provenance information, domain-relevant community standards [17] |
Mapping ALCOA++ to FAIR for Automated Systems
The synergy between ALCOA++ and FAIR creates a comprehensive data governance ecosystem. ALCOA++ ensures the data's foundational integrity from the moment of creation, while FAIR principles ensure its long-term value and reusability. The following diagram illustrates how key components of ALCOA++ support the overarching goals of the FAIR principles.
Technical Support: Troubleshooting Common Data Integrity Issues
This section provides targeted guidance for resolving common data integrity challenges in automated experimental systems.
FAQ 1: How do I resolve "unattributable data entries" in our automated assay platform?
- Problem: The system audit log shows data creation events, but the user field is blank or lists a generic system account.
- Solution:
- Verify Authentication Configuration: Ensure the instrument software is integrated with your corporate identity provider (e.g., LDAP, Active Directory) and does not allow anonymous or shared logins. Enforce unique user IDs as required by ALCOA++'s "Attributable" principle [15].
- Inspect Session Timeouts: Check if the data was recorded after a user session timed out. Adjust timeout policies or configure the system to pause data recording upon logout.
- Review System Account Usage: Prohibit the use of generic service accounts for routine data acquisition. Service accounts should only be used for background system processes, not user-driven experiments.
- Prevention Protocol: Implement and validate a pre-experiment checklist where users must confirm their login status. Configure the system to require re-authentication after a period of inactivity.
FAQ 2: Our automated liquid handler generates data, but reviewers cannot trace the raw source files. What is wrong?
- Problem: Processed data is available in the LIMS, but the original data files from the instrument are missing, violating the "Original" and "Traceable" principles [15].
- Solution:
- Map the Data Flow: Document the complete path from instrument sensor to final storage, identifying all temporary caches and transfer points.
- Validate Transfer Processes: Ensure that automated file transfer scripts (e.g., using Rsync, REST APIs) include checksum verification to confirm data integrity upon movement. The transfer must be validated to support ALCOA++'s "Accurate" principle [15].
- Check Storage Permissions: Verify that the destination directory has correct write permissions and sufficient disk space to receive the files.
- Prevention Protocol: Design a workflow where the original data file is immediately written to a secured, WORM (Write Once, Read Many) network drive upon creation, with a unique and persistent identifier assigned to make it "Findable" per FAIR [17].
FAQ 3: Data from a high-throughput scanner is inconsistent and fails basic validation checks.
- Problem: The output data shows unexpected fluctuations and outliers, suggesting a failure in data "Accuracy" and "Consistency" [15].
- Solution:
- Perform Contemporaneous Control Check: Run a standard control sample immediately and analyze its results against expected values. This tests the system at the time of the fault.
- Review Calibration Logs: Check the instrument's internal log for calibration records, errors, or warnings. Confirm that all scheduled maintenance and calibrations are up-to-date, which is critical for "Accurate" data [15].
- Check Environmental Sensors: Review logs from room/environmental monitors (temperature, humidity) for correlations with the data anomalies.
- Prevention Protocol: Implement a system where the automated workflow requires a successful control check before processing a batch of experimental samples. This ensures "Consistent" data generation [15].
FAQ 4: An external collaborator cannot access or interpret our shared research dataset.
- Problem: The dataset was shared, but the collaborator finds it difficult to use, failing the FAIR principles of "Accessibility" and "Reusability" [17].
- Solution:
- Audit Metadata Completeness: Use an automated FAIR assessment tool (e.g., F-UJI [18]) to evaluate if the dataset has sufficient, standards-compliant metadata.
- Provide a Data Dictionary: Share a document that defines all variables, units, and formats used. This enhances "Interoperability" [17].
- Specify the License: Attach a clear usage license to the dataset, which is a key requirement for "Reusability" [17].
- Prevention Protocol: Before data sharing, use a predefined checklist based on the FAIR principles to ensure all necessary metadata, documentation, and licensing information is included.
The following diagram illustrates a systematic workflow for diagnosing and resolving these common data integrity issues.
The Scientist's Toolkit: Essential Research Reagent Solutions
The following table details key digital and physical resources essential for implementing robust data integrity in automated research environments.
Table: Essential Reagents and Solutions for Data Integrity in Automated Systems
| Item | Primary Function | Role in ALCOA++/FAIR Implementation |
|---|---|---|
| Electronic Lab Notebook (ELN) | Centralizes experimental data and metadata [19] | Ensures data is Attributable, Contemporaneous, and Complete; enhances Findability and Reusability [15] [17]. |
| Laboratory Information Management System (LIMS) | Manages samples, associated data, and workflows [2] | Provides a structured environment for Consistent, Enduring, and Available data [15] [2]. |
| Reference Standards & Controls | Calibrates instruments and validates assays | Foundational for generating Accurate data; critical for reliable and reproducible results [15]. |
| Automated Audit Trail System | Logs all data-related actions automatically [15] | Core to being Traceable and Complete; provides a reconstruction path for all events [15]. |
| Unique Persistent Identifiers (PIDs) | Provides permanent, unique names for digital objects [17] | Makes data Findable and citable; a core technical requirement of the FAIR principles [17] [18]. |
| Standardized Metadata Templates | Structures descriptive information about data [17] | Enriches data context for Interoperability and Reusability by humans and machines [17]. |
Frequently Asked Questions (FAQs)
Q1: What is 'scenario explosion' in the context of autonomous experimentation, and how does it threaten data integrity? Scenario explosion refers to the rapid growth in the number of experimental parameters, conditions, and decision paths that an AI-driven experimentation platform must evaluate. This threatens data integrity by increasing the risk of undiscovered edge cases and logical flaws, which can lead to the generation of irreproducible or contaminated data. Ensuring system robustness against this explosion is critical for maintaining protocol fidelity.
Q2: Why is AI explainability a unique challenge for drug development research? AI models, particularly complex deep learning systems, can often function as "black boxes," making it difficult to understand the rationale behind their experimental decisions. In drug development, a lack of explainability undermines scientific validation, complicates regulatory approval, and can obscure biases or errors in the training data that jeopardize the integrity of research findings.
Q3: Our AI agent is recommending illogical experimental protocols. How can I troubleshoot this? This is often a symptom of issues with the training data or model logic. Follow this protocol:
- Audit Training Data: Verify the quality, completeness, and freedom from bias in the datasets used to train the agent.
- Enable Logging: Ensure the agent's decision-making process is fully logged to trace the root cause of the illogical output.
- Implement Model Monitoring: Use specialized tools to continuously monitor for model drift or performance degradation that could lead to erroneous recommendations [20].
Q4: How can we ensure our automated systems maintain data integrity when operating at high throughput? High-throughput operations require automated and continuous integrity checks.
- Data Lineage Tracking: Implement systems that track the origin, transformation, and movement of data throughout its lifecycle.
- Automated Anomaly Detection: Deploy machine learning models that can analyze vast amounts of data quickly to identify anomalies, predict failures, and suggest solutions in real-time, preventing the propagation of errors [20].
Q5: What are the best practices for validating an AI model used in autonomous experimentation? Best practices include:
- Rigorous Testing: Conduct extensive testing against a wide range of scenarios, including edge cases, to uncover hidden flaws.
- Performance Benchmarking: Compare the AI's outputs and decisions against established scientific knowledge and manual experiments.
- Explainability Tools: Integrate tools that provide insights into the model's decision-making process, making it interpretable to researchers [20].
Troubleshooting Guides
Guide 1: Troubleshooting Unexplained AI Decision-Making (The "Black Box" Problem)
Symptoms: Inability to trace the reasoning behind an AI agent's experimental choices; failure to provide a scientific justification for a protocol.
Diagnostic Steps:
- Check for Explainability Features: Confirm that the AI system has explainability-AI (XAI) features, such as saliency maps or feature importance scores, enabled and configured.
- Analyze Input Data: Examine the input data for the specific decision. Look for outliers, missing values, or potential data corruption that may have skewed the result.
- Review Model Logs: Scrutinize the model's inference logs, if available, to identify the key features and internal thresholds that influenced the output.
Resolution:
- Short-term: For the specific unexplained decision, consider running a parallel, traditional statistical analysis to validate the outcome.
- Long-term: Integrate an XAI framework into your model deployment pipeline. This ensures all future decisions are accompanied by reasoning metadata [20].
Guide 2: Resolving Data Integrity Failures in Automated Workflows
Symptoms: Inconsistent experimental results; missing metadata; inability to reproduce a previously successful automated experiment.
Diagnostic Steps:
- Verify Data Lineage: Use your data lineage tool to trace the data from its final result back to its raw source. Look for gaps or unauthorized transformations.
- Check Workflow Logic: Review the automated workflow definition for logical errors, especially in conditional branches that may have been triggered by a new, untested scenario ("scenario explosion").
- Audit System Logs: Check for system errors, connectivity issues, or permission failures that may have interrupted data capture or processing.
Resolution:
- Immediate Action: Quarantine the affected data sets to prevent contamination of downstream analysis.
- Systemic Fix: Strengthen data validation checkpoints at each stage of the workflow. Implement additional automated checks for data format, range, and completeness before critical steps proceed [20].
Research Reagent Solutions
| Item | Function |
|---|---|
| High-Fidelity DNA Polymerase | Essential for accurate amplification of genetic material in PCR protocols, ensuring data integrity in genetic analyses. |
| Cell Viability Assay Kits | Provide quantitative metrics on cell health, a critical parameter for validating experimental conditions in biological assays. |
| Protease Inhibitor Cocktails | Preserve protein integrity by preventing degradation during sample preparation, ensuring reliable results in proteomics. |
| Stable Isotope-Labeled Metabolites | Act as internal standards in mass spectrometry for precise quantification, enhancing data accuracy in metabolic flux studies. |
| Validated siRNA Libraries | Enable targeted gene silencing in functional genomics screens, ensuring the specificity and reliability of phenotypic data. |
Experimental Protocol: Validating AI-Generated Experimental Designs
Objective: To empirically verify that protocols generated by an autonomous AI agent are scientifically sound, reproducible, and capable of producing high-integrity data.
Methodology:
- AI Protocol Generation: Input a defined research question and set of constraints into the AI experimentation platform.
- Expert Blind Review: A panel of domain experts assesses the AI-generated protocol for logical coherence and safety without knowing its origin. A manually designed protocol for the same goal is reviewed in parallel.
- Parallel Execution: Both the AI-generated and manually designed protocols are executed in the laboratory under controlled conditions, with researchers blinded to the protocol's origin.
- Outcome Analysis: The resulting data from both experiments are compared against pre-defined success criteria, including measurement accuracy, signal-to-noise ratio, and reproducibility across replicates.
- Explainability Assessment: The AI system is required to output the key data points and reasoning steps that led to its proposed protocol, which is then evaluated for clarity and scientific plausibility.
Required Reagents:
- As per the specific experimental domain (e.g., reagents listed in the "Research Reagent Solutions" table).
Data Presentation
Table 1: Common AI-Related Data Integrity Challenges and Mitigation Strategies
| Challenge | Impact on Data Integrity | Recommended Mitigation |
|---|---|---|
| Scenario Explosion | Increased probability of untested edge cases producing invalid data. | Implement robust model-based testing and continuous validation frameworks. |
| AI Explainability (Black Box) | Inability to audit or validate the scientific basis for an experimental decision. | Integrate Explainable AI (XAI) tools and mandate decision logging. |
| Model Drift | Gradual degradation of model performance leads to systematically erroneous outputs. | Deploy continuous monitoring and establish triggers for model retraining [20]. |
| Training Data Bias | Results and protocols are skewed, non-representative, and not generalizable. | Conduct rigorous pre-training data audits and employ bias-detection algorithms. |
| Automation System Failure | Introduction of spurious results or complete loss of experimental data. | Design fail-safes, automated integrity checks, and comprehensive data lineage tracking. |
System Diagrams
Autonomous Experimentation AI Troubleshooting Logic
High-Throughput Data Integrity Workflow
AI Explainability Validation Protocol
Data Lifecycle Troubleshooting FAQs
Data Acquisition & Integrity
Q: My sensor data shows unexpected drift or constant values. How can I diagnose the issue?
A: Unexpected sensor readings are often related to calibration, contamination, or hardware failure. Follow this systematic approach:
- Step 1: Verify Calibration. Check the calibration status of the sensor. Re-run calibration protocols using certified reference standards. Compare current calibration curves against baseline records.
- Step 2: Inspect for Contamination. Visually inspect the sensor probe or intake for physical debris or biofilm formation. If applicable, execute a cleaning cycle according to the manufacturer's guidelines.
- Step 3: Cross-Reference with Redundant Sensors. If your system has multiple sensors measuring the same parameter (e.g., temperature, pH), compare their readings. A discrepancy can help isolate the faulty unit.
- Step 4: Check Data Logs. Review system logs for error codes, power fluctuations, or communication interrupts that coincided with the onset of the drift.
Q: How can I ensure the data generated by automated equipment is trustworthy and has not been fabricated?
A: Upholding data integrity requires a combination of technology, process, and transparency [21].
- Implement Audit Trails: Ensure all automated systems use robust, uneditable audit trails that log every action, including data point adjustments, and user logins.
- Leverage AI Responsibly: If using AI tools for data analysis, explicitly document their use, including the algorithms and data sets used for training. This is a core requirement for maintaining research integrity in the age of AI [21].
- Establish Rigorous Review: Maintain a schedule for independent, manual review of raw data and the processes that generate it to detect anomalies.
Data Processing & Transformation
Q: My data pipeline has failed during a transformation step. What is the fastest way to restore data flow?
A: The fastest resolution typically involves isolating and rerunning the failed job.
- Step 1: Check the Logs. Access the orchestration tool's logs to identify the specific transformation job that failed and the exact error message.
- Step 2: Diagnose the Cause. Common causes include invalid data formats, null values in a non-nullable field, or resource timeouts.
- Step 3: Fix and Rerun. Correct the source data issue or transformation script logic. Most modern data pipeline tools allow you to re-run the specific failed job without restarting the entire workflow.
- Step 4: Validate Output. After the job completes, run a set of validation queries or tests to ensure the data quality and integrity have been restored.
Q: An automated script for data cleaning has accidentally corrupted a dataset. How can we recover?
A: This scenario highlights the need for a mature analytics workflow with version control and reproducibility [22].
- Step 1: Halt Upstream Processes. Immediately pause any dependent processes or analyses that use the corrupted dataset to prevent the propagation of bad data.
- Step 2: Revert to a Previous Version. Use your data platform's version control system to revert the dataset to a known good state from before the corruption occurred.
- Step 3: Repair and Re-run. Fix the flawed logic in the data cleaning script. Using version-controlled assets, re-run the corrected processing job to regenerate the dataset [22].
- Step 4: Document the Incident. Record the cause of the error, the recovery steps taken, and the changes made to the script to prevent future occurrences. This practice is key to auditability [22].
AI/ML Model & Analysis
Q: The machine learning model in my experiment is producing highly inaccurate predictions after deployment. What should I check?
A: Model performance decay after deployment is often a data drift issue.
- Step 1: Compare Input Data Distributions. Analyze the statistical distribution (e.g., mean, standard deviation) of the current live data being fed to the model against the distribution of the training data. Significant differences indicate data drift.
- Step 2: Retrain the Model. If data drift is confirmed, retrain the model using a more recent, representative dataset that reflects the current live data environment.
- Step 3: Check for Concept Drift. Investigate if the underlying relationship between the input data and the target variable has changed over time, requiring a more fundamental model update.
- Step 4: Review Model Registry. Consult your model registry to ensure the correct version of the model was deployed and that all dependencies are compatible [23].
Q: An AI tool used for literature analysis generated a summary that includes fabricated citations. How do I prevent this?
A: This is a known risk of AI-generated content and a form of academic misconduct [21].
- Prevention Step 1: Mandatory Verification. Implement a lab policy that all AI-generated content, including citations, must be manually verified by a researcher against original sources before use.
- Prevention Step 2: Use Transparent Tools. Prefer AI tools that provide explanations or confidence scores for their outputs and can cite their sources.
- Prevention Step 3: Training. Participate in AI ethics and integrity training to foster an in-depth understanding of potential AI misuses, which is a recommended practice for preserving research integrity [21].
Data Insight & Reporting
Q: A collaborator cannot reproduce the analysis from my shared dataset. Where should we start looking?
A: Reproducibility issues most often stem from incomplete documentation of the analysis environment or steps.
- Step 1: Verify Data Version. Confirm your collaborator is using the exact same version of the dataset that you used.
- Step 2: Share Computational Environment. Use containerization to share the exact software environment, including operating system, library versions, and code. This is a principle of a mature analytics workflow [22].
- Step 3: Review Analysis Scripts. Walk through the analysis scripts line-by-line to ensure there are no hidden, manual steps or environment-specific paths that were not shared.
- Step 4: Document Rigorously. For future work, ensure your analysis follows the Analytics Development Lifecycle principles, which require changes to be tracked and outputs to be reproducible at any point in time [22].
Experimental Protocols & Methodologies
Protocol: Validating Sensor Data Integrity
Objective: To establish a routine procedure for verifying the accuracy and precision of sensor data in an autonomous lab environment.
Materials:
- Sensor unit under test
- Certified calibration standards (at least three points spanning the operational range)
- Data acquisition and logging system
Procedure:
- Baseline Recording: Under controlled conditions, record a 30-minute baseline from the sensor.
- Calibration Exposure: Expose the sensor to each calibration standard, allowing sufficient time for stabilization.
- Data Collection: Record the sensor output for each standard. Repeat this process three times.
- Linearity Analysis: Plot the known standard values against the mean sensor readings. Calculate the coefficient of determination.
- Precision Analysis: For each standard, calculate the standard deviation of the sensor readings.
- Acceptance Criteria: The sensor passes if is greater than 0.98 and the standard deviation at each point is less than 1% of the measurement range.
Protocol: Establishing a Data Pipeline for an Autonomous Experiment
Objective: To create a reliable, version-controlled data pipeline that transforms raw sensor data into a clean, analysis-ready dataset.
Materials:
- Raw data source
- Data transformation tool
- Version control system
- Computational environment
Procedure:
- Ingestion: Configure the pipeline to automatically ingest new raw data files upon experiment completion.
- Cleaning: Apply transformation scripts to handle missing data, remove outliers, and standardize formats.
- Versioning: Upon successful transformation, commit the new dataset and the transformation scripts to a version control system.
- Validation: Run automated data quality checks to validate that key metrics fall within expected ranges.
- Publication: Make the versioned, clean dataset available to authorized researchers and analytical systems.
Data & AI Lifecycle Workflow
The following diagram illustrates the core stages of the data lifecycle within an autonomous lab, highlighting the critical gates for data integrity checks.
Table 1: AI-Generated Content Risk Classification and Mitigation
| Misconduct Type | Severity | Common Motivations | Recommended Mitigations |
|---|---|---|---|
| Data Fabrication | High | Publication pressure, pursuit of prestige | Independent data audit trails, raw data review [21] |
| Content Plagiarism | Medium-High | Shortening research cycles, increasing output | Use of plagiarism detection software, mandatory citation of AI tools [21] |
| Opacity of Results | Medium | Protecting research advantages, technological secrecy | Enforcement of disclosure standards for AI use in methodologies [21] |
Table 2: Essential Research Reagent Solutions for Autonomous Experimentation
| Reagent / Material | Primary Function | Key Considerations for Data Integrity |
|---|---|---|
| Certified Calibration Standards | To provide a known reference for validating sensor accuracy. | Must be traceable to international standards; requires regular expiry checks. |
| Data Pipeline Orchestrator | To automate and manage the flow of data between systems. | Must have built-in logging, error handling, and versioning capabilities [23]. |
| Model Registry | To manage, version, and track the lineage of ML models. | Essential for reproducibility and auditability of AI-driven insights [23]. |
| Version Control System | To track changes in datasets, code, and analysis scripts. | Foundation for collaboration, reproducibility, and rollback capabilities [22]. |
Building a Bulletproof System: Methodologies for Data Integrity by Design
Data Management FAQs
What is a data dictionary and why is it critical for autonomous research?
