Building Trust in Science: A 2025 Guide to Research Integrity in Materials Science & Engineering
This article provides a comprehensive guide for researchers and professionals on upholding research integrity in materials science.
Building Trust in Science: A 2025 Guide to Research Integrity in Materials Science & Engineering
Abstract
This article provides a comprehensive guide for researchers and professionals on upholding research integrity in materials science. It covers foundational principles, including the latest 2025 ORI definitions of misconduct and the materials science research cycle. The guide explores methodological applications of AI-powered image checking tools like Proofig, troubleshooting for common issues like image duplication and self-plagiarism, and validation techniques through robust training and electronic oversight systems. By synthesizing these areas, the article offers a actionable framework to prevent misconduct, enhance data credibility, and accelerate the reliable translation of materials research into real-world applications.
Understanding Research Integrity: Core Principles and the 2025 Landscape
Research misconduct represents a fundamental breach of the ethical principles that underpin the scientific enterprise. In materials science, where findings directly influence technological advancement and product development, maintaining rigorous standards of integrity is paramount. The Office of Research Integrity (ORI) provides the foundational definition that has guided research integrity policy for decades: research misconduct is strictly defined as fabrication, falsification, or plagiarism (FFP) in proposing, performing, reviewing, or reporting research [1]. It is crucial to note that this definition explicitly excludes honest error or differences of opinion [2]. This technical guide examines the current state of FFP within the context of materials science research, incorporating 2025 regulatory updates, detection methodologies, and preventative frameworks essential for researchers, scientists, and drug development professionals dedicated to upholding the highest standards of scientific integrity.
Core Definitions and Regulatory Framework
The FFP Triad: Official Definitions
The U.S. Office of Research Integrity precisely defines the three core elements of research misconduct [2]:
- Fabrication: Making up data or results and recording or reporting them as actual findings. In materials science, this could involve inventing characterization data, such as spectroscopic readings or mechanical property measurements.
- Falsification: Manipulating research materials, equipment, or processes, or changing or omitting data or results such that the research is not accurately represented in the research record. Examples include improperly manipulating microscopy images or selectively omitting inconsistent experimental results.
- Plagiarism: The appropriation of another person's ideas, processes, results, or words without giving appropriate credit. This encompasses copying another researcher's synthesis procedures, theoretical models, or descriptive text without attribution.
The 2025 ORI Final Rule: Key Updates
On January 1, 2025, the ORI implemented its long-awaited Final Rule revising the Public Health Service (PHS) Policies on Research Misconduct, marking the first major overhaul since 2005 [1]. Key enhancements particularly relevant to materials science include:
- Clarified Terminology: The Final Rule provides clearer legal and operational definitions for terms like "recklessness," "honest error," and notably, "self-plagiarism." While self-plagiarism and authorship disputes are now explicitly excluded from the federal definition of misconduct, they remain subject to institutional policies or publishing standards [1].
- Procedural Efficiency: Institutions can now add new respondents or allegations to an ongoing investigation without restarting the entire process, significantly improving the efficiency of addressing complex cases