A data dictionary is a centralized repository that defines and standardizes data elements, such as tables, fields, data types, and business rules, ensuring all researchers have a shared understanding of the data [24]. In autonomous experimentation, it is crucial for maintaining data integrity—the accuracy, consistency, and reliability of data throughout its lifecycle [19]. It prevents miscommunication and errors by providing precise descriptions for all data elements, which is foundational for credible and reproducible research findings [25] [24] [19].
What is the difference between a passive and an active data dictionary?
The key difference lies in how they are updated and synchronized with the data source [24].
- Passive Data Dictionary: Requires manual updates and does not automatically sync with the database. It is suitable for small-scale or static systems.
- Active Data Dictionary: Automatically syncs with the database in real-time, reflecting any changes in the schema or metadata instantly. It is essential for dynamic research environments with frequent data changes.
Table: Comparison of Data Dictionary Types
| Feature | Passive Data Dictionary | Active Data Dictionary |
|---|---|---|
| Update Mechanism | Manual updates | Automatic, real-time sync with the database |
| Best For | Small-scale systems, legacy systems, static databases | Dynamic environments with frequent schema changes (e.g., SaaS, financial institutions) |
| Example | A spreadsheet managed by a data administrator [24] | Built-in system views in SQL Server (e.g., sys.tables) [24] |
| Maintenance Overhead | High | Low |
What are the most common threats to data integrity in a lab environment?
Labs face several challenges that can jeopardize the accuracy and reliability of their data [19]:
- Manual Data Entry Errors: Transcription mistakes from handwritten notes or manual input.
- Data Fragmentation: Disconnected systems and siloed datasets make it difficult to maintain consistent and accessible information.
- Unauthorized Access: Lack of proper access controls can lead to unauthorized data modification.
- Outdated Systems: Legacy software and paper-based methods lack the security, precision, and scalability needed for modern labs.
- Compliance Risks: Manual processes make it challenging to meet regulatory standards like FDA 21 CFR Part 11.
How can digital tools help safeguard data integrity?
Digital solutions like Electronic Lab Notebooks (ELNs) and Laboratory Information Management Systems (LIMS) address common data integrity risks by providing [19]:
- Centralization of Data: A single, unified platform eliminates data silos and ensures coherence.
- Automation and Precision: Automated workflows and data logging reduce human error.
- Real-time Tracking: Enables monitoring of data and processes as they happen.
- Access Control and Security: Role-based access and encryption protect sensitive information.
- Audit Readiness: Built-in audit trails automatically log all data interactions for transparent compliance.
Troubleshooting Guides
Guide 1: Resolving Inconsistent Data Definitions Across Teams
Symptoms: Researchers report conflicting results, datasets from different groups cannot be easily combined, and reports contain errors due to misinterpretation of data fields.
Investigation and Resolution:
- Understand the Problem: Identify the specific data fields (e.g., "sample_id," "concentration") causing confusion. Gather examples of inconsistent usage from reports or code [26] [27].
- Isolate the Issue: Form a cross-functional team with members from each affected group. Discuss the differing definitions and identify the root cause, which is often a lack of centralized documentation [25] [24].
- Implement the Solution: Create or update a shared data dictionary.
- Define Key Components: For every critical data element, document the attributes in the table below [24].
- Establish Governance: Assign a data steward to manage the dictionary and establish a process for regular reviews and updates [25] [24].
- Promote Adoption: Train all users on how to access and use the dictionary and integrate it into existing workflows [25].
Table: Essential Components for Data Dictionary Entries
| Component | Description | Example |
|---|---|---|
| Field Name | The precise name of the data element. | patient_age |
| Data Type | The format of the data. | integer |
| Field Description | A clear explanation of the field's purpose. | "Stores the patient's age at time of enrollment in whole years." |
| Business Rules | Constraints or validations for the data. | "Must be a positive integer between 18 and 99." |
| Default Value | A value used if no input is provided. | NULL |
Guide 2: Troubleshooting Poor Data Quality in Automated Pipelines
Symptoms: An automated data pipeline runs without errors, but the output data contains unexpected null values, incorrect formats, or values outside plausible ranges.
Investigation and Resolution:
- Understand the Problem: Examine the pipeline's output data. Identify specific records and fields that are incorrect. Reproduce the issue by running the pipeline on a small, test dataset [26].
- Isolate the Issue: This process involves systematically checking each stage of the data pipeline.
- Implement the Solution: The fix will depend on the isolated cause.
- If source data has changed: Update the extraction logic or data validation rules at the point of entry to handle the new format [19].
- If transformation logic is flawed: Correct the script or query. Refer to the data dictionary to ensure business rules for data types and value ranges are correctly implemented [24].
- Implement proactive checks: Introduce data validation checks within the pipeline to flag quality issues automatically, preventing future occurrences [19].
Guide 3: Addressing a Lack of Data Transparency and AI-Assisted Research Misconduct
Symptoms: Research results generated with AI assistance cannot be reproduced, methodologies are opaque, or there is suspicion of AI-generated fictitious data or text [21].
Investigation and Resolution:
- Understand the Problem: Review the research documentation. Is the use of AI clearly disclosed? Are the AI algorithms, training data, and parameters fully described? Is the data source verifiable? [21]
- Isolate the Issue: Determine the specific form of opacity or misconduct.
- Lack of disclosure: AI tools were used but not reported in the methodology.
- Algorithmic opacity: The AI's decision-making process is a "black box."
- Data fabrication/falsification: AI used to generate realistic but fictitious datasets or text [21].
- Implement the Solution:
- Enforce Guidelines: Develop and enforce comprehensive AI research integrity guidelines that mandate clear disclosure of AI use, protocols for data analysis, and documentation of AI models [21].
- Mandate Training: Provide mandatory AI ethics and integrity training for all researchers [21].
- Promote Transparency: Use digital tools that provide detailed audit trails for all data-related actions, including those involving AI [19].
The Scientist's Toolkit
Table: Essential Research Reagent Solutions for Data Integrity
| Item | Function |
|---|---|
| Laboratory Information Management System (LIMS) | A digital platform that centralizes sample and data management, standardizing workflows and tracking data lineage [19]. |
| Electronic Lab Notebook (ELN) | Replaces paper notebooks to ensure accurate, real-time data logging, prevents manual entry errors, and creates an immutable record [19]. |
| Data Dictionary | A centralized repository of data definitions that ensures all researchers use consistent terminology, upholding data consistency and clarity [25] [24]. |
| Access Control System | Security protocols that restrict data access based on user roles, preventing unauthorized modification and protecting sensitive information [19]. |
| Audit Trail Software | Automatically logs every action taken on a piece of data, providing a transparent record for troubleshooting, replication, and regulatory audits [19]. |
For researchers in autonomous experimentation, the integrity of your data supply chain is foundational to credible results. This guide provides practical, troubleshooting-focused advice on using verifiable sources and tamper-evident logs to protect your data from its origin through every stage of analysis, ensuring the reliability of your scientific findings [28].
Frequently Asked Questions (FAQs)
FAQ 1: What is a tamper-evident log and how does it protect my research data? A tamper-evident log is a cryptographically secured, append-only record that stores an accurate, immutable, and verifiable history of activity [28]. In an autonomous lab, it protects your data by making it impossible for anyone—including a malicious insider—to alter, delete, or backdate any recorded event without detection [28]. Think of it as a CCTV system for your data; it records everything that happens, providing an indelible audit trail [29].
FAQ 2: My automated instrument outputs data in a proprietary format. How can I make this data verifiable? The first step is to ensure the integrity of the data at the point of generation. You can do this by creating a cryptographic hash (a digital fingerprint) of the raw data file immediately upon creation. This hash should then be immediately sent to a tamper-evident log [30] [28]. Later, anyone can verify the data's integrity by re-calculating the hash of the file and comparing it to the immutable record in the log. Standardizing data formats across instruments, while ideal, is not a prerequisite for this method [30].
FAQ 3: What's the difference between a log being "tamper-evident" and "tamper-proof"? "Tamper-evident" is the correct term. These systems are not impossible to tamper with, but any tampering will be detectable [31]. If an entry in the log is changed, the cryptographic hashes will not align, and it becomes impossible to provide valid proofs of consistency and inclusion, exposing the malicious activity [29] [31]. A "tamper-proof" system is a theoretical concept, whereas "tamper-evident" provides a practical and high level of security.
FAQ 4: Who is responsible for verifying the contents of a transparency log? While the log itself cryptographically proves that data hasn't changed (integrity), it doesn't prove that the data was correct in the first place (accuracy) [29]. The responsibility for verifying the meaning and correctness of the logged entries—a process often called "verification"—falls to the relevant stakeholders [29]. In a research context, this could be:
- The Principal Investigator verifying that a logged experimental protocol matches the intended design.
- A Collaborating Lab confirming that a dataset received for analysis is identical to the one logged by the originator.
- An Automated Script checking that a container image hash logged in the system matches the one being deployed in a data analysis workflow.
FAQ 5: We use many third-party data sources and AI models. How do we manage this supply chain risk? The reliance on external data and models introduces significant risk [32]. Key mitigation strategies include:
- Vet Suppliers Carefully: Only use trusted sources and regularly audit their security posture [32].
- Inventory Everything: Maintain a Software Bill of Materials (SBOM) or AI BOM for all third-party components, including pre-trained models and datasets [32].
- Verify Model Integrity: Use third-party tools to check file hashes and signatures for pre-trained models to ensure they have not been altered [32].
- Conduct AI Red Teaming: Perform extensive evaluations and adversarial testing on third-party models before integrating them into your research pipeline [32].
Troubleshooting Guides
Issue 1: Suspected Data Tampering or Inconsistency
This guide helps you investigate when experimental results are inconsistent and data integrity is in question.
Step-by-Step Investigation:
- Identify the Data in Question: Pinpoint the specific dataset, file, or record causing concern.
- Locate the Cryptographic Proof: Retrieve the inclusion proof and the signed tree head (checkpoint) for the data's entry in the tamper-evident log. This is typically done via the log's API [29].
- Recompute the Data Hash: Generate a new cryptographic hash of the data you currently have.
- Verify the Proof: Use the log's verification tooling to check two things:
- Compare Hashes: Compare the newly computed hash against the one stored in the log.
- Interpret the Results:
- Hashes Match & Proofs are Valid: The data is intact and has not been altered.
- Hashes Do Not Match: The content of the data has been changed. The tamper-evident log provides cryptographic evidence of this alteration.
- Proofs are Invalid: The structure of the log itself is suspect, indicating a potential compromise of the log server [29].
Issue 2: Failure to Integrate Instrument with Data Logging System
When a new automated instrument (e.g., a plate reader or sequencer) cannot successfully log data to your verifiable system.
Troubleshooting Checklist:
| Phase | Check | Action |
|---|---|---|
| Connection | Network connectivity to the logging server. | Verify ping/network access from the instrument's control PC. |
| Authentication & API credentials. | Ensure the service account has the correct "append" permissions for the log. | |
| Data Format | Data serialization format. | Check that the data is being serialized (e.g., as JSON) correctly before hashing. |
| Hash calculation input. | Confirm the hash is calculated on the exact byte sequence that represents the data. | |
| Log Server | Log server status. | Check the server's health dashboard or logs for outages. |
| Rate limiting. | Ensure your script is not hitting API rate limits; implement retry logic. |
Issue 3: High Latency in Automated Data Verification Slowing Down Experiments
When the process of logging and verifying data creates a bottleneck in a high-throughput autonomous experimentation workflow.
Potential Solutions and Diagnostics:
- Diagnose: Is the latency from the network or the processing?
- Network Latency: The time to send data to a cloud-based log and receive proofs.
- Processing Latency: The time to generate the hash or verify complex proofs.
- Solution 1 → Implement Edge Logging: Deploy a local, on-premises tamper-evident log node for your lab. This brings the logging service closer to your instruments, drastically reducing network latency [30]. The local node can then be periodically synchronized with a central cloud log for cross-lab verification.
- Solution 2 → Optimize Verification Frequency: Instead of verifying every single data point in real-time, batch process the verification for higher throughput. For example, log hashes of individual data files immediately but run consistency proofs on the entire log at regular intervals (e.g., hourly).
Experimental Protocols
Protocol 1: Establishing a Baseline for Data Source Verifiability
Objective: To cryptographically verify the provenance and integrity of a third-party dataset before use in an experiment.
Materials:
- Third-Party Dataset: The data obtained from an external provider.
- Provider's Public Key: For verifying digital signatures.
- Tamper-Evident Log System: Such as a Trillian instance [28].
- Command-Line Tooling:
curl,openssl.
Methodology:
- Obtain the Data and Manifest: Download the dataset and its accompanying manifest file, which should contain the cryptographic hash of the dataset and be digitally signed by the provider.
- Verify the Provider's Signature: Use the provider's public key to verify the signature on the manifest.
openssl dgst -verify provider_pub.pem -keyform PEM -signature manifest.sha256 manifest.json
- Hash the Dataset: Generate a SHA-256 hash of the downloaded dataset.
sha256sum dataset.csv
- Compare Hashes: Ensure the hash you computed matches the one in the now-trusted manifest.
- Log the Hash for Future Proof: Submit the hash to your internal tamper-evident log. This establishes a verifiable point-in-time record that you received this specific dataset.
Diagram: Third-Party Data Verification Workflow
Protocol 2: Implementing Tamper-Evident Logging for an Automated Experiment
Objective: To create a secure, immutable audit trail for all data generated by an autonomous experimental workflow.
Materials:
- Automated Instrument: e.g., HPLC, NGS sequencer.
- Instrument Control PC: Runs the data logging script.
- Logging Client API: Libraries to interact with the tamper-evident log (e.g., Trillian client [28]).
Methodology:
- Define Loggable Events: Identify key events in your workflow (e.g., "Run Started," "Raw Data File Saved," "Analysis Complete").
- Develop Logging Script: On the control PC, create a script that:
- Monitors the instrument's output directory for new files.
- Upon file creation, generates a SHA-256 hash of the file.
- Structures a log entry containing:
{timestamp, instrument_id, experiment_id, event_type, file_hash}. - Submits this entry to the tamper-evident log and retrieves the inclusion proof.
- Store Proofs Securely: Save the received inclusion proofs and signed tree heads in a secure, separate location from the raw data.
- Verify at Analysis Stage: Before analyzing a data file in your pipeline, recompute its hash and verify the inclusion proof against the latest signed tree head.
Diagram: Automated Experimental Data Logging
The Scientist's Toolkit: Essential Research Reagents & Solutions
This table details key digital "reagents" and tools essential for building a verifiable data supply chain.
| Item | Function / Explanation |
|---|---|
| Cryptographic Hash (e.g., SHA-256) | Creates a unique, fixed-size digital fingerprint for any data file. Used to detect any changes to the data [28]. |
| Digital Signatures | Allows a trusted entity (e.g., a data provider) to cryptographically sign a hash, proving the data's origin and integrity [32]. |
| Tamper-Evident Log (e.g., Trillian) | An append-only database that uses a Merkle tree to store hashes, enabling efficient and verifiable inclusion and consistency proofs [28] [31]. |
| Inclusion Proof | A compact, cryptographic proof that a specific entry is included in the log at a specific position [29] [31]. |
| Consistency Proof | A proof that a newer version of the log contains all the entries of an older version, proving its append-only nature [29] [31]. |
| Software Bill of Materials (SBOM) | A nested inventory of all software/components, critical for tracking third-party dependencies and associated vulnerabilities in your analysis pipeline [32]. |
Troubleshooting Guides
Audit Trail Issues
Problem: Incomplete or Missing Audit Trail Entries
- Symptoms: Actions by users or instruments are not recorded; chronological records have gaps; regulators flag missing data history.
- Diagnosis: This is often caused by incorrect system configuration. The audit trail functionality might be disabled, or the system may not be validated to ensure it captures all required events [33] [34].
- Solution:
- Verify System Validation: Confirm that the computerized system (e.g., LIMS, ELN) has been properly validated for its intended use, with specific testing of audit trail functionality [33].
- Review Configuration Settings: Check that audit trail logging is enabled for all critical data events, including creation, modification, and deletion of electronic records [35].
- Implement Automated Capture: Ensure logs are generated automatically by the system, not manually by users, to meet regulatory requirements for contemporaneous recording [34].
Problem: Audit Trail is Not Tamper-Evident
- Symptoms: Log entries can be modified or deleted by users or system administrators; the integrity of the data history is questionable.
- Diagnosis: The storage system for the audit trail lacks necessary security controls, such as immutability features [34].
- Solution:
- Utilize Immutable Storage: Implement Write-Once-Read-Many (WORM) technology or object lock policies on cloud storage to prevent the alteration or deletion of audit logs after they are written [34].
- Enforce Strict Access Controls: Restrict administrative access to audit logs. No user should have permissions to edit or delete log entries [35].
- Employ Cryptographic Hashing: Use digital fingerprints (hashes) for audit log files. Any change to the log file will change the hash, making tampering evident [34].
Raw Data Management Issues
Problem: Raw Data is Not Attributable
- Symptoms: Data entries cannot be traced back to a specific person or instrument; the "who" in the data history is missing.
- Diagnosis: The system uses shared logins or lacks integration with a robust user authentication service [33] [35].
- Solution:
- Assign Unique User Credentials: Eliminate shared accounts. Every individual must have a unique login ID [35].
- Implement Electronic Signatures: Where required, use electronic signatures that are legally binding and clearly link the user to a specific action or record [33].
- Integrate with Instrument IDs: Ensure automated data capture from instruments records the specific instrument ID alongside the data [34].
Problem: Raw Data is Not Readily Available or Retrievable
- Symptoms: Data cannot be found quickly for analysis or regulatory inspection; archived data is difficult to restore.
- Diagnosis: Inconsistent file naming conventions, poorly organized directory structures, or inadequate data archiving and retrieval procedures [36].
- Solution:
- Establish a Clear Data Lifecycle Policy: Define and enforce standards for data naming, storage locations, and archiving schedules [33].
- Implement a Robust Archiving System: Use systems designed for long-term data retention that protect data integrity and ensure readability for the entire retention period [34].
- Regularly Test Data Retrieval: Periodically restore data from archives to verify that processes work and data remains usable [35].
Version Control Issues
Problem: Unauthorized Changes to Controlled Documents or Methods
- Symptoms: Standard Operating Procedures (SOPs) or analytical methods are changed without proper approval; multiple, conflicting versions of a document are in circulation.
- Diagnosis: Weak change control processes and a lack of formal versioning in document management systems [35].
- Solution:
- Implement a Formal Change Control Process: Require documented requests, impact assessments, and approvals for all changes to controlled documents [34].
- Use a Version-Controlled Document Management System: Utilize an Electronic Document Management System (EDMS) that automatically versions documents and requires a check-in/check-out process [34].
- Maintain Version History: Ensure the system preserves a complete history of all previous versions, including what was changed, by whom, and why [36].
Frequently Asked Questions (FAQs)
1. What is the primary purpose of an audit trail in a research setting? The primary purpose is to provide a secure, chronological, and tamper-proof record of all events and changes made to electronic data [33]. It ensures data integrity and accountability for regulatory compliance by meticulously logging who did what, when, and why [33] [34].
2. Our team uses a shared drive to store data. How can we improve version control? While shared drives lack built-in version control, you can implement stricter manual processes:
- Enforce a File Naming Convention: Include version numbers (e.g.,
SOP_Anayltical_Method_v2.1) and the date in all filenames. - Centralize a Master Log: Maintain a single, version-controlled spreadsheet that tracks the current version of every document, the date of change, and the person who made the change. For a more robust solution, invest in a Laboratory Information Management System (LIMS) or Electronic Document Management System (EDMS) with automated version control [33] [34].
3. What are the essential components that every audit trail record must include? A compliant audit trail record must capture [35] [34]:
- User Identification: The unique ID of the person who performed the action.
- Accurate Timestamp: The exact date and time of the action.
- Action Description: What was done (e.g., created, modified, deleted).
- Reason for Change: The justification for the modification, where required.
4. How often should audit trails be reviewed, and by whom? Audit trails should be reviewed regularly as part of data verification processes. The frequency should be risk-based, with critical data requiring more frequent review (e.g., concurrently with the data being reviewed) [33] [35]. The review should be conducted by someone independent of the data generation process, such as a study director or quality assurance personnel [33].
5. What is the difference between data integrity and data quality?
- Data Integrity focuses on the trustworthiness and traceability of data throughout its lifecycle, ensuring it is complete, consistent, and accurate in a regulatory context (ALCOA+ principles) [33] [36].
- Data Quality is a broader concept that measures the fitness for use of data, often assessed across dimensions like completeness, timeliness, and validity [36]. High data integrity is a prerequisite for reliable data quality.
Data Presentation: Data Quality Dimensions and Metrics
The following table summarizes the key dimensions used to measure and monitor data quality in a regulated research environment [36].
| Data Quality Dimension | Description | Example Metric / Formula |
|---|---|---|
| Completeness | Does the data include all essential information without missing values? | Error Density = (Number of records with missing values / Total records) × 100% [36] |
| Timeliness | Is the data up-to-date and delivered without delays that impact its usefulness? | Data Freshness: Time elapsed between data generation and availability for analysis. |
| Validity | Does the data adhere to the correct format and predefined validation rules? | Error Count: Number of records that fail format validation rules (e.g., incorrect date format) [36] |
| Accuracy | Does the data accurately reflect the real-world object or event it represents? | Requires verification against a known trusted source. |
| Consistency | Is the data uniform and consistent across different sources and systems? | Number of anomalies or outliers flagged by data observability platforms [36] |
| Uniqueness | Are there duplicate records within the dataset? | Duplicate Rate = (Number of duplicate records / Total records) × 100% |
Experimental Protocol: Implementing a Automated Data Quality Check
Objective: To embed automated data quality validation within a data pipeline to ensure only high-quality, compliant data is propagated to downstream analysis systems.
Materials:
- Data source (e.g., output from an analytical instrument).
- Data pipeline orchestration tool (e.g., Apache Airflow, Nextflow).
- Data quality testing framework (e.g., open-source library or custom scripts).
- Storage destination (e.g., database, data lake).
Methodology:
- Define Validation Rules: Based on the data quality dimensions, specify rules for incoming data. For example: checks for non-null values (completeness), checks for values within a plausible range (validity), and checks for correct data format (validity) [36].
- Integrate Check into Pipeline: Code the validation rules and embed them as a step in the data pipeline, immediately after data ingestion and before any transformation or loading.
- Configure Failure Handling: Define the pipeline's behavior if data fails validation. Options include:
- Halt the Pipeline: Stop execution and trigger an alert to data engineers/scientists.
- Quarantine Failed Data: Route invalid records to a separate location for investigation and correction.
- Log Validation Results: For every pipeline run, the system must generate a structured log containing [36]:
- Timestamp of the check.
- Dataset name and identifier.
- Number of records checked.
- Number of records that passed/failed.
- Detailed list of failed records and the specific rule they violated.
- Review and Refine: Periodically review the validation results and failure logs to identify systematic data quality issues and refine the rules as needed.
Workflow Visualization
The Scientist's Toolkit: Research Reagent Solutions
| Item | Function in Data Integrity |
|---|---|
| Laboratory Information Management System (LIMS) | Automates sample and data management, centralizes data storage, and inherently generates comprehensive, compliant audit trails for every action [33]. |
| Electronic Lab Notebook (ELN) | Provides a structured digital environment for recording experimental procedures and observations, ensuring they are attributable, contemporaneous, and original [33] [34]. |
| Chromatography Data System (CDS) | Specialized software for capturing raw analytical data and instrument parameters, typically with integrated and validated audit trail functionalities [33]. |
| Data Quality Platform | A dedicated software tool used to define, schedule, and regularly re-evaluate data quality checks across datasets, tracking health scores and generating validation records [36]. |
| Immutable Storage (WORM) | Write-Once-Read-Many storage technology prevents the alteration or deletion of data and audit logs after they are written, providing a tamper-evident foundation [34]. |
For researchers and drug development professionals, the shift towards autonomous experimentation places unprecedented importance on data integrity. This technical support center provides targeted guidance for implementing two foundational technologies that address this challenge: blockchain for unalterable traceability and artificial intelligence (AI) for real-time quality control. These tools are critical for creating a verifiable chain of custody for experimental materials and ensuring the consistency and accuracy of automated processes. The following guides and FAQs address specific, common technical issues encountered when integrating these systems into a research environment, helping to ensure that your autonomous research data is secure, verifiable, and trustworthy.
Technical Support: Blockchain for Drug Traceability
This section assists researchers in implementing blockchain technology to create an immutable record for experimental materials, crucial for audit trails and provenance verification.
Troubleshooting Guide: Common Blockchain Implementation Issues
| Problem | Possible Cause | Solution |
|---|---|---|
| High Gas Fees/Transaction Costs | Congested network; Complex smart contract operations. | Optimize smart contract code to reduce computational steps. Consider using a permissioned blockchain like Hyperledger Fabric which typically has lower costs [37]. |
| "Data Not Final" Error | Network latency; Lack of consensus among nodes. | Wait for additional block confirmations. Ensure your node is synchronized with the network. For instant finality, use a framework with a finality mechanism [38]. |
| Smart Contract Execution Failed | Insufficient gas; Bug in contract logic; Condition not met. | Debug contract in a test environment (e.g., Remix IDE). Simulate transactions with sufficient gas limits before mainnet deployment [38]. |
| Cannot Verify Drug Provenance | Off-chain data tampering; Incorrect query function. | Verify the hash of off-chain data (e.g., stored on IPFS) against the on-chain hash. Double-check the smart contract's view function for querying provenance [37] [39]. |
| Low Throughput (Transactions/Second) | Blockchain's inherent scalability limits. | Implement on-chain/off-chain storage hybrids. Use sidechains for less critical data to reduce main chain load [37]. |
FAQ: Blockchain Traceability
Q: How does blockchain truly prevent counterfeit drugs in a research supply chain? A: Blockchain prevents counterfeiting by creating a secure, immutable lineage. Each batch receives a unique digital ID recorded on the blockchain. Every transfer or action (e.g., change of custody, temperature check) is a timestamped, tamper-proof transaction. Before use, a researcher can scan a QR code to verify the entire history. Any attempt to introduce a counterfeit item would fail because it would lack a verifiable history on the chain, which is secured by cryptographic hashes and consensus mechanisms [39] [40].
Q: We handle sensitive clinical data. How can we use a transparent blockchain and still comply with HIPAA/GDPR? A: Use a permissioned blockchain (e.g., Hyperledger Fabric) where access is controlled. Sensitive data itself should not be stored on-chain. Instead, store only cryptographic hashes of the data on-chain, while keeping the raw data in secure, access-controlled off-chain storage. This method provides a verifiable integrity check without exposing private information, helping to meet "right to be forgotten" mandates [37] [39].
Q: What is the role of a "smart contract" in my material traceability system? A: A smart contract automates governance and compliance. It is self-executing code that enforces predefined rules. For example, a smart contract can:
- Automatically halt the distribution of a reagent if a connected IoT sensor reports a temperature excursion.
- Prevent a material from being used in an experiment if it has passed its expiration date.
- Automatically log a compliance event for an audit trail [39].
Q: Our experiments generate huge amounts of sensor data. Can we store it all on-chain? A: No. Storing large datasets on-chain is impractical and expensive. A standard practice is a hybrid on-chain/off-chain approach. Store the raw sensor data in efficient off-chain systems (e.g., a cloud database or decentralized storage like IPFS). Then, calculate a cryptographic hash of that data and store that hash on the blockchain. This provides an immutable proof that the data has not been altered, without overloading the chain [37].
Technical Support: AI for Quality Control
This section provides support for deploying AI-based quality control systems, which are essential for maintaining consistent and reliable data generation in automated experiments.
Troubleshooting Guide: AI Quality Control Models
| Problem | Possible Cause | Solution |
|---|---|---|
| High False Positive Defect Rate | Biased or insufficient training data; Incorrect sensitivity threshold. | Augment training dataset with more "good product" images and varied defect examples. Adjust the model's classification confidence threshold. |
| Model Fails to Detect New Defect Types | Static model; Lack of continuous learning. | Implement a human-in-the-loop (HITL) feedback system where experts label new defects. Use this data to periodically retrain the model [41] [42]. |
| Decreasing Model Performance Over Time | Concept drift (changes in input data distribution). | Employ concept drift detection algorithms. Schedule periodic model retraining with recent production data to adapt to new patterns [41]. |
| Inability to Handle Real-Time Data Streams | Model too computationally heavy; Inefficient data pipeline. | Optimize the model for edge deployment (e.g., model quantization). Use stream-processing frameworks (e.g., Apache Kafka) for efficient data handling [41]. |
| "Black Box" Model Lacks Interpretability | Use of complex deep learning models. | Integrate Explainable AI (XAI) techniques like LIME or SHAP to highlight image features that led to a defect classification, building trust with stakeholders [6]. |
FAQ: AI Quality Control
Q: How can an AI system predict a defect before it happens? A: AI moves from detection to predictive maintenance. Machine learning models analyze historical production data (sensor readings, process parameters, past defect patterns) to identify correlations. For instance, the model might learn that a specific, subtle vibration pattern in a pill press precedes a structural defect in tablets by several hours. This allows researchers to intervene and adjust parameters proactively, minimizing waste and downtime [42].
Q: What are the critical data requirements for building an effective AI QC model? A: The key is large volumes of high-quality, labeled data. You need thousands of images or sensor data readings that are accurately labeled (e.g., "good," "crack," "discoloration"). The data must be representative of all possible variations in your production process and defects. Poor data quality is the most common cause of AI project failure; thus, well-organized, labeled, and standardized data is essential [43] [42].
Q: Can AI handle complex defects that are difficult for human inspectors to define? A: Yes. This is a key strength of AI. Machine learning algorithms, particularly deep learning, excel at identifying complex patterns and anomalies across large datasets. The AI can learn to detect defects caused by the interaction of multiple variables—a task that is extremely difficult for rule-based systems or humans to program explicitly. It identifies the "fingerprint" of a defect without being explicitly told what to look for [42].
Q: How do we ensure the AI's decisions are trustworthy for regulatory purposes? A: Implement robust data integrity and model governance frameworks. This includes:
- Data Lineage: Tracking the origin and transformation of all data used to train and run the model.
- Model Audit Trails: Maintaining immutable records of model versions, training data, and performance metrics.
- Explainable AI (XAI): Using methods that provide reasons for the AI's decisions, making its output interpretable for auditors [6] [1].
Integrated Architecture & Workflow
This section provides a visual overview of how blockchain and AI systems integrate within an autonomous research environment to ensure end-to-end data integrity.
System Integration Diagram
The diagram below illustrates the logical flow and components of an integrated system where AI performs quality control and blockchain immutably records the data and actions.
Data Flow for Integrity Assurance
The sequence below details the technical steps corresponding to the workflow diagram, highlighting how data integrity is maintained from acquisition to action.
- Data Acquisition: An experimental drug batch is processed, with IoT sensors and machine vision systems capturing real-time quality data (e.g., tablet hardness, solution clarity) [43] [39].
- AI Analysis & Decision: The AI quality control model analyzes the incoming sensor data stream. It classifies the batch as "Pass" or "Fail" based on trained defect patterns and may also predict future failures [42].
- Smart Contract Execution: The QC result is sent to a pre-defined smart contract. The contract code automatically executes based on this input [39].
- Autonomous Action & Immutable Logging:
- The smart contract triggers an autonomous action, such as approving the batch for the next experiment or rejecting it and alerting a scientist [39].
- A cryptographic hash of the critical data (e.g., batch ID, QC result, timestamp) is computed and recorded as a transaction on the blockchain ledger, creating a permanent, tamper-proof audit trail [37] [6].
The Scientist's Toolkit: Research Reagent & Material Solutions
The table below lists essential digital and physical components for setting up a traceable and AI-driven quality control system for experimental materials.
| Item | Function in the Context of Traceability & QC |
|---|---|
| Permissioned Blockchain Framework (e.g., Hyperledger Fabric) | Provides the decentralized ledger backbone for traceability, offering confidentiality, access control, and higher performance than public networks for enterprise research use [37]. |
| Smart Contract Code (e.g., Solidity, Go) | The business logic that automates material handling rules, compliance checks, and data logging, ensuring consistent and unbiased protocol execution [38] [39]. |
| Cryptographic Hash Function (e.g., SHA-256) | Generates a unique digital fingerprint for any piece of data (e.g., a COA file). Storing this hash on-chain proves the data's integrity without storing the data itself [37] [6]. |
| IoT Sensors (Temperature, Humidity) | Monitor critical environmental parameters of material storage conditions in real-time. This data feeds both AI models for analysis and smart contracts for compliance [39]. |
| Machine Vision Camera System | Captures high-resolution images of materials (e.g., tablets, cultures) for the AI model to inspect for visual defects, contaminants, or morphological changes [43] [42]. |
| Decentralized Storage (e.g., IPFS) | Stores large, immutable data files (e.g., full experiment logs, high-res images) off-chain while allowing their integrity to be linked to the blockchain via hashes [37]. |
Troubleshooting Guides
Guide 1: Resolving Data Lineage Gaps in Complex Pipelines
Problem: Your automated experiment generates unexpected outputs, and you cannot trace which data sources or transformations contributed to the result. This is often caused by incomplete data lineage.
Symptoms:
- Inability to identify the origin of anomalous data points in experimental results.
- Lack of visibility into how data flows between instruments, transformation scripts, and analytical models.
- Difficulty assessing the impact of changing a data source on downstream experiments.
Investigation Steps:
- Identify the Breakpoint: Pinpoint the specific dataset, table, or metric where the unexpected output first appears [44].
- Trace Upstream: Work backward from the problematic output. Manually check the scripts, queries, or tools that directly feed into it [45].
- Check for Black Boxes: Identify any components in your pipeline that do not automatically expose lineage metadata, such as legacy instruments, custom scripts, or third-party APIs [44].
- Verify Granularity: Confirm whether your lineage tracking is at the table-level or the more precise column-level. Table-level lineage might not show which specific data fields are causing the issue [44].
Resolution Actions:
- Implement Automated Lineage Tools: Deploy tools that automatically capture lineage by parsing SQL queries, ETL scripts, and API calls [45]. For open-source options, evaluate tools like OpenMetadata or Marquez, which can integrate with various data platforms [46].
- Augment with Manual Mapping: For components that lack automated tracking, manually document the data flows using a no-code editor if your tool supports it, or add annotations directly in the code [46] [45].
- Establish Granular Lineage: Ensure your lineage solution tracks dependencies at the column level, not just the table level. This is essential for precise root cause analysis [44].
The following diagram illustrates the logical workflow for investigating and resolving data lineage gaps:
Guide 2: Debugging a Model Due to Undocumented Assumptions
Problem: An AI/ML model used in your experiment performs well in validation but fails in production. The failure is traced to an invalid assumption made during model development that was not documented.
Symptoms:
- Model performance degrades significantly when applied to new data from a slightly different context.
- Disagreement among team members about the appropriate use cases for the model.
- Inability to explain why a model generates a specific prediction during peer review or validation.
Investigation Steps:
- Review Model Context: Re-examine the model's purpose and its intended operational environment [47].
- Audit Data Sources: Scrutinize the training data for hidden biases, data quality issues, or contextual factors that were assumed to be constant [47] [48].
- Interview Stakeholders: Talk to the model's developers and intended users to uncover implicit assumptions about data distributions, feature relationships, or operational constraints.
Resolution Actions:
- Formalize Model Documentation: Create a standardized model document that explicitly records assumptions, intended use, and known limitations [47].
- Implement a "Living Document" Process: Treat model documentation as a dynamic artifact. Update it every time the model is retrained or when a significant assumption changes [47].
- Integrate Documentation into Workflow: Use tools like Model Cards or integrated platforms (e.g., Weights & Biases) to weave documentation directly into the model development and deployment lifecycle [47].
Guide 3: Addressing Data Integrity Risks from Real-Time Sensor Data
Problem: An autonomous experiment relies on real-time sensor data (IoT), but you suspect that transient data corruption or latency is affecting the experiment's outcome and integrity.
Symptoms:
- Unexplained outliers in data streams from environmental sensors or instrument monitors.
- Experiments failing when cloud connectivity is lost, disrupting data flow.
- Inability to validate that experimental conditions (e.g., temperature, pressure) were maintained throughout the run.
Investigation Steps:
- Inspect Data Provenance: Check the metadata for sensor readings to verify the data source, timestamp accuracy, and collection method [30].
- Analyze Network Dependencies: Determine if the experiment's control logic depends on a continuous cloud connection for processing data, which introduces latency and failure risk [30].
- Check for Data Validation Rules: Verify if there are automated checks for data range, consistency, and completeness at the point of ingestion.
Resolution Actions:
- Deploy Edge AI: Process sensor data locally using Edge AI devices. This reduces latency for real-time decision-making and allows the experiment to continue functioning during network outages [30].
- Implement Tamper-Evident Logs: Use immutable audit logs to create a secure, time-stamped record of all data ingested, making manipulation evident [48].
- Establish a Verifiable Data Supply Chain: Ensure data is sourced from verified origins and use anomaly detection to flag suspicious data points as they enter the system [48].
Frequently Asked Questions (FAQs)
Q1: What is the concrete difference between data lineage and model documentation? A1: Data lineage is a technical map tracking the journey of data—its origin, movement, and transformations—through your systems. It answers "where did this data come from and how was it changed?" [44] [45]. Model documentation is a comprehensive record about an AI/ML model itself. It details the model's purpose, the data sources used to train it, its architecture, underlying assumptions, and its limitations [47]. Lineage is about the data's path, while documentation is about the model's construction and context.
Q2: Why is column-level lineage considered essential for troubleshooting, unlike table-level lineage? A2: Table-level lineage shows how entire tables are connected, but column-level lineage traces dependencies down to individual data fields [44]. When a single calculated field in your experiment is incorrect, table-level lineage only tells you which source tables were involved. Column-level lineage shows you the exact chain of transformations and computations for that specific field, dramatically speeding up root cause analysis [44] [49].
Q3: Our team is small. Is automated data lineage feasible, or is it a manual process? A3: Automated lineage is not only feasible but highly recommended to avoid the unsustainable burden of manual maintenance [44] [45]. Modern open-source and commercial tools can automatically scan your SQL scripts, ETL jobs, and other pipelines to build and maintain the lineage map [46] [49]. Manual processes quickly become outdated and untrustworthy in dynamic research environments [44].
Q4: How can we practically start implementing operational transparency with limited resources? A4: Begin with a high-impact, focused pilot:
- Select a Critical Experiment: Choose one important experiment whose integrity is paramount.
- Document a Single Model: Fully document the assumptions, data sources, and limitations for the model used in that experiment [47].
- Map Key Data Lineage: Use an available tool or a free trial of a commercial platform to automate lineage for the experiment's primary data pipeline [46] [49]. This focused approach demonstrates value and builds a case for broader implementation.
The Scientist's Toolkit: Key Solutions for Data Integrity
The following table details essential tools and methodologies for maintaining data integrity through operational transparency.
| Tool / Solution Category | Key Function | Relevance to Autonomous Experimentation |
|---|---|---|
| Automated Data Lineage Tools (e.g., OpenMetadata, Marquez) [46] | Automatically discovers and maps data flows across systems, tracking data from source to consumption. | Provides a verifiable map of how experimental data is transformed, crucial for replicability and debugging. |
| Model Documentation Frameworks (e.g., Model Cards) [47] | Provides a structured template for recording model purpose, data, assumptions, and limitations. | Ensures model assumptions and operational constraints are explicitly defined and communicated, preventing misuse. |
| Edge AI Compute [30] | Enables local, low-latency data processing at the source of data generation (e.g., in the lab). | Reduces reliance on cloud connectivity, allowing real-time analysis and control while enhancing data security. |
| Immutable Audit Logs [48] | Creates a tamper-evident record of all data access, changes, and model decisions. | Serves as a definitive provenance trail for regulatory compliance and forensic analysis of experimental runs. |
| Metadata Management Systems [45] | Serves as a unified repository for technical, operational, and business metadata. | Preserves the context, provenance, and historical context of research data across shifting systems and tools. |
Navigating Real-World Challenges: Identifying and Mitigating Data Integrity Risks
Troubleshooting Guide: Diagnosing Common Failure Modes
This guide helps researchers systematically identify and address failures that compromise data integrity in autonomous experimentation.
Failure Mode: Human Error
Human errors are unintentional actions or decisions that deviate from expected procedures.
| Failure Mode | Example in Autonomous Research | Impact on Data Integrity | Key Diagnostic Questions |
|---|---|---|---|
| Slips & Lapses (Unintended actions) [50] | Forgetting to calibrate a sensor before an automated run; transposing digits during manual data entry. [50] [19] | Introduces inaccuracy and inconsistency from the start of the data lifecycle, compromising all subsequent results. [19] | Was a step in a routine procedure missed or performed incorrectly? Is this an error in executing a planned action? |
| Mistakes (Wrong decisions) [50] | Incorrectly programming an experimental protocol into an automation system; misinterpreting a data sheet leading to wrong parameter settings. [50] | Leads to a fundamentally flawed experimental setup, causing systematic errors and making data invalid. [19] | Was the intended action itself wrong due to a lack of knowledge or incorrect judgment? |
Failure Mode: Systemic Flaws
Systemic flaws are inherent weaknesses in tools, processes, or infrastructure.
| Failure Mode | Example in Autonomous Research | Impact on Data Integrity | Key Diagnostic Questions |
|---|---|---|---|
| Poor Process Design [50] | An automated workflow lacks error-checking steps after critical instrument interactions. | Makes processes unreliable and non-reproducible, allowing errors to go undetected. [51] [19] | Does the process design make errors more likely? Are there built-in checks and controls? |
| Inadequate Tools & Version Control [52] | Using unversioned data or model code, leading to an inability to reproduce a previous experiment's conditions. | Directly undermines reproducibility, a cornerstone of research integrity. [53] [54] | Can you precisely recreate the state of the code, data, and model from any past experiment? |
| AI Model Failures [55] | An AI agent controlling experiments exhibits "reward hacking" to achieve a target metric via an unintended path, or "hallucinates" and fabricates data. [21] [55] | Produces misleading or entirely fabricated results that can be difficult to detect, potentially misdirecting research. [21] [55] | Is the AI model's behavior explainable and aligned with the true scientific goal? Has it been validated on diverse, real-world scenarios? |
Failure Mode: Environmental Threats
Environmental threats are external factors that disrupt the experimental system.
| Failure Mode | Example in Autonomous Research | Impact on Data Integrity | Key Diagnostic Questions |
|---|---|---|---|
| Data Fragmentation & Silos [19] | Experimental data is stored across disconnected instruments, legacy software, and individual spreadsheets. | Prevents a complete and consistent view of the data, hindering analysis and collaboration. [19] | Is all relevant data accessible from a single, unified source? Can you easily trace the data lineage? |
| Unauthorized Access & Security Breaches [19] | Lack of access controls allows accidental or malicious alteration of experimental parameters or datasets. | Compromises the accuracy and reliability of data, potentially invalidating intellectual property. [19] [52] | Are there robust, role-based controls on who can view, edit, or execute experiments and data? |
| Model & Data Drift [55] [52] | The statistical properties of incoming experimental data change over time (data drift), or an AI model's performance degrades due to changing conditions (model drift). | Leads to a gradual and often silent decay in data quality and model accuracy, rendering conclusions unreliable. [55] [52] | Are you continuously monitoring the statistical properties of input data and the performance of any AI models against a known baseline? |
Root Cause Analysis for Emergent AI Failures
When an AI component of your autonomous system fails unexpectedly, a structured root cause analysis (RCA) is essential. [55] Traditional debugging is often insufficient for complex AI behaviors. [55]
Methodology:
- Establish Full-Stack Observability and Agent Tracing: Implement comprehensive logging to capture the AI's entire operational process. This includes the initial prompt, all internal reasoning steps (chain-of-thought), any API calls or tool uses, and the final output. This trace is critical for pinpointing where the process failed. [55]
- Conduct Systematic Error Analysis and Categorization: Manually or semi-automatically review and label a set of failure incidents. Group similar failures into broader categories (e.g., "Factual Grounding Failure," "Contextual Collapse"). Calculate error rates to prioritize the most critical failure modes for investigation. [55]
- Deep Dive with Explainable AI (XAI) Techniques: Use techniques like SHAP (SHapley Additive exPlanations) or LIME (Local Interpretable Model-agnostic Explanations) to understand which features in the input data the model was focusing on when it failed. Visualization tools can reveal if the model was attending to irrelevant or spurious correlations. [55]
- Isolate, Test, and Remediate the Root Cause: Formulate a hypothesis for the root cause (e.g., "The model fails because its training data is outdated") and run controlled experiments to test it (e.g., "Implement a Retrieval-Augmented Generation (RAG) pipeline with a fresh knowledge base and measure the change in failure rate"). [55]
Frequently Asked Questions (FAQs)
Q: Our lab is mostly manual. What is the single most impactful step we can take to reduce human error? A: The most impactful step is to begin digitizing and centralizing your data. Transitioning from paper notebooks and spreadsheets to an Electronic Lab Notebook (ELN) or Laboratory Information Management System (LIMS) reduces manual transcription errors, eliminates data fragmentation, and provides a single source of truth. This directly addresses common slips/lapses like manual entry errors and mistakes from working with incomplete data. [19]
Q: We've implemented version control for our code, but is it really necessary for data and models too? A: Yes, absolutely. Version control for data and models is a core MLOps best practice and is non-negotiable for ensuring reproducibility. [52] Without it, you cannot reliably recreate the exact conditions of a past experiment. If a model fails in production, you need to know which version of the data and model code was used to quickly identify the change and roll back if necessary. [52]
Q: What does "silent failure" mean in the context of an autonomous experiment, and how can we prevent it? A: A "silent failure" occurs when the experimental system continues to operate without throwing an obvious error, but the data it is producing is becoming increasingly inaccurate or invalid. [52] Common causes include model drift and data drift. [55] [52] Prevention requires continuous monitoring of both the model's predictive performance and the statistical properties of the incoming data, comparing them to a established baseline. Automated alerts should trigger when deviations exceed a threshold. [52]
Q: How can we proactively find failures before they happen in a new automated workflow? A: Conduct a Process Failure Mode and Effects Analysis (PFMEA). [51] [56] This is a structured, proactive method where a multidisciplinary team: * Maps out the entire automated workflow. * Brainstorms potential failure modes at each step. * Analyzes the causes and effects of each potential failure. * Prioritizes risks using a Risk Priority Number (RPN). * Implements corrective actions to mitigate the highest-priority risks before the workflow goes live. [56]
The Scientist's Toolkit: Essential Research Reagent Solutions
This table details key digital and methodological "reagents" essential for maintaining data integrity.
| Tool / Solution | Function | Relevance to Data Integrity |
|---|---|---|
| Electronic Lab Notebook (ELN) / LIMS | Centralizes and digitizes experimental data, protocols, and results. [19] | Safeguards accuracy and consistency by reducing manual entry errors and data fragmentation. Ensures completeness by providing a structured repository. [19] |
| Version Control Systems (e.g., Git, DVC) | Tracks changes to code, data, and model artifacts over time. [52] | Ensures reproducibility by allowing researchers to revert to any previous state of an experiment. Creates a reliable audit trail. [53] [52] |
| Process Failure Mode and Effects Analysis (PFMEA) | A proactive risk assessment methodology for identifying and mitigating potential process failures. [56] | Improves reliability and robustness of experimental workflows by systematically addressing weaknesses before they cause data-compromising errors. [51] [56] |
| Explainable AI (XAI) Techniques | A suite of tools (e.g., SHAP, LIME) to interpret and understand the decision-making process of AI models. [55] | Provides transparency into the "black box" of AI, helping to diagnose failures, identify bias, and build trust in AI-driven experimentation. [21] [55] |
| Data Dictionary | A centralized document that defines all variables, their units, coding, and context. [54] | Ensures interpretability and understandability of data across the research team and over time, preventing misinterpretation that leads to analytical errors. [54] |
Proactive Risk Assessment with PFMEA
The PFMEA methodology provides a structured framework to proactively identify and mitigate potential failures before they impact your research. [56]
- Form a Multidisciplinary Team: Assemble a cross-functional team including process engineers, quality experts, operators, and data scientists. Diverse perspectives are crucial for identifying all potential failures.
- Process Mapping and Flowcharting: Create a detailed map or flowchart of the autonomous experimental workflow. Define the scope and boundaries of the analysis.
- Identify Potential Failure Modes: For each process step, brainstorm all the ways that step could fail (e.g., "sensor calibration skipped," "incorrect reagent volume dispensed," "AI model receives corrupted input data").
- Assign Severity, Occurrence, and Detection Rankings:
- Severity (S): Rank the seriousness of the effect of the failure on the data/output (e.g., 1=no effect, 10=catastrophic, invalidates all data).
- Occurrence (O): Rank the likelihood of the failure occurring (e.g., 1=very unlikely, 10=almost inevitable).
- Detection (D): Rank the ability to detect the failure before it affects the final result (e.g., 1=almost certain detection, 10=absolute uncertainty).
- Calculate the Risk Priority Number (RPN): Compute RPN = S × O × D. This quantitative measure helps prioritize which failure modes to address first. Higher RPNs indicate higher risk.
- Implement Corrective Actions: For high-RPN failure modes, define and implement actions to reduce the RPN. This could involve reducing the likelihood of occurrence (e.g., better training), improving detection (e.g., automated checks), or mitigating severity (e.g., design changes).
FAQ: Understanding Data Poisoning and Its Impact
What is data poisoning and why is it a significant threat to autonomous research?
Data poisoning is a type of cyberattack where an adversary intentionally corrupts the training data used to develop a machine learning (ML) or artificial intelligence (AI) model. The attacker injects harmful or misleading examples into the training dataset, which causes the model to learn incorrect patterns and behave in ways that benefit the attacker once deployed [57] [58]. This is particularly critical for autonomous experimentation because AI models make decisions based on their training. If the foundational data is compromised, all subsequent research findings, experimental directions, and conclusions are jeopardized, directly threatening research integrity and reproducibility [57] [54].
What is the difference between data poisoning and a prompt injection attack?
These attacks target different stages of the AI lifecycle. Data poisoning occurs during the training phase, corrupting the model from within before it is ever deployed. In contrast, a prompt injection occurs during inference (runtime), where the attacker manipulates the model's input to cause malicious behavior at that moment. The key difference is that data poisoning creates a fundamentally flawed model, while prompt injection exploits a model that was trained correctly [57] [58].
What are the common symptoms of a poisoned AI model?
It can be difficult to detect a poisoned model, as it may perform normally in most scenarios. However, some key symptoms include [59]:
- Model Degradation: Unexplained, persistent worsening of the model's performance and accuracy over time.
- Unintended Outputs: The model produces strange, biased, or unexpected results that its designers cannot explain.
- Increase in False Positives/Negatives: A sudden spike in incorrect classifications or decisions, such as a security model failing to detect specific threats.
- Biased Results: Outputs that unfairly skew toward a particular direction or demographic, indicating injected bias.
FAQ: Identifying and Diagnosing Threats
How can I tell if my experimental data has been poisoned?
Diagnosing data poisoning requires vigilance throughout the data lifecycle. Look for these warning signs:
- Anomalies in Training Data: Use data validation and anomaly detection tools to identify suspicious data points, outliers, or patterns that deviate from expected distributions [60] [59].
- Performance Discrepancies: The model performs well on training and validation sets but fails unexpectedly on specific, real-world inputs or attacker-controlled triggers [57].
- Audit Trail Irregularities: Review detailed logs of data access and modifications. Unauthorized changes or access from suspicious user accounts can indicate tampering [59].
What are the main types of data poisoning attacks I should guard against?
Data poisoning attacks can be classified by their method and goal. The table below summarizes the primary types [57] [58] [59].
| Attack Type | Objective | Common Techniques |
|---|---|---|
| Backdoor Attacks | Embeds a hidden trigger; the model behaves normally until it encounters the trigger, then acts maliciously. | Introducing data with subtle, imperceptible modifications (e.g., a specific pixel pattern in an image, inaudible audio noise). |
| Label Flipping | Causes the model to misclassify data by corrupting the labels in the training set. | Systematically swapping correct labels with incorrect ones (e.g., labeling "cat" images as "dog"). |
| Availability Attacks | Degrades the model's overall performance and reliability, making it unusable. | Injecting random noise or fabricated data to reduce the model's general accuracy and robustness. |
| Clean-Label Attacks | A stealthy attack where data is poisoned but still appears to be correctly labeled, evading detection. | Making subtle, malicious modifications to data points without changing their labels, exploiting model vulnerabilities. |
The following diagram illustrates the typical lifecycle of a data poisoning attack, from the attacker's perspective to the compromised model's deployment.
FAQ: Prevention and Mitigation Strategies
What are the most effective strategies to prevent data poisoning?
A robust defense requires a multi-layered approach focused on data integrity and continuous monitoring. Key strategies include [58] [60] [59]:
- Data Validation and Sanitization: Implement strict processes to check and clean training data before use, identifying and removing suspicious or corrupted data points.
- Adversarial Training: Proactively improve model robustness by intentionally including carefully crafted adversarial examples during the training phase, teaching the model to resist manipulation.
- Strict Access Controls and Data Provenance: Enforce the principle of least privilege (POLP) for data access. Maintain detailed records (provenance) of all data sources, modifications, and access requests to create accountability and a traceable audit trail.
- Continuous Monitoring and Anomaly Detection: Use security tools to monitor the model's performance and data inputs in real-time, allowing for the swift detection of and response to unusual behavior or performance degradation.
If I suspect my model has been poisoned, what steps should I take?
A swift and systematic response is critical to contain the damage.
- Isolate and Contain: Immediately take the compromised model offline to prevent it from affecting operational decisions or research outcomes.
- Investigate and Trace: Leverage your data provenance and audit logs to trace the source of the poisoning. Identify which data was manipulated and how it was introduced.
- Eradicate and Clean: Remove the poisoned data from your training sets. This may require reverting to a known-clean, earlier version of the dataset.
- Retrain and Validate: Retrain the model on the sanitized dataset. Thoroughly validate its performance against clean test data before considering re-deployment.
- Enhance Security: Analyze the incident to identify security gaps and strengthen your defenses to prevent a recurrence [59].
The diagram below maps the key defensive measures to the specific parts of the ML workflow they protect.
The Scientist's Toolkit: Key Reagents for Defense
The following table details essential "research reagents" – in this case, security practices and tools – that are critical for building a lab environment resilient to data poisoning threats.
| Tool / Solution | Function in Preventing Data Poisoning |
|---|---|
| Data Provenance Framework | Creates a detailed, immutable record of data origin, movement, and transformation, enabling attack tracing and data lineage verification [59] [54]. |
| Anomaly Detection Software | Automatically scans training data and model behavior to identify statistical outliers and patterns indicative of poisoned samples [60] [59]. |
| Electronic Lab Notebooks (ELN) / LIMS | Centralizes and secures experimental data with role-based access controls and detailed audit trails, reducing fragmentation and unauthorized modification risks [19]. |
| Adversarial Training Libraries | Provides algorithms and frameworks to generate adversarial examples and harden models against evasion and poisoning attacks during training [58] [59]. |
| Unified SIEM Solution | A Security Information and Event Management (SIEM) system aggregates and correlates logs from networks, endpoints, and cloud storage to detect coordinated poisoning activities [60]. |
Troubleshooting Guide: Identifying Data Integrity Gaps
This guide helps you diagnose common data integrity issues in autonomous experimentation. Follow the flowchart below to systematically identify potential problems in your research data.
Detailed Diagnostic Steps
1. Environment Factors
- Check physical conditions: Verify temperature, humidity, and lighting are within equipment specifications [61].
- Assess connectivity: Ensure stable internet/power supply for continuous data recording [61].
- Evaluate workspace: Confirm adequate space for proper equipment operation and participant interaction [61].
2. Technology & Equipment
- Verify sensor calibration: Check calibration records and perform validation tests [2].
- Test data transmission: Ensure complete data transfer between systems without corruption [2].
- Confirm storage integrity: Validate that data is stored securely with proper backup systems [62].
3. User Skills & Procedures
- Assess training adequacy: Verify users received comprehensive equipment and protocol training [61].
- Review documentation: Check for contemporaneous, accurate recording following ALCOA+ principles [3].
- Evaluate adherence: Observe whether users follow established protocols consistently [61].
4. Subject Engagement
- Monitor participation: Track attendance and completion rates for studies involving human subjects [61].
- Assess comfort: Ensure subjects are comfortable with equipment and procedures [61].
- Review incentives: Evaluate whether participation incentives adequately motivate engagement [61].
Frequently Asked Questions
What are the most critical environmental factors affecting data integrity in mobile health studies? Environmental challenges in field-based research include limited power sources, extreme temperatures, poor connectivity, and difficult transportation conditions. These factors can cause data loss, sensor malfunctions, and incomplete datasets. Implement environmental buffers such as portable power banks, protective equipment cases, and offline data collection capabilities to mitigate these issues [61].
How can we quickly assess if our automated laboratory systems are maintaining data integrity? Conduct regular mini-audits focusing on these key indicators:
- Data completeness: Verify no missing entries in datasets [62]
- System integration: Check seamless data flow between instruments, LIMS, and ELNs [2]
- Audit trails: Review electronic records for unauthorized changes or deletions [3]
- Backup verification: Confirm successful data backups and test recovery procedures [62]
What specific user skill gaps most commonly compromise data integrity? Common skill deficiencies include:
- Inadequate sensor operation: Improper placement or usage of physiological sensors [61]
- Poor documentation practices: Failure to follow Good Documentation Practices (GDP) and ALCOA+ principles [3]
- Limited troubleshooting ability: Inability to identify and address basic equipment issues [26]
- Insufficient data validation: Lack of understanding in verifying data quality and accuracy [2]
How does the ALCOA+ framework apply to autonomous experimentation data? ALCOA+ principles ensure data integrity throughout the research lifecycle:
| Principle | Application in Autonomous Research |
|---|---|
| Attributable | System automatically records user IDs and timestamps for all data entries [3]. |
| Legible | Electronic records remain readable throughout data lifecycle [3]. |
| Contemporaneous | Real-time data capture with automated time-stamping [3]. |
| Original | Secure storage of source data with protected audit trails [3]. |
| Accurate | Automated validation rules and range checks [3]. |
| Complete | System checks for missing data and confirms full dataset transmission [3]. |
What technological solutions best prevent data integrity gaps in automated labs? Implement a layered approach:
- Laboratory Information Management System (LIMS): Centralizes data storage and sample tracking [2]
- Automated data capture: Reduces manual entry errors [2]
- Integration architecture: Ensures seamless communication between instruments and data systems [2]
- Cybersecurity measures: Protects against unauthorized access and data corruption [62]
Experimental Protocol: Assessing Data Integrity Risks
This protocol provides a standardized methodology for evaluating data integrity risks in research environments, based on a validated approach from mHealth research [61].
Methodology
1. Quantitative Data Analysis
- Data Collection: Collect system usage logs, sensor outputs, and data completion records over a representative period [61]
- Completeness Calculation: Determine the percentage of expected data points successfully captured
- Quality Assessment: Evaluate signal quality metrics appropriate to your sensors and equipment
2. Qualitative Evaluation
- Structured Interviews: Conduct interviews with research staff, field workers, and technicians [61]
- Usability Assessment: Evaluate the ease of use and logical workflow of data collection systems [61]
- Content Analysis: Identify common themes in data integrity challenges from interview transcripts [61]
Implementation Checklist
Use this comprehensive checklist to evaluate and address data integrity risks in your research environment:
Risk Assessment Table
| Risk Category | Specific Risk Factors | Mitigation Strategies |
|---|---|---|
| Environment | Power outages, extreme temperatures, poor connectivity [61] | Portable power sources, environmental protection, offline capabilities [61] |
| Technology | Sensor malfunction, software errors, data transmission failures [2] | Regular calibration, automated validation, secure backup systems [62] |
| User Skills | Insufficient training, documentation errors, protocol deviations [61] | Comprehensive training, clear SOPs, regular competency assessment [3] |
| Subject Engagement | Low participation, discomfort with equipment, motivation issues [61] | Clear communication, comfortable procedures, appropriate incentives [61] |
The Scientist's Toolkit: Essential Research Reagents & Solutions
| Tool/Resource | Function in Data Integrity Management |
|---|---|
| Laboratory Information Management System (LIMS) | Centralizes data storage, tracks samples, and ensures consistent data handling across systems [2]. |
| Electronic Lab Notebooks (ELNs) | Provides structured environment for recording experimental data following ALCOA+ principles [3]. |
| Automated Data Validation Tools | Implements real-time checks for data accuracy, completeness, and consistency [62]. |
| Audit Trail Systems | Tracks all data modifications, providing chronological record of changes for compliance and troubleshooting [3]. |
| Data Backup and Recovery Solutions | Ensures data availability and protects against loss from system failures or cybersecurity incidents [62]. |
| Standard Operating Procedures (SOPs) | Establishes consistent protocols for data handling, documentation, and equipment operation [2]. |
| Sensor Calibration Tools | Maintains measurement accuracy through regular validation and adjustment of sensing equipment [2]. |
Troubleshooting Guide: Common Issues in Autonomous Systems
| Problem Area | Specific Symptoms | Potential Causes | Recommended Solutions |
|---|---|---|---|
| System Performance | Task completion failures; failure to discover diverse failure modes during testing [63] [64]. | Improper task planning; generation of nonfunctional code; inadequate refinement strategies [63]. | Implement learning-based Bayesian inference for more efficient failure mode discovery [64]. Enhance planner logic and self-diagnosis mechanisms [63]. |
| Data Integrity | Inaccurate data; inconsistencies across datasets; incomplete data [19] [54]. | Manual data entry errors; data fragmentation across siloed systems; use of outdated systems [19]. | Implement a centralized digital platform (e.g., ELN, LIMS); enforce a data dictionary; maintain raw data; automate data validation [19] [54]. |
| Model Degradation | Decreased prediction accuracy in production; model drift [52]. | Changes in underlying data distribution (data drift); concept drift; poor initial data quality [52]. | Set up real-time performance monitoring and data drift detection algorithms. Establish automated retraining pipelines [52]. |
| Graceful Degradation | System crashes or fails unsafely under stress or component failure [65]. | Lack of predefined degraded modes; wrong priority assignments; no resource monitoring [65]. | Identify and prioritize functions via hazard analysis. Define a mode table with triggers and safe reactions. Instrument resource and fault detection [65]. |
| Research Reproducibility | Inability to reproduce model results or experimental outcomes [53] [54]. | Inconsistent environments; undocumented dependencies; lack of version control for data, code, and models [53] [52]. | Use containerization; implement version control for all artifacts (code, data, models); maintain detailed documentation and a data dictionary [53] [54] [52]. |
Frequently Asked Questions (FAQs)
Q1: What is the core difference between a fail-safe and graceful degradation? A fail-safe is a broader concept where a system defaults to a predefined, safe state upon a failure to prevent harm. Graceful degradation is a specific strategy to achieve fail-safe operation, where a system maintains its most critical safety-related functions by deliberately reducing non-critical services when parts fail or resources run low [65]. It is a planned, deliberate state, not an accidental failure.
Q2: How can I proactively discover how my autonomous system might fail before deployment? Conventional testing methods like large-scale Monte Carlo simulations are inefficient for finding rare failures. Instead, consider advanced testing frameworks like learning-based Bayesian inference, which can efficiently explore the search space to discover diverse and rare failure modes by finding environmental conditions that lead to system failure [64].
Q3: Our team struggles with model reproducibility. What are the key practices to ensure we can replicate results? Reproducibility hinges on rigorous version control and documentation. Key practices include:
- Version Control Everything: Track code, data, models, and configurations using tools like Git and DVC [52].
- Containerization: Use Docker to package your code and dependencies, ensuring consistent environments across stages [52].
- Documentation: Maintain a data dictionary that explains all variable names, coding categories, and units [54].
- Keep Raw Data: Always save the original, unprocessed data in multiple locations [54].
Q4: What are the fundamental principles for maintaining data integrity in automated experiments? Data integrity is built on principles that should guide your data handling processes [54]:
- Accuracy: Data must reflect true observed values.
- Completeness: Data must contain all relevant information.
- Reproducibility: Data collection and processing must be replicable.
- Understandability: Data should be comprehensible without overly specific knowledge. Balancing these principles, such as ensuring completeness without sacrificing accuracy, is key to robust data integrity [54].
Q5: How can we design our ML system to gracefully handle a sudden drop in computational resources? Apply the core principles of graceful degradation [65]:
- Identify & Prioritize Functions: Classify functions by criticality (e.g., safety-alarm vs. non-critical reporting).
- Define a Mode Table: Specify triggers (e.g., CPU >90%) and actions (e.g., "keep" critical alarm scanning, "shed" maintenance UI).
- Instrument Monitors: Implement resource monitors (CPU, memory) with hysteresis to prevent mode thrashing.
- Annunciate State: Clearly indicate "Degraded Mode" to operators so they are aware of limited functionality.
The Scientist's Toolkit: Essential Research Reagents & Solutions
| Item | Function in the Context of Fail-Safes & Data Integrity |
|---|---|
| Electronic Lab Notebook (ELN) | A digital platform for centralizing experimental data, ensuring consistency, accuracy, and providing detailed audit trails to safeguard data integrity [19]. |
| Version Control Systems (e.g., Git, DVC) | Tools for tracking changes across all ML artifacts (code, data, models), creating reproducible workflows and allowing teams to roll back to stable versions if failures occur [52]. |
| Containerization (e.g., Docker) | Technology that packages code and dependencies into isolated units, guaranteeing environment consistency and enabling reproducible results across different machines [52]. |
| Model Registry (e.g., MLflow) | A centralized system to manage, version, and track the lifecycle of machine learning models, which is critical for auditability and deploying known-good model versions [52]. |
| Data Dictionary | A separate document that defines all variable names, categories, units, and collection context. It is essential for ensuring data is interpretable and used correctly by all researchers, protecting against misinterpretation [54]. |
| Bayesian Inference Testing Framework | A specialized testing methodology that uses learning-based techniques to efficiently discover rare failure modes in autonomous systems by exploring the environment variable space [64]. |
Experimental Protocol: Testing a Graceful Degradation Mechanism
1. Objective: To verify that a system correctly enters a predefined degraded mode and maintains its critical safety functions when subjected to resource stress or component failure.
2. Methodology:
- System Instrumentation: Integrate resource monitors for CPU load, memory pressure, and communication status. Implement a state machine that manages mode transitions based on predefined triggers [65].
- Fault Injection: Simulate adverse conditions to test the system's response. This includes [65]:
- Artificially spiking CPU load.
- Simulating brownout conditions (low voltage).
- Introducing network instability or communication loss.
- Validation & Measurement: During fault injection, measure [65]:
- Determinism: Verify that worst-case execution times for safety-critical functions are still met.
- Functionality: Confirm that critical functions (e.g., alarm scanning) are active and non-critical ones (e.g., history export) are shed or simplified.
- Annunciation: Check that the system clearly indicates its degraded state to the operator.
3. Evaluation: The experiment is successful if the system's safety functions remain operational within their timing bounds, non-critical services are correctly managed, and the state change is unambiguously communicated, as per the predefined mode table [65].
Graceful Degradation Logic Flow
Data Integrity Workflow for Autonomous Research
Autonomous experimentation represents a paradigm shift in research, leveraging artificial intelligence (AI), robotics, and real-time data analysis to accelerate discovery. In this data-driven environment, data integrity—the accuracy, consistency, and reliability of data throughout its lifecycle—becomes the cornerstone of scientific validity. The integration of AI and machine learning (ML) in research institutions demands foundational guidelines for their ethical, transparent, and sustainable use to protect research integrity and public trust [66]. Similarly, modern laboratories are transforming into interconnected data factories, where the seamless flow of standardized, high-integrity data from instruments to analysis platforms is critical for competitiveness and discovery speed [30]. Cultivating a culture of integrity is not merely a procedural requirement but a fundamental component that enables researchers to harness the full potential of automation while ensuring the credibility of their outcomes.
Core Principles and Training Framework
A robust culture of integrity is built on a framework of core principles that guide daily operations and long-term strategy. These principles should be embedded into every aspect of the research lifecycle, from initial design to final publication.
- Principle 1: Reproducibility. Every experiment must be designed and documented such that it can be replicated precisely. This requires versioning everything, including code, data, and models, and logging every training run with detailed environment information [67].
- Principle 2: Transparency. All processes, algorithms, and data sources must be open to scrutiny. This involves promoting transparency and oversight in AI systems and maintaining clear metadata and provenance [66].
- Principle 3: Accountability. Clear roles and responsibilities for data integrity must be established. This is supported by tracking lineage—knowing who trained a model, on what data, and with what configuration—to ensure full auditability [67].
- Principle 4: Security and Sovereignty. Data must be protected from unauthorized access or modification, and cultural and data sovereignty must be respected, ensuring data is used in a rights-respecting manner [66].
Essential Training Modules
A continuous training program is vital to instill these principles. Key modules should include:
- Good Documentation Practices (GDCP): Training on the precise and contemporaneous recording of all experimental procedures and data, a practice emphasized even in challenging environments like maximum containment laboratories [68].
- AI and ML Ethics for Researchers: Guidance on identifying and mitigating risks like algorithmic bias and information loss when using AI tools for data analysis [66].
- Data Quality Standards (e.g., GLP): Training on quality systems like Good Laboratory Practice (GLP) regulations, which are essential for ensuring the reliability and regulatory usefulness of generated data [68].
- Introduction to MLOps: Education on MLOps best practices, including experiment tracking, version control, and CI/CD automation, to ensure models are production-ready and reliable [67] [69].
Troubleshooting Common Data Integrity Issues
This section serves as a technical support center, providing direct answers to specific data integrity challenges encountered during autonomous experimentation.
Problem: How do we verify the authenticity of participants in a fully remote, longitudinal study?
- Solution: Implement a multi-step authentication protocol without creating barriers to participation. A proven method includes both passive checks (e.g., randomized online survey passwords) and a five-step active protocol:
- Interest Form Duplication Review: Check for duplicate personal information in initial sign-ups.
- Screening Attention Check: Embed attention-check questions in screening surveys.
- Personal Information Verification: Review provided information for inconsistencies post-screening.
- Verbal Identity Confirmation: Conduct a verbal confirmation at the baseline interview.
- Consistent Reporting Review: Check for inconsistent responses across the baseline assessment [70].
- Data: In one study, this protocol led to the exclusion of 11.13% of potential participants from online advertising. The "personal information verification" step was most effective, accounting for 56.2% of failed checks [70].
- Solution: Implement a multi-step authentication protocol without creating barriers to participation. A proven method includes both passive checks (e.g., randomized online survey passwords) and a five-step active protocol:
Problem: Our machine learning models are performing well in development but fail quietly in production. How can we detect this?
- Solution: Implement comprehensive post-deployment monitoring to catch problems early.
- Track Model Performance: Continuously monitor metrics like accuracy and precision.
- Set Up Data Drift Detection: Use tools like Evidently AI or WhyLabs to detect when incoming production data differs significantly from training data.
- Monitor for Concept Drift: Identify when the relationship between model features and the target variable evolves over time.
- Set Up Alerting Pipelines: Use systems like Prometheus and Grafana to trigger alerts when key metrics degrade beyond a threshold [67].
- Solution: Implement comprehensive post-deployment monitoring to catch problems early.
Problem: An experiment produces a groundbreaking result, but we cannot reproduce it. What went wrong?
- Solution: Ensure full reproducibility by logging every aspect of the experimental run.
- Logging: Use tools like MLflow, Weights & Biases, or Neptune.ai to log parameters, metrics, and code versions for every training run.
- Environment Capture: Containerize training pipelines with Docker and capture library versions.
- Versioning: Version all code, data, and models using Git, DVC, or similar tools. Tag every production model with the exact dataset and code commit used to train it [71] [67].
- Solution: Ensure full reproducibility by logging every aspect of the experimental run.
Problem: We need to process high-volume sensor data from lab equipment for real-time control, but cloud latency is too high.
- Solution: Adopt a Hybrid Infrastructure with Edge AI. Deploy local high-performance computing (HPC) resources, such as Cloud GPUs, on-premises. This enables:
- Faster Decision-Making: AI models can provide immediate feedback to robotic systems.
- Enhanced Security: Sensitive data can be processed locally before anonymization.
- Operational Resilience: Core lab functions remain operational during network outages [30].
- Solution: Adopt a Hybrid Infrastructure with Edge AI. Deploy local high-performance computing (HPC) resources, such as Cloud GPUs, on-premises. This enables:
Problem: A manuscript is flagged for potentially manipulated images. How could this have been prevented?
- Solution: Engage with the broader research integrity community and utilize emerging tools. Attend forums like the STM Research Integrity Day to learn about the latest trends and tools designed to detect fraudulent manuscripts and image manipulation [72].
Essential Protocols for Key Experiments
Protocol 1: ML Experiment Tracking and Reproducibility
This protocol ensures that machine learning experiments are well-organized, comparable, and reproducible.
- Objective: To systematically track, compare, and reproduce ML experiments, ensuring valid conclusions and model reliability.
- Methodology:
- Tool Selection: Choose an experiment tracking tool (e.g., MLflow, Neptune, Weights & Biases) based on your team's workflow, framework compatibility, and collaboration needs [71].
- Integration: Integrate the tool's client library into your training scripts.
- Logging: For each experiment run, log:
- Comparison: Use the tool's UI to compare runs, analyze different models, and select the best performer based on multiple metrics [73].
- Troubleshooting Tip: If results cannot be reproduced, verify that the logged environment details and dataset version exactly match those of the original run.
Protocol 2: Authenticating Remote Research Participants
This protocol safeguards data integrity in studies involving remote recruitment, minimizing fraudulent submissions.
- Objective: To authenticate participants recruited remotely for a longitudinal study while avoiding barriers to participation for stigmatized or marginalized groups [70].
- Methodology:
- Initial Screening: Implement an online screening survey with an embedded attention check question.
- Information Verification: Automatically and manually review provided personal information for duplicates or logical inconsistencies.
- Identity Confirmation: Conduct a verbal identity confirmation during the first phone or video interview.
- Consistency Check: Review responses across the baseline assessment for inconsistent reporting of key data (e.g., substance use frequency) [70].
- Troubleshooting Tip: If a high rate of fraudulent submissions is detected from a specific recruitment channel, add a step to review IP addresses for suspicious patterns or geolocations.
Technical Solutions & Research Reagents
The following table details key digital "reagents" and tools essential for maintaining data integrity in an automated research environment.
Table 1: Essential Research Reagent Solutions for Data Integrity
| Tool Category | Example Solutions | Primary Function |
|---|---|---|
| Experiment Tracking | MLflow, Weights & Biases, Neptune.ai | Logs parameters, metrics, and artifacts for ML experiments; enables comparison and reproducibility [71] [73] [67]. |
| Data Versioning | DVC, LakeFS, Delta Lake | Versions and manages large datasets, linking them to specific code commits and model outputs [67] [69]. |
| Model Monitoring | Evidently AI, WhyLabs, Prometheus | Monitors production models for performance degradation, data drift, and concept drift [67]. |
| Workflow Orchestration | Airflow, Kubeflow Pipelines, Prefect | Automates and coordinates end-to-end ML pipelines, from data ingestion to model deployment [67]. |
| Feature Storage | Feast, Tecton | Centralizes and manages model features, ensuring consistency between training and inference [67]. |
Visualizing the Integrity Framework
The following diagrams illustrate the key workflows and relationships that underpin a culture of integrity in autonomous research.
Data Integrity Troubleshooting Workflow
Frequently Asked Questions (FAQs)
How do we decide which MLOps tools to use for our research team? Start by defining your stack based on use case maturity and team size. For early-stage research, tools like MLflow, DVC, and Airflow offer flexibility. At a larger scale, consider end-to-end platforms like Kubeflow or cloud-specific options. Always prioritize interoperability and versioning support [67].
How can we automate model retraining without increasing technical debt? Set up event-based retraining triggers, such as data drift alerts or performance dips. Automate model validation against a champion model before deployment and use shadow testing or canary releases to minimize risk. CI/CD pipelines with rollback capabilities are key [67].
What are the first steps to implementing MLOps practices in a traditional lab? Start small. Begin by tracking experiments with MLflow and versioning data with DVC. Then, gradually containerize model training and deployment workflows. Don't aim for full automation upfront; build your MLOps capabilities iteratively [67].
Do we need a dedicated MLOps team? Effective MLOps requires collaboration between data scientists, ML engineers, and DevOps. For smaller teams, cross-functional roles can work. As you scale, dedicated MLOps expertise becomes essential for maintaining system reliability and speed [67].
How do we monitor models without creating alert fatigue? Focus on business-impacting metrics alongside ML metrics. Use tools like Evidently AI or WhyLabs to set targeted alerts based on meaningful thresholds, and evolve towards more sophisticated anomaly-based detection over time [67].
Proving Trustworthiness: Validation Strategies for AI-Driven Decisions
Troubleshooting Guides
Simulation Layer Discrepancies
Issue: Significant drift between simulated and expected theoretical models
- Problem: My simulation results show a persistent and growing drift from the expected theoretical output, making the model unreliable for prediction.
- Diagnosis:
- Verify Model Fidelity: Check that all model parameters (e.g., coefficients, time constants) are correctly entered and use data type
doublefor high precision to minimize quantization error [74]. - Check Solver Configuration: Ensure the ODE/PDE solver (e.g., ODE45, Runge-Kutta) is appropriate for your system's stiffness. A variable-step solver is often necessary for systems with dynamics that change rapidly [74].
- Validate Initial Conditions: Confirm that all initial states are set correctly, as erroneous initial conditions can cause the solution to diverge from the expected path.
- Verify Model Fidelity: Check that all model parameters (e.g., coefficients, time constants) are correctly entered and use data type
- Resolution Protocol:
- Run the simulation for a simple, known-good test case where the analytical solution is available.
- Gradually reduce the solver's relative and absolute error tolerances (e.g., from
1e-3to1e-6) and observe if the drift decreases. Tighter tolerances increase computation time but improve accuracy. - If the problem persists, isolate and simulate individual model components to identify the specific subsystem causing the divergence.
Issue: Simulation fails to initialize or terminates abruptly
- Problem: The simulation software throws an initialization error or stops unexpectedly during runtime.
- Diagnosis:
- Algebraic Loop Detection: The model likely contains an algebraic loop—a circular dependency of signals that does not contain a discrete or continuous state block. Most simulation environments have debugging flags to detect these.
- Memory Overflow: Check for memory leaks or excessively small fixed-step sizes that generate too much data.
- Resolution Protocol:
- Introduce a
Unit DelayorMemoryblock into the suspected loop to break the direct feedthrough. - For memory issues, increase the solver's step size or limit the output data saved to only essential signals. Monitor system memory usage during initialization.
- Introduce a
Hardware-in-the-Loop (HIL) Layer Synchronization
Issue: Latency and timing jitter in HIL test results
- Problem: The HIL test results show inconsistent timing, with variable latency between the input commands and the system's output response, compromising data integrity.
- Diagnosis:
- Real-Time Kernel Performance: The HIL platform's operating system may not be configured for true hard real-time execution, causing other processes to interrupt the model's execution.
- Model Overload: The computational load of the model may exceed the HIL hardware's capability, causing overruns where the model cannot complete its calculation within one sample period.
- Resolution Protocol:
- Run a benchmark test on the HIL hardware to verify real-time kernel performance. Disable any non-essential services or processes on the host machine.
- Profile the model's execution time. Simplify the model by reducing complexity or increasing the fixed step size until the execution time is consistently less than the sample time.
- Use a dedicated digital I/O card with its own clock for time-critical signal generation and acquisition to bypass the operating system's scheduling.
Issue: Communication bus errors (e.g., CAN, Ethernet) between HIL and Unit Under Test
- Problem: Frequent packet drops, checksum errors, or timeouts on the communication bus connecting the HIL simulator and the Unit Under Test (UUT).
- Diagnosis:
- Physical Layer Check: Verify cable integrity, termination resistors (for CAN), and connector pins.
- Configuration Mismatch: Ensure the baud rate, message ID, and data format (e.g., big-endian vs. little-endian) are identically configured on both the HIL transceiver and the UUT.
- Resolution Protocol:
- Use a bus analyzer (e.g., CANoe, Wireshark) to monitor the raw bus traffic and isolate the source of the error.
- Implement a "heartbeat" signal in the communication protocol. If the heartbeat is lost, the test should fail gracefully with a clear log entry indicating the time and nature of the failure.
Field Testing Data Anomalies
Issue: Corrupted or missing data logs from field tests
- Problem: After a field test, data files are partially corrupted, unreadable, or completely missing, creating gaps in the experimental record.
- Diagnosis:
- Power Instability: Sudden loss of power to the data logger during shutdown can corrupt the file system.
- Faulty Storage Media: The SD card or solid-state drive may be damaged or have worn out from excessive write cycles.
- Software Crash: The logging application may have crashed due to an unhandled exception, stopping data recording.
- Resolution Protocol:
- Implement a robust shutdown sequence with a dedicated "shutdown" signal that triggers the logger to close all files properly before power is cut.
- Use industrial-grade, high-endurance storage media. After each test, verify data integrity using checksums (e.g., SHA-256).
- Program the logging application with a watchdog timer that automatically restarts the process if it becomes unresponsive.
Issue: Inconsistent results between HIL and field testing phases
- Problem: The system performs flawlessly in HIL testing but exhibits different behaviors or failures in the field.
- Diagnosis:
- Unmodeled Environmental Dynamics: The simulation model may not account for real-world environmental factors like temperature extremes, vibration, or electromagnetic interference.
- Sensor/Actuator Discrepancy: Differences in performance or calibration between the simulated, HIL, and physical sensors/actuators.
- Resolution Protocol:
- Parameter Identification: Conduct system identification tests in the field to characterize and update the simulation model with real-world parameters.
- Calibration Cross-Check: Establish a traceable calibration chain. Ensure all sensors used in HIL bench setups are regularly calibrated against a primary standard, and that the same calibration files are used in the simulation models.
Frequently Asked Questions (FAQs)
Q1: Why is a multi-layered validation strategy critical for autonomous experimentation and drug development? A multi-layered approach de-risks the entire R&D pipeline [75]. Simulation allows for high-risk, low-cost hypothesis testing. HIL testing validates software and control logic against physical hardware responses in a safe, controlled environment. Finally, field testing (or lab-based clinical simulation) uncovers unpredictable real-world interactions. This layered strategy ensures data integrity by providing multiple, independent verification points, which is non-negotiable in regulated fields like drug development [76].
Q2: How do we establish a traceability matrix across simulation, HIL, and field testing data? A robust traceability matrix is foundational. It should link each requirement to specific test cases in each validation layer. The following table outlines a sample structure for such a matrix:
| Requirement ID | Simulation Test Case | HIL Test Case | Field Test Case | Verification Status | Data Integrity Hash |
|---|---|---|---|---|---|
| REQ-001-PK | SIM-PK-01 (IV dosing) | HIL-PK-01 (pump accuracy) | FIELD-PK-01 (in-vivo) | Pass | SHA-256: a1b2... |
| REQ-002-PD | SIM-PD-05 (EC50 fit) | HIL-PD-02 (sensor response) | FIELD-PD-03 (biomarker) | In Progress | SHA-256: c3d4... |
Q3: What are the recommended color-coding standards for wiring and data streams in HIL setups? Using a consistent, high-contrast color palette prevents misidentification. The following palette, which provides sufficient contrast for users with color vision deficiencies, is recommended for diagrams and physical labels [77] [78] [79].
| Function | Color Hex | Usage Example |
|---|---|---|
| Power (Primary) | #EA4335 (Red) [77] |
24V Main Power Line |
| Communication (Data Bus) | #4285F4 (Blue) [77] |
CAN, Ethernet Cables |
| Sensor Signal (Input) | #34A853 (Green) [77] |
Analog Voltage Inputs (0-5V) |
| Actuator Signal (Output) | #FBBC05 (Yellow) [77] |
PWM, Digital Outputs |
| Ground | #5F6368 (Dark Gray) |
Earth, Signal Ground |
Q4: Our team is new to HIL testing. What are the essential hardware components for a starter kit? A basic HIL kit for validating an embedded system should include the components listed in the table below.
| Component | Function | Example Part/Spec |
|---|---|---|
| Real-Time Target Computer | Executes plant model in hard real-time with deterministic timing. | National Instruments PXIe-8840, Speedgoat Baseline |
| I/O Interface Cards | Provides analog/digital, input/output channels to interface with UUT. | Analog I/O (PXI-6289), CAN Interface (PXI-8513) |
| Signal Conditioning | Protects I/O cards by scaling/isolating voltages and currents from the UUT. | SCB-68A breakout box with optional isolation |
| Breakout Box / Panel | Provides easy-access terminal blocks for all signals connected to the UUT. | Custom-designed with labeled, color-coded terminals |
Q5: How can we automatically flag data integrity issues, such as manipulation or corruption, in our test results? Implement a digital fingerprint for every dataset. This involves generating a cryptographic hash (e.g., SHA-256) of the raw data file immediately upon acquisition. This hash should be stored separately from the data. Any subsequent alteration of the data, no matter how small, will change this hash. During analysis, re-compute the hash and compare it to the stored value; a mismatch indicates potential corruption or tampering, automatically flagging the dataset for review [76].
The Scientist's Toolkit: Research Reagent Solutions
For research involving biological validation in the field testing phase, the following reagents are essential.
| Research Reagent | Function in Validation |
|---|---|
| Calibration Buffer Set (e.g., pH 4.00, 7.00, 10.01) | Provides known reference points to calibrate pH and ion-selective sensors in HIL benches and field-deployed instruments, ensuring measurement traceability. |
| Stable Isotope-Labeled Internal Standards | Spiked into biological samples during mass spectrometry analysis to correct for sample preparation losses and matrix effects, guaranteeing quantitative accuracy. |
| Genetically Encoded Biosensors (e.g., GCaMP for Ca²⁺) | Expressed in cell cultures or model organisms during in-vivo field tests to provide real-time, spatially resolved readouts of physiological activity. |
| Validated Antibody Panels (for Flow Cytometry) | Used to tag and identify specific cell types in complex mixtures, validating that the system's biological response matches the predicted mechanistic model. |
| Synthetic Agonists/Antagonists | Pharmacological tools used in HIL and field tests to probe specific pathways, confirming that the system's response to a controlled stimulus aligns with model predictions. |
Multi-Layered Validation Workflow
The following diagram illustrates the logical relationship and data flow between the three validation layers, which is critical for ensuring a seamless and traceable process.
Frequently Asked Questions (FAQs)
FAQ 1: What is the primary goal of benchmarking autonomous systems against traditional methods? The primary goal is to quantitatively assess the performance and reliability gains of new, AI-driven systems. This process helps identify improvements in operational efficiency, cost reduction, and error rates, while ensuring that the integrity of the research data is maintained or enhanced. This validation is crucial for building trust in autonomous systems [30] [48].
FAQ 2: Why is data integrity a special concern in autonomous experimentation? Autonomous systems make decisions at speeds and scales that were once unimaginable, and their outputs are entirely shaped by the data they ingest [48]. If this data is biased, flawed, or maliciously manipulated (a threat known as data poisoning), the models will reproduce those distortions at scale, often without obvious warning. A 2025 Nature Medicine study revealed that introducing just 0.001% of AI-generated misinformation into a training dataset caused a medical large language model to produce 4.8% more harmful clinical advice, despite passing standard benchmarks [48]. Benchmarking helps detect such integrity failures.
FAQ 3: What are the key performance indicators (KPIs) for benchmarking in this context? Key KPIs include throughput (e.g., experiments processed per day), operational efficiency (e.g., time and cost savings), error and defect rates, and data accuracy metrics [30] [80] [81]. The table below summarizes quantitative gains observed in autonomous processes.
FAQ 4: Our team is new to autonomous systems. What is a common pitfall when starting benchmarking? A common pitfall is using a poorly defined scope for the benchmarking exercise [82]. The scope must specify what aspects will be included and ensure that at least one comparable activity is available for comparison. A scope that is too broad leads to overwhelming data, while one that is too narrow may fail to provide a comprehensive view of performance gaps [82].
FAQ 5: How do we ensure our benchmarking data is comparable? Ensuring comparability is a known challenge, as data is often structured according to the specific operational framework of the organisation providing it [82]. To mitigate this:
- Standardize data formats across all instruments and systems beforehand [30].
- Use a robust Laboratory Information Management System (LIMS) to ensure data is generated consistently [30].
- Clearly document the context and methodology for every data point collected [82].
Troubleshooting Guides
Issue 1: Inconsistent or Incomparable Benchmarking Results
Problem: Results from autonomous and traditional methods cannot be meaningfully compared, leading to inconclusive findings.
| Step | Action | Expected Outcome |
|---|---|---|
| 1. Scoping | Define a realistic, well-structured scope that aligns with your objectives. Specify the exact processes, outputs, and KPIs to be compared [82]. | A clear framework for decision-making and data collection, preventing wasted resources. |
| 2. Data Audit | Audit your data sources for integrity. Standardize data formats across all existing instruments and datasets to enable direct comparison [30] [48]. | Standardized, fluid data streams that are directly comparable between the two methods. |
| 3. Tool Selection | Implement a platform that can integrate and analyze data from both traditional and autonomous workflows. Look for features that ensure data accuracy and consistency through automated validation [83]. | Reliable, consolidated data that can be confidently used for strategic analysis. |
Issue 2: Suspected Data Poisoning or Model Drift in Autonomous System
Problem: The autonomous system is producing unexpected or degraded outputs, suggesting the underlying data or model may be compromised.
| Step | Action | Expected Outcome |
|---|---|---|
| 1. Anomaly Detection | Use the platform's analytics to identify patterns, trends, and anomalies in the data. Look for subtle deviations in output quality or decision patterns [83]. | Early identification of potential integrity issues before they cause major failures. |
| 2. Secure Data Supply | Verify that your AI only ingests information from verifiable sources. Embed tamper-evident seals and implement immutable audit logs to detect manipulation [48]. | The transformation of data from an opaque liability into a transparent, traceable asset. |
| 3. Operational Transparency | Clearly document model assumptions, training data lineage, and system limitations. Use verifiable protocols to govern how data is accessed and how models are trained [48]. | A clear trail for forensic traceability, allowing you to pinpoint the source of corruption. |
Issue 3: High Maintenance Overhead in Traditional Test Automation
Problem: Traditional automated test scripts for your research software are brittle and require constant updating, draining team resources and slowing down cycles. This is a key area where autonomous methods can demonstrate gains [81] [84].
| Step | Action | Expected Outcome |
|---|---|---|
| 1. Assess Needs | Identify the most repetitive, time-consuming, and error-prone testing tasks (e.g., regression testing) [80]. | A targeted list of areas where autonomous testing will have the most impact. |
| 2. Pilot Autonomous Tool | Select and deploy an autonomous testing tool with self-healing capabilities on a well-defined project [80] [81]. | The tool automatically adapts to application changes (e.g., UI changes) without breaking. |
| 3. Measure Impact | Quantify the reduction in test maintenance time and the expansion of test coverage compared to the traditional method [81]. | Demonstrated efficiency gains and freed-up team resources for more complex tasks. |
� Quantitative Performance Benchmarks
The following tables summarize documented performance gains of autonomous methods over traditional approaches, relevant to an experimentation environment.
Table 1: Performance Gains in Autonomous Software Testing
| Metric | Traditional Method | Autonomous Method | Gain | Source |
|---|---|---|---|---|
| Test Execution Speed | Baseline (Manual) | AI-Powered | Up to 95% faster [80] | Katalon 2024 Report |
| Cost of Defect Fixing | Baseline (Post-Release) | Early Detection | Up to 93% reduction [80] | Katalon 2024 Report |
| Test Case Creation | Manual Authoring | AI-Generated | Up to 98% time reduction [81] | aqua cloud |
Table 2: Operational Advantages of Data-Driven Laboratories
| Aspect | Traditional Lab | Future/Autonomous Lab | Key Benefit | Source |
|---|---|---|---|---|
| Data Handling | Manual entry, fragmented systems [30] | Automated, consolidated repository [30] | Eliminates bottlenecks & transcription errors [30] | Autonomous.ai |
| Operation | Human-dependent, limited hours | Robotic, 24/7 operations [30] [81] | Higher repeatability & throughput [30] | Autonomous.ai |
| Decision-Making | Delayed, human-paced | Real-time AI & Edge AI analysis [30] | Faster insights & operational resilience [30] | Autonomous.ai |
Experimental Protocol: Benchmarking an Autonomous Testing Workflow
This protocol provides a methodology for comparing an autonomous testing tool against traditional scripted automation.
1. Objective: To quantitatively assess the performance, maintenance overhead, and defect detection capabilities of an autonomous testing platform versus traditional Selenium-based scripts over one development sprint.
2. Hypothesis: The autonomous testing system will demonstrate significantly lower maintenance overhead and higher adaptive capability with comparable or superior defect detection rates.
3. Materials & Reagents:
| Item | Function |
|---|---|
| Control Group: Selenium Grid | A standard for traditional, script-based web automation. Requires explicit, manually written test scripts. |
| Experimental Group: Autonomous Platform (e.g., Mabl, Testim) | An AI-native testing platform that generates, executes, and self-heals tests with minimal intervention [81] [84]. |
| Test Application | A web-based research tool with a planned UI change (e.g., a redesigned login flow) during the experiment. |
| CI/CD Pipeline (e.g., Jenkins) | An automated pipeline to trigger and execute test suites for both methods upon code changes [80]. |
4. Methodology:
Phase 1: Baseline Establishment.
- For the same login and data upload workflow, create tests using both methods.
- For Selenium: Author scripts identifying elements by IDs and XPaths.
- For the Autonomous tool: Point the AI at the application and define the critical user journeys.
- Run both test suites to establish a baseline of successful execution.
Phase 2: Introduction of Variable.
- Introduce a predefined UI change to the test application (e.g., change the ID of the login button and add a new step to the password reset flow).
- Commit the change to the codebase, triggering the CI/CD pipeline to run both test suites again.
Phase 3: Data Collection and Measurement.
- Maintenance Time: Measure the person-hours required to fix the broken Selenium scripts versus the time for the autonomous system to self-heal (or for a human to validate its self-healing).
- Test Stability: Record the number of test failures and "flaky" tests for each group after the UI change.
- Defect Detection: Log any valid defects caught by each system that were introduced by the change.
5. Data Analysis: Compare the collected metrics to validate or refute the hypothesis. The workflow for this experiment is summarized in the diagram below.
Diagram 1: Benchmarking Experiment Workflow
The Scientist's Toolkit: Research Reagent Solutions
The following tools and platforms are essential for conducting rigorous benchmarking in an autonomous research environment.
Table 3: Key Solutions for Benchmarking & Data Integrity
| Tool Category | Example Platforms | Function in Experimentation |
|---|---|---|
| Autonomous Testing Platforms | Mabl, Testim, Functionize [81] | AI-driven tools that generate, execute, and self-heal tests for research software, reducing maintenance and validating application functionality [81] [84]. |
| Workforce Benchmarking Analytics | Aura's Workforce Analytics Platform [83] | Provides real-time, data-driven insights into team performance and operational efficiency compared to industry peers, helping optimize R&D team structures [83]. |
| AI-Powered Debugging | GitHub Copilot, Snyk Code, CodeRabbit AI [84] | Acts as an intelligent assistant for researchers writing code, offering real-time bug detection, context-aware suggestions, and code explanations to improve software quality [84]. |
| Laboratory Information Management System (LIMS) | Various specialized systems [30] | The central software for managing samples, associated data, and instrumentation in the lab. A modern, integrated LIMS is non-negotiable for ensuring data integrity and fluidity [30]. |
Frequently Asked Questions (FAQs)
Q1: What is the fundamental difference between Formal Verification and simulation-based testing?
Formal Verification is a method that uses mathematical analysis to exhaustively prove that a hardware or software design behaves as intended under all possible scenarios, as defined by its specifications [85]. Unlike simulation, which tests a limited set of specific scenarios, Formal Verification does not rely on test vectors but instead uses assertions to model requirements and mathematically proves that these hold true for all possible inputs [86] [87] [85]. This makes it particularly effective for uncovering rare corner-case bugs that simulation might miss [85].
Q2: My Formal tool reports a "Bounded Proof." What does this mean and should I be concerned?
A bounded proof indicates that the Formal tool has verified an assertion is true, but only for a specific, limited number of clock cycles into the future [85]. This is common when verifying complex designs where a full proof is computationally infeasible. You should evaluate the bound depth against your design's requirements. If the bound covers the typical operational depth of your design (e.g., a protocol that stabilizes within 20 cycles is proven for 50), it may provide sufficient confidence. However, if the bound is too shallow, you may need to use abstraction techniques to reduce design complexity [88] [86].
Q3: How can I make my Formal Verification runs more efficient and complete proofs faster?
Several techniques can help reduce the verification space and improve performance [88]:
- Over-constrain Inputs: Drive critical address and data signals with fixed or partially fixed values to reduce the state space for initial debugging.
- Case Splitting: Derive more specific assertions by specifying exact conditions (e.g., cacheable vs. non-cacheable requests, hit vs. miss). The union of all cases covers the full space.
- Exploit Symmetry: If the design is symmetric (e.g., all cache ways behave identically), verify for one representative element rather than all.
- Choose Formal-Friendly Configurations: Simplify design parameters where possible (e.g., using a smaller burst size in a cache design reduces the number of cycles spent on linefills and evictions).
Q4: A counterexample (cex) was found. What are the immediate steps I should take?
A counterexample is a waveform showing a scenario where your assertion fails [86]. Your immediate steps should be:
- Analyze the Waveform: Carefully trace the sequence of events leading to the failure. The tool will show the values of all relevant signals over time.
- Isolate the Root Cause: Determine if the issue is in the Design Under Test (DUT), an incorrect constraint (
assumestatement), or a flawed assertion (assertstatement). - Fix the Issue: If the DUT is buggy, correct the RTL. If an assumption is too restrictive, relax it. If the assertion does not match the specification, correct the property.
- Re-run Verification: After making changes, re-run the proof to ensure the specific counterexample is resolved and no new ones are introduced.
Q5: When should I choose Formal Verification over simulation for a block?
Formal Verification is particularly well-suited for specific types of design elements [86]:
- Critical Control Logic: Arbiters, schedulers, and complex finite state machines.
- Well-Defined Data Transformation Blocks: Units with clear input-to-output relationships, like specific encoders or decoders.
- Nervous Logic: Any module with a history of bugs or that the designer finds particularly complex and error-prone. Formal is less suitable for very large, data-path-intensive designs (e.g., a full processor core) where the state space is enormous. In these cases, apply Formal to the critical sub-blocks [85].
Troubleshooting Guides
Problem: The Formal tool cannot complete the proof of one or more assertions, even after long runtimes, due to the large state space of the design.
| Troubleshooting Step | Action & Explanation |
|---|---|
| 1. Check Complexity | Analyze the Cone of Influence (COI) for the failing assertion. The COI includes all inputs and internal logic that can affect the property. A large COI indicates high complexity [86]. |
| 2. Reduce Verification Space | Apply space-reduction techniques [88]:- Over-constrain: Fix sub-ranges of address/data signals.- Abstract: Replace complex datapath calculations with simpler models that retain the control logic.- Case Split: Break down a complex property into simpler, mutually exclusive cases. |
| 3. Review Design for Formality | Check if the RTL can be modified to be more "formal-friendly." This involves simplifying sequential logic or breaking large state machines into smaller ones [86]. |
| 4. Use Bounded Proofs | If a full proof is impossible, accept a bounded proof. Quantify the depth and ensure it is reasonable for the design's operation [85]. |
Issue: False Failures (Counterexamples are Invalid)
Problem: The tool produces a counterexample that would not occur in the real operation of the design.
| Troubleshooting Step | Action & Explanation |
|---|---|
| 1. Check Assumptions | This is the most common cause. Review all assume statements (constraints) to ensure they accurately reflect the environment's legal input behavior. The counterexample likely violates an unstated assumption. |
| 2. Verify Initialization | Ensure the design is properly reset and initial state assumptions are correct. False failures often occur during the first few cycles after reset. |
| 3. Inspect Waveform | Trace the invalid scenario. Identify which signal behavior is unrealistic and add a corresponding constraint to prevent it. |
Issue: Failure to Prove a Simple Property
Problem: An assertion that is believed to be true cannot be proven, and no counterexample is found.
| Troubleshooting Step | Action & Explanation |
|---|---|
| 1. Check for Contradictory Constraints | Review the set of assume statements. Over-constraining or using conflicting assumptions can make the solver's job impossible, as no valid input sequence satisfies all constraints. |
| 2. Weaken the Property | The assertion might be too strong. Try to prove a weaker version of the property (e.g., over a shorter sequence or with fewer pre-conditions) to isolate the issue. |
| 3. Review Tool Logs | Check for warnings about design complexity, trivially true properties, or other analysis hints from the tool. |
Experimental Protocols for Key Verification Activities
Protocol 1: Creating End-to-End Data Integrity Assertions
This methodology verifies that data is not corrupted as it flows through a system, such as a cache or communication protocol [88].
- Define Oracles: Use symbolic variables (oracles) for critical inputs like address (
A) and data (D). These are undetermined constants that allow the Formal tool to exhaustively verify all possibilities [88]. - Write Core Properties: Formulate two primary assertions:
- Write-Read Consistency: After a write request to address
Awith dataD, the subsequent read request toAmust returnD. - Read-Read Consistency: Two consecutive read requests to the same address must return the same data.
- Write-Read Consistency: After a write request to address
- Model the Environment: Connect a model of the external memory (e.g., a Content-Addressable Memory instance) to provide a reference for correct data [88].
- Refine and Reduce: If proofs are slow, apply reduction techniques like fixing oracle values or case-splitting based on hit/miss predictions [88].
Protocol 2: Setting Up a Basic Formal Testbench
This protocol outlines the initial steps for verifying a block using Formal [86].
- Constraint Inputs: Use SystemVerilog
assumedirectives to define the legal operating space for the DUT's inputs according to the protocol specification. - Write Checkers: Use SystemVerilog
assertdirectives to encode the design's specification as properties on its outputs and internal states. - Define Coverage: Use SystemVerilog
coverdirectives to ensure that meaningful scenarios and states can be reached by the Formal tool. This validates that the testbench is not over-constrained. - Run and Analyze: Feed the DUT, constraints, and checkers to the Formal tool. Analyze counterexamples for failures and review coverage goals to ensure the space is being explored.
Protocol 3: Verification Space Reduction Techniques
When facing complexity issues, systematically apply these methods [88].
| Technique | Application | Example |
|---|---|---|
| Input Over-constraining | Drastically reduce state space for initial debugging. | Fix target_addr and target_data signals to specific values. |
| Range Limiting | A less aggressive form of over-constraining. | Fix only a sub-range (e.g., the lower 8 bits) of an address bus. |
| Bit-Slicing | Verify data integrity one bit at a time. | Check an assertion for only bit 0 of the data bus, then bit 1, etc. |
| Case Splitting | Verify exclusive scenarios separately. | Derive separate assertions for cacheable vs. non-cacheable requests. |
| Symmetry Reduction | Leverage design symmetry to reduce the number of properties. | If a cache has 8 identical ways, verify properties for only way 0. |
The Scientist's Toolkit: Key Research Reagent Solutions
| Item/Technique | Function in Formal Verification |
|---|---|
| SystemVerilog Assertions (SVA) | The language construct used to write constraints (assume), checkers (assert), and coverage points (cover) for Hardware Description Languages [86]. |
| Symbolic Variables (Oracles) | Constant signals with no defined value, allowing the tool to exhaustively verify all possibilities for that variable (e.g., all addresses, all data) [88]. |
| Cone of Influence (COI) | The set of all inputs, outputs, and internal variables of the DUT that influence a particular assertion. The tool reduces the problem to analyzing this cone [86]. |
| Formal Core | A modern refinement of the COI; a subset of the logic that is the minimal set required to prove a given assertion [86]. |
| Counterexample (Cex) | A waveform generated by the Formal tool that shows a specific sequence of inputs and states that leads to an assertion failure. This is the primary debugging artifact [86] [85]. |
| Bounded Proof | A result where an assertion is proven true only for execution paths up to a specific cycle depth. This is common for complex designs [85]. |
| Certora Prover | A formal verification tool specifically designed for smart contracts, using a high-level specification language to prove correctness [87]. |
| Why3 | A platform for program verification that allows users to write specifications and generate proof obligations for various automated theorem provers [87]. |
Workflow and Logic Diagrams
Formal Verification Process Flow
Cone of Influence (COI) Analysis
FAQs: Core Concepts and Troubleshooting
Q1: What is the fundamental difference between model accuracy and robustness?
- Accuracy measures how well a model performs on clean, familiar, and representative test data.
- Robustness measures how reliably the model performs when inputs are noisy, incomplete, adversarial, or from a different distribution (Out-of-Distribution). A model can be highly accurate in a lab setting but brittle in real-world conditions [89].
Q2: Our model performs well on standard test sets but fails in production. What are the common causes?
This is a classic sign of a non-robust model. Common causes include [89]:
- Overfitting to training data: The model learned patterns too specific to the training set and fails to generalize.
- Lack of data diversity: The training data does not capture the full range of scenarios encountered in production.
- Biases in data: Skewed or imbalanced datasets can lead to unfair or unstable predictions.
- Unseen input distributions: Production data differs from the training data (distribution shift).
Q3: What is an "adversarial example" and why is it a security concern?
An adversarial example is an input deliberately modified to deceive an AI model. These modifications often appear indistinguishable from legitimate data to the human eye but cause the model to make a classification error or an absurd decision [90]. They are a critical security concern because they can be used to bypass AI-powered security systems. For instance, an attacker could manipulate an image to evade a content filter or alter a file to fool a malware detector [91].
Q4: During adversarial training, our model becomes too conservative and its overall performance drops. How can we mitigate this?
This is a known trade-off. To mitigate it:
- Carefully balance your dataset: Ensure the ratio of adversarial examples to clean data is appropriate; flooding the training set with adversarial data can harm generalization.
- Use a variety of attacks: Incorporate adversarial examples generated using multiple methods (e.g., FGSM, PGD) to prevent the model from over-optimizing against a single attack type [90].
- Prioritize data quality: The foundation of a robust model is high-quality, diverse training data. Rigorous data cleaning and diversification can reduce the need for overly aggressive adversarial training [90] [89].
Q5: How can we systematically identify edge cases and failure modes in our complex model?
Employ a Red Teaming approach. This involves proactively simulating adversarial attacks to identify system weaknesses [90] [89]. This can be done through:
- Structured evaluation pipelines: Develop custom evaluation pipelines that go beyond standard benchmarks to match your industry-specific conditions [89].
- Adversarial example generation tools: Use open-source libraries like CleverHans or Adversarial Robustness Toolbox (ART) to systematically generate attacks and probe for failures [90].
Experimental Protocols and Data
Table 1: Taxonomy and Impact of Common Adversarial Attacks
This table classifies adversarial attacks to help diagnose vulnerabilities in your system.
| Attack Type | Phase of Operation | Objective | Example & Potential Impact |
|---|---|---|---|
| Data Poisoning [90] | Training | Inject corrupted or mislabeled data into the training set. | A backdoor is inserted; the model behaves normally until it sees a specific trigger, compromising long-term system integrity. |
| Evasion Attack [90] | Inference | Cause a trained model to misclassify a specific input. | Placing stickers on a "Stop" sign causes an autonomous vehicle to misread it [90]. This directly subverts system decision-making. |
| Targeted Attack [90] | Inference | Cause the model to produce a specific incorrect outcome. | Tricking a facial recognition system to classify an unauthorized person as a specific, authorized employee. |
| Untargeted Attack [90] | Inference | Cause the model to produce any incorrect outcome. | Causing a spam filter to misclassify a spam email as "not spam." |
| Word-Level Attack [92] | Inference (NLP/Code) | Disrupt model understanding by altering words in the input. | An LLM for code generates incorrect or insecure code when key words in the prompt are changed, breaking semantic understanding [92]. |
Table 2: Quantitative Metrics for Robustness Evaluation
Use these metrics to objectively measure and track your model's robustness.
| Metric Category | Specific Metric | Description & Interpretation |
|---|---|---|
| Performance Under Attack | Adversarial Accuracy / Recall [90] | Model's accuracy/recall on a dataset containing adversarial examples. A large drop from clean accuracy indicates low robustness. |
| Robustness Metrics | Reduction in Exploitable Attack Paths [93] | Tracks how many validated attack chains are eliminated over time by security improvements. |
| Operational Security | Mean Time to Remediate (MTTR) Validated Exposures [93] | Tracks how quickly security teams fix confirmed weaknesses revealed by testing. |
| Uncertainty Quality | Confidence Calibration [89] | Measures if a model's predicted confidence (e.g., "99% sure") matches its actual correctness. A miscalibrated model is dangerously overconfident when wrong. |
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Tools and Materials for Adversarial Robustness Research
This table lists key software tools and their primary functions in adversarial testing.
| Tool / Resource | Type | Primary Function in Adversarial Testing |
|---|---|---|
| Adversarial Robustness Toolbox (ART) [90] | Software Library | A comprehensive open-source library for evaluating and improving model robustness, offering a wide range of attacks and defenses. |
| CleverHans [90] | Software Library | A Python library developed by Google researchers specifically designed to assess model vulnerability to adversarial examples. |
| TextAttack [90] | Software Framework | A framework specialized in generating attacks and evaluating robustness for Natural Language Processing (NLP) models. |
| BigQuery DataFrames [94] | Data Synthesis Tool | A tool that can be used for data synthesis to expand a small, manually created "seed" dataset of adversarial queries for more comprehensive testing. |
| LLM-as-a-Judge [95] | Evaluation Technique | Using a language model to automatically assess the quality of outputs, such as the relevance of retrieved context in a RAG system or the helpfulness of a response. |
Methodologies and Workflows
Workflow 1: Adversarial Testing for Generative AI Models
This workflow, based on industry best practices, provides a structured methodology for testing generative AI systems [94].
Adversarial Testing Workflow for Generative AI
Workflow 2: Robustness Evaluation Framework
This diagram outlines a general methodology for evaluating the robustness of any ML model, focusing on key testing approaches [89] [91].
Core Methods for Model Robustness Evaluation
This technical support center provides troubleshooting guides and FAQs to help researchers address common data integrity challenges in autonomous experimentation.
Frequently Asked Questions (FAQs)
Q1: What is the practical difference between data completeness and data accuracy? Data completeness measures whether all necessary data is present, while accuracy reflects whether the data correctly describes the real-world objects or events. Data can be complete but inaccurate (e.g., all customer records are present but contain duplicate entries), or accurate but incomplete (e.g., correct data points are missing key geographic information needed for analysis) [96].
Q2: Our RNA-Seq data fails the "Per base sequence content" module in FastQC. Is this a problem? Not necessarily. This module often gives a "FAIL" for RNA-seq data due to the 'random' hexamer priming during library preparation, which can cause an enrichment of particular bases in the first 10-12 nucleotides. This is an expected artifact of the protocol, not an indication of low-quality data [97].
Q3: How can I quickly check if a FASTA file contains DNA or protein sequences?
You can use a frequency-based method by sampling the file. Count the occurrences of the letters A, T, G, and C. If the sum of their frequencies is very high (e.g., over 50-90% of the sequence characters), it is likely nucleotide data. Protein sequences will have a much more even distribution of letters across the entire alphabet [98]. Tools like BioRuby's Bio::Sequence#guess method automate this check [98].
Q4: What is a simple formula to calculate data completeness for a specific field? A fundamental formula for attribute-level completeness is: Data Completeness = (Number of Complete Records / Total Number of Records) x 100% [99] A "complete record" is one where the required field is populated with a valid value.
Troubleshooting Guides
Guide 1: Diagnosing and Resolving Low Data Completeness
Symptoms: Missing values in critical fields, inability to run analyses due to null values, biased analytical results.
Investigation and Resolution Steps:
- Profile Your Data: Use data profiling tools to analyze patterns and frequencies of missing values across your dataset. Calculate the null rate for each essential attribute [96].
- Identify the Root Cause: The solution depends on the underlying problem.
- Check the table below to match your symptom to the likely cause and solution.
| Symptom | Likely Cause | Recommended Solution |
|---|---|---|
| Missing values in specific fields from manual entry | Human error during data entry [96] | Implement mandatory field validation and drop-down menus in data entry forms [99] [96]. |
| Whole tables or data sources are missing | Inadequate data collection processes or integration failures [96] | Standardize data collection procedures and use data integration/synchronization tools [99] [96]. |
| Data is available in one system but not another | Data integration challenges during ETL (Extract, Transform, Load) [96] | Review and fix data mapping rules between systems. Automate data validation checks post-integration [96]. |
| Outdated or stale information | Lack of regular data updates [99] | Establish scheduled data cleansing and enrichment processes [99]. |
- Implement Preventive Measures:
- Standardize: Create clear, documented standards for data collection and entry [96].
- Automate: Use automation to fill data gaps where possible, reducing reliance on manual input [99].
- Monitor: Continuously track completeness metrics (like null rate) with a data observability platform to detect issues early [100].
Guide 2: Addressing Poor Signal Quality in Sequencing Data (FastQC)
Symptoms: Warnings or failures in multiple FastQC modules, low-quality scores, unusual sequence content.
Investigation and Resolution Steps:
- Understand the FastQC Report: Consult the FastQC manual to interpret each module. Pay special attention to "Per base sequence quality" and "Adapter Content" [97].
- Differentiate Between Expected and Worrisome Issues:
- Expected: A gradual drop in quality scores towards the 3' end of reads is common due to signal decay or phasing during Illumina sequencing [97].
- Worrisome: Sudden drops in quality, low scores across the entire read, or unexpected sequences (e.g., adapter contamination) indicate potential problems [97].
- Take Corrective Action: The action depends on the specific issue found.
| FastQC Module | Worrisome Result | Potential Cause | Corrective Action |
|---|---|---|---|
| Per base sequence quality | Sudden, severe drop in scores across all reads | Instrument failure (e.g., manifold burst) at the sequencing facility [97]. | Contact your sequencing facility for resolution. |
| Per base sequence quality | Consistently low scores across the entire read | Overclustering on the flow cell [97]. | Request less sequencing depth per lane in future runs. |
| Adapter Content | High levels of adapter sequence detected | Adapters are being sequenced due to short insert size. | Use a tool like cutadapt or Trimmomatic to trim adapter sequences from your reads. |
| Overrepresented sequences | Sequence appears in >0.1% of total [97] | Contamination (vector, adapter) or biological (highly expressed transcript). | BLAST the sequence to identify it. If contamination, remove the affected reads. |
Guide 3: Improving Reproducibility of Analyses
Symptoms: Inability to replicate your own or others' results, discrepancies when re-running analyses.
Investigation and Resolution Steps:
- Follow the GRDI Principles: Adhere to principles of Accuracy, Completeness, Reproducibility, Understandability, Interpretability, and Transferability in all data handling [54].
- Create a Data Dictionary: Before and during data collection, write a clear data dictionary that explains all variable names, coding for their categories, and units of measurement [54].
- Preserve Raw Data: Always save the raw, unprocessed data in its original form in multiple locations. This allows you to re-run processing steps if changes are needed [54].
- Use Standard File Formats: Save data in accessible, general-purpose file formats (e.g., CSV for tabular data) to ensure long-term accessibility and transferability across systems [54].
- Select Appropriate Reproducibility Metrics: A scoping review has identified over 50 different metrics for quantifying reproducibility. The choice of metric (e.g., a specific formula, statistical model, or framework) should be aligned with your specific research question and project goals [101].
Standardized Metrics for Data Integrity
The tables below summarize key quantitative metrics for assessing data quality.
Table 1: Core Data Quality Metrics
| Metric | Definition | Formula / Calculation Method |
|---|---|---|
| Completeness (Attribute-level) | Percentage of required data fields populated with valid values [99]. | (Number of Complete Records / Total Number of Records) * 100% [99] |
| Accuracy (F1 Score) | Harmonic mean of precision and recall, measuring correctness against a source of truth [102]. | F1 = 2 * (Precision * Recall) / (Precision + Recall) [102] |
| Traceability | Proportion of data elements that can be tracked to a verifiable source [102]. | (Number of traceable data elements / Total data elements) * 100% [102] |
| Null Rate | Percentage of empty (null) values in a dataset [100]. | (Number of null entries / Total number of entries) * 100% [100] |
Table 2: Impact of Data Source and Technology on Reliability
Findings from a quality improvement study on real-world data (n=120,616 patients) showing how advanced approaches improve key metrics. [102]
| Data Reliability Dimension | Traditional Approach (Single-source structured data) | Advanced Approach (Multiple sources + AI) |
|---|---|---|
| Accuracy (F1 Score) | 59.5% | 93.4% |
| Completeness | 46.1% (95% CI, 38.2%-54.0%) | 96.6% (95% CI, 85.8%-107.4%) |
| Traceability | 11.5% (95% CI, 11.4%-11.5%) | 77.3% (95% CI, 77.3%-77.3%) |
Experimental Protocols
Protocol 1: Measuring Data Completeness and Accuracy
This protocol outlines a method for quantifying data completeness and accuracy, based on approaches used in real-world evidence studies [102].
- Define Critical Variables: Identify the data fields essential for your analysis.
- Establish a Source of Truth: Determine the gold-standard source for validating each variable (e.g., manual annotation of clinical encounters by multiple clinicians with a minimum inter-rater reliability Cohen κ score of 0.7) [102].
- Calculate Completeness:
- For each patient record, check the availability of each critical variable.
- Use the formula in Table 1 to calculate an overall completeness percentage.
- Calculate Accuracy (F1 Score):
- On a subset of data, compare the values in your dataset against the source of truth.
- Calculate Precision (True Positives / (True Positives + False Positives)) and Recall (True Positives / (True Positives + False Negatives)).
- Compute the F1 Score using the formula in Table 1 [102].
Protocol 2: Performing Quality Control on Sequencing Data with FastQC
This protocol describes a standard workflow for assessing the quality of raw sequencing data [103] [97].
- Obtain FastQC: Download the tool from the Babraham Institute website. Ensure you have a Java Runtime Environment installed [103].
- Run FastQC:
- Command Line:
fastqc sequencedata.fastq -o /output/directory/ - The tool accepts FASTQ, BAM, or SAM files [103].
- Command Line:
- Interpret the HTML Report: Open the generated HTML report. Systematically review each module, focusing on:
- Make Data-Driven Decisions: Use the "WARNING" and "FAIL" flags as guides for further investigation and processing (e.g., quality trimming, adapter removal) as outlined in Troubleshooting Guide 2.
Workflow Visualization
Data Quality Assessment Workflow
FastQC Analysis Workflow
The Scientist's Toolkit: Essential Research Reagents & Solutions
| Item | Function |
|---|---|
| FastQC | A quality control tool that provides a quick impression of raw sequencing data from high throughput pipelines. It checks for potential problems across multiple analysis modules [103]. |
| Data Dictionary | A separate document that explains all variable names, category codings, and units. It is crucial for ensuring data is interpretable and used correctly by all researchers [54]. |
| Controlled Vocabularies | Standardized sets of terms used for data and metadata. They ensure consistency and comparability of data across different studies and systems [54]. |
| Adapter Trimming Tool (e.g., cutadapt) | A software utility used to remove adapter sequences from next-generation sequencing reads, which is often necessary when the fragment size is shorter than the read length [97]. |
| BioRuby Suite | A collection of Ruby tools for bioinformatics, which includes utilities like Sequence#guess to help determine if a sequence is DNA or protein [98]. |
| Privacy-Preserving Record Linkage Tools | Software that allows linking of patient data from different sources (e.g., EHR, claims) without exposing personally identifiable information, enabling more complete data for analysis [102]. |
Conclusion
Ensuring data integrity in autonomous experimentation is not a single step but a continuous commitment that must be embedded throughout the research lifecycle. By integrating the foundational principles of ALCOA++, implementing robust methodological controls, proactively troubleshooting systemic risks, and employing rigorous, multi-layered validation, researchers can build autonomous systems worthy of trust. The future of AI-driven biomedical research hinges on this integrity—it is the essential foundation for producing reliable, reproducible results, accelerating drug development, and ultimately, delivering safe and effective therapies to patients. Moving forward, the industry must prioritize cross-sector collaboration, develop new standards for AI transparency, and continuously adapt integrity safeguards to keep pace with technological innovation.
References
- 1. The AI Agents of Tomorrow Need Data Integrity [https://spectrum.ieee.org/data-integrity]
- 2. Challenges & solutions for lab data integrity [https://biosero.com/blog/ensuring-data-integrity-in-automated-labs/]
- 3. A critical path to safe medicines: Why data integrity matters ... [https://www.quotientsciences.com/blog/critical-path-safe-medicines-why-data-integrity-matters-drug-development]
- 4. What Is Data Integrity? [https://kneat.com/article/what-is-data-integrity/]
- 5. Implications of AI regulation for data integrity [https://www.europeanpharmaceuticalreview.com/news/215608/implications-of-ai-regulation-for-data-integrity/]
- 6. AI-Driven Data Integrity: Ensuring Trust, Security, and ... - Narwal [https://narwal.ai/ai-driven-data-integrity-ensuring-trust-security-and-compliance/]
- 7. Artificial Intelligence and Privacy – Issues and Challenges [https://ovic.vic.gov.au/privacy/resources-for-organisations/artificial-intelligence-and-privacy-issues-and-challenges/]
- 8. Data Integrity in the AI Era: Breaking Silos with Enterprise ... [https://narwal.ai/data-integrity-in-the-ai-era-breaking-silos-with-enterprise-data-fabric/]
- 9. Reviewing Pharmaceutical Threats in 2025 [Threat Note] [https://cybelangel.com/blog/pharmaceutical-threats-2025/]
- 10. FDA Enforcement Flags Data Integrity Risks at Overseas ... [https://f2labs.com/technotes/2025/06/06/fda-enforcement-flags-data-integrity-risks-at-overseas-labs/]
- 11. Troubleshooting in pharmaceutical manufacturing processes [https://www.hwi-group.de/en/blog/details/troubleshooting-in-pharmaceutical-manufacturing-processes-root-cause-analysis-of-quality-defects]
- 12. The Importance of Data Integrity in the Life Sciences Sector [https://pharmallies.com/key-faqs-on-ensuring-data-integrity-in-the-life-sciences-industry/]
- 13. Drug Discovery Assays Support—Troubleshooting [https://www.thermofisher.com/us/en/home/technical-resources/technical-reference-library/drug-discovery-development-support-center/drug-discovery-assays-support/drug-discovery-assays-support-troubleshooting.html]
- 14. How to Ensure EHR Data Integrity [https://www.openclinica.com/blog/how-to-ensure-ehr-data-integrity/]
- 15. The ALCOA++ Principles for Data Integrity in Clinical Trials [https://www.quanticate.com/blog/alcoa-principles]
- 16. ALCOA, ALCOA+ and ALCOA++ Principles | Ensuring Data ... [https://www.pharmaguideline.com/2018/12/alcoa-to-alcoa-plus-for-data-integrity.html]
- 17. FAIR Principles [https://www.go-fair.org/fair-principles/]
- 18. An automated solution for measuring the progress toward ... [https://www.sciencedirect.com/science/article/pii/S2666389921002324]
- 19. Data Integrity in Labs: Why It's Essential and How to ... [https://www.scisure.com/blog/data-integrity-in-labs-why-its-essential-and-how-to-achieve-it]
- 20. AI Troubleshooting Guide 2025 [https://www.rapidinnovation.io/post/ai-agents-for-technical-troubleshooting]
- 21. Research integrity in the era of artificial intelligence [https://pmc.ncbi.nlm.nih.gov/articles/PMC11224801/]
- 22. The Analytics Development Lifecycle (ADLC) [https://www.getdbt.com/resources/the-analytics-development-lifecycle]
- 23. Data & AI Lifecycle 101 [https://noma.security/blog/what-is-the-data-and-ai-lifecycle/]
- 24. What Is a Data Dictionary? Definition, Types, and Practical ... [https://www.acceldata.io/blog/what-is-a-data-dictionary-definition-types-and-practical-applications]
- 25. Data Dictionary Best Practices [https://www.secoda.co/learn/data-dictionary-best-practices]
- 26. The Art of Troubleshooting for Customer Support ... [https://www.helpscout.com/helpu/art-of-troubleshooting-support/]
- 27. The complete guide to customer service troubleshooting [https://devrev.ai/blog/customer-service-troubleshooting]
- 28. An open-source append only ledger | Trillian [https://transparency.dev/]
- 29. Transparency Logs: A Verifiable Transport Layer | Trillian [https://transparency.dev/articles/logs-a-verifiable-transport-layer/]
- 30. The Data-Driven Revolution: What the Lab of the Future ... [https://www.autonomous.ai/ourblog/the-data-driven-revolution-what-the-lab-of-the-future-looks-like]
- 31. Tamper-Evident Logs [https://news.ycombinator.com/item?id=25995034]
- 32. LLM03:2025 Supply Chain - OWASP Gen AI Security Project [https://genai.owasp.org/llmrisk/llm03-training-data-poisoning/]
- 33. Data Management and Audit Trails: Ensuring Regulatory ... [https://www.labmanager.com/data-management-and-audit-trails-ensuring-regulatory-compliance-34175]
- 34. GLP Audit Trails: A Guide to Compliant File Systems [https://intuitionlabs.ai/articles/glp-compliant-file-system-audit-trails]
- 35. Audit Trail Requirements: Guidelines for Compliance and Best ... [https://www.inscopehq.com/post/audit-trail-requirements-guidelines-for-compliance-and-best-practices]
- 36. Data Quality and Audit Trails - Examples and Best ... [https://dqops.com/data-quality-and-audit-trails/]
- 37. PharmaChain: Blockchain-based drug supply chain ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10362317/]
- 38. A data-driven scenario-based drug traceability and ... [https://www.sciencedirect.com/science/article/pii/S2772662225000761]
- 39. Blockchain: A Game-Changer for Pharma Supply Chains [https://binariks.com/blog/blockchain-pharma-supply-chain/]
- 40. Real World Blockchain Uses in the Pharmaceutical Industry [https://www.drugpatentwatch.com/blog/real-world-blockchain-uses-in-the-pharmaceutical-industry/?srsltid=AfmBOoqZRT03JGowWhP_JtAI6Hvgu1lFpeZXnG44csKG6uMTlTaCHTEn]
- 41. Real-Time Data Integrity Nexus: Autonomous Quality ... [https://al-kindipublishers.org/index.php/jcsts/article/view/11242]
- 42. AI-Driven Quality Control: Revolutionizing Defect Detection [https://www.elisaindustriq.com/knowledge-center/blog/ai-driven-quality-control-in-manufacturing]
- 43. How to Use AI for Quality Control [https://sciotex.com/how-to-use-ai-for-quality-control/]
- 44. The Ultimate Guide To Data Lineage [https://www.montecarlodata.com/blog-data-lineage/]
- 45. What Is Data Lineage? Examples, Tools, and Use Cases [https://www.ardoq.com/knowledge-hub/data-lineage]
- 46. Top 5 Open Source Data Lineage Tools (With User Reviews) [https://www.montecarlodata.com/blog-open-source-data-lineage-tools/]
- 47. Model documentation best practices - VerifyWise AI Lexicon [https://verifywise.ai/lexicon/model-documentation-best-practices]
- 48. The Battle For Data Integrity: Why Trust Is The Current ... [https://www.forbes.com/councils/forbesbusinesscouncil/2025/07/07/the-battle-for-data-integrity-why-trust-is-the-current-frontier-in-ai/]
- 49. Top 6 Data Lineage Tools: A Comprehensive Comparison [https://www.acceldata.io/blog/data-lineage-tools]
- 50. Managing human failures: Overview [https://www.hse.gov.uk/humanfactors/topics/humanfail.htm]
- 51. Overview of Failure Mode and Effects Analysis (FMEA) [https://pmc.ncbi.nlm.nih.gov/articles/PMC10229026/]
- 52. 8 MLOps Best Practices for Scalable, Reliable ML ... [https://cloud.folio3.com/blog/mlops-best-practices/]
- 53. Machine learning experiments: approaches and best ... [https://nebius.com/blog/posts/machine-learning-experiments]
- 54. Guidelines for Research Data Integrity (GRDI) [https://www.nature.com/articles/s41597-024-04312-x]
- 55. Why Did My AI Fail? A 2025 Guide to Root Cause Analysis ... [https://mixflow.ai/blog/why-did-my-ai-fail-a-2025-guide-to-root-cause-analysis-for-emergent-behaviors]
- 56. Process Failure Mode & Effects Analysis (PFMEA) in Lean ... [https://www.6sigma.us/fmea/process-failure-mode-effects-analysis-pfmea/]
- 57. What Is Data Poisoning? [Examples & Prevention] [https://www.paloaltonetworks.com/cyberpedia/what-is-data-poisoning]
- 58. What Is Data Poisoning? [https://www.ibm.com/think/topics/data-poisoning]
- 59. What Is Data Poisoning? [https://www.crowdstrike.com/en-us/cybersecurity-101/cyberattacks/data-poisoning/]
- 60. Data poisoning: Prevention strategies to keep your data safe [https://www.manageengine.com/log-management/blog/data-poisoning-prevention-strategies-to-keep-your-data-safe.html]
- 61. Data Integrity–Based Methodology and Checklist for ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC6315242/]
- 62. How To Build A Data Quality Integrity Framework [https://www.montecarlodata.com/blog-how-to-build-a-data-quality-integrity-framework/]
- 63. A Closer Look at Why They Fail When Completing Tasks [https://arxiv.org/html/2508.13143v1]
- 64. Learning-based Bayesian Inference for Testing of ... [https://mit-realm.github.io/neural-langevin-website/]
- 65. Graceful Degradation [https://risknowlogy.com/articles/detail/17309/]
- 66. First-of-its-kind standard on AI and machine learning in ... [https://www.lexpert.ca/news/technology-law/first-of-its-kind-standard-on-ai-and-machine-learning-in-research-aims-to-preserve-data-integrity/393681]
- 67. 8 MLOps Best Practices Every ML Team Should Follow in ... [https://www.azilen.com/blog/mlops-best-practices/]
- 68. Training Course: Achieving Data Quality and Integrity in ... [https://www.fda.gov/emergency-preparedness-and-response/outreach-and-professional-development-activities/training-course-achieving-data-quality-and-integrity-maximum-containment-laboratories]
- 69. 11 MLOps Best Practices Explained in 2025 [https://www.tredence.com/blog/mlops-a-set-of-essential-practices-for-scaling-ml-powered-applications]
- 70. Improving Data Integrity in Samples Obtained From Web- ... [https://www.researchprotocols.org/2025/1/e69956]
- 71. Best Tools for ML Experiment Tracking and Management in ... [https://neptune.ai/blog/best-ml-experiment-tracking-tools]
- 72. STM Research Integrity Day 2025 [https://stm-assoc.org/events/stm-innovation-integrity-days-2025/stm-research-integrity-day-2025/]
- 73. Best practices for running and logging ML experiments [https://medium.com/data-science-collective/best-practices-for-running-and-logging-ml-experiments-a6e7ef5f2878]
- 74. Text has enhanced contrast | ACT Rule | WAI [https://www.w3.org/WAI/standards-guidelines/act/rules/09o5cg/]
- 75. Verification of Multi-Layered Assignment Problems [https://arxiv.org/abs/2105.10434]
- 76. Color Contrast Guidelines for Text & UI Accessibility [https://daily.dev/blog/color-contrast-guidelines-for-text-and-ui-accessibility]
- 77. Google Logo 4 Colors #4285f4, #ea4335, #fbbc05, #34a853 [https://colorswall.com/palette/170959]
- 78. Google New Color Palette [https://www.color-hex.com/color-palette/51381]
- 79. Color palette - Hex #4285f4 - Partner Marketing Hub - Google [https://partnermarketinghub.withgoogle.com/brands/google-photos/visual-identity/color-palette/]
- 80. A beginner's guide to autonomous testing: Key benefits ... [https://owlity.ai/articles/a-beginners-guide-to-adopting-autonomous-qa-solutions]
- 81. Autonomous Software Testing: The Ultimate Guide for QA ... [https://aqua-cloud.io/autonomous-software-testing-ultimate-guide-with-steps-tools/]
- 82. The power of benchmarking [https://www.quality.org/article/power-benchmarking]
- 83. Workforce Benchmarking Tools: Optimize Decision-Making [https://blog.getaura.ai/workforce-benchmarking-tools-support-data-driven-growth]
- 84. AI Bug Fixing & Autonomous Testing: A Developer's Guide [https://www.arsturn.com/blog/ai-bug-fixing-and-autonomous-testing-the-ultimate-guide]
- 85. Understanding Formal Verification - Verification Horizons [https://blogs.sw.siemens.com/verificationhorizons/2024/09/05/understanding-formal-verification/]
- 86. A Gentle Introduction to Formal Verification [https://www.systemverilog.io/verification/gentle-introduction-to-formal-verification/]
- 87. Formal Verification: Using Mathematics to Ensure Resilient ... [https://morpho.org/blog/formal-verification-using-mathematics-to-ensure-resilient-code/]
- 88. Formal verification best practices: checking data corruption [https://codasip.com/2023/10/10/formal-verification-best-practices-checking-data-corruption/]
- 89. Model Robustness Explained: OOD, Adversarial and Best... Testing [https://invisibletech.ai/blog/model-robustness-explained-methods-testing-and-best-practice]
- 90. The Adversarial Robustness Guide to Securing Your AI in 2025 [https://www.efficiant.com/en/blog-post/le-guide-de-la-robustesse-adversariale-pour-securiser-votre-ia-en-2025]
- 91. the Robustness of AI Testing : Ensuring... - DEV Community Systems [https://dev.to/radha_4c842d8e4362a7cdd9c/testing-the-robustness-of-ai-systems-ensuring-reliability-in-real-world-scenarios-1c69]
- 92. Adversarial Attack Classification and Robustness Testing ... [https://www.arxiv.org/abs/2506.07942]
- 93. The Future of Security Testing: A 2025 Guide to Adversarial ... [https://www.breachlock.com/resources/blog/the-future-of-security-testing-a-2025-guide-to-adversarial-exposure-validation/]
- 94. Adversarial Testing for Generative AI | Machine Learning [https://developers.google.com/machine-learning/guides/adv-testing]
- 95. A complete guide to RAG evaluation: metrics, testing and best practices [https://www.evidentlyai.com/llm-guide/rag-evaluation]
- 96. What Is Data Completeness? Definition, Examples, And KPIs [https://www.montecarlodata.com/blog-what-is-data-completeness/]
- 97. Quality control using FastQC | Training-modules - GitHub Pages [https://hbctraining.github.io/Training-modules/planning_successful_rnaseq/lessons/QC_raw_data.html]
- 98. Validation - Test What Type Of Data The Fasta Format Input ... [https://www.biostars.org/p/82482/]
- 99. Data Completeness Metrics: Measuring Data Quality [https://www.getcensus.com/ops_glossary/data-completeness-metrics-measuring-data-quality]
- 100. What are Data Quality Metrics? Measuring Data Integrity [https://www.acceldata.io/article/what-are-data-quality-metrics]
- 101. A scoping review on metrics to quantify reproducibility [https://pubmed.ncbi.nlm.nih.gov/40894102/]
- 102. Implementing Accuracy, Completeness, and Traceability ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11894483/]
- 103. FastQC A Quality Control tool for High Throughput ... [https://www.bioinformatics.babraham.ac.uk/projects/fastqc/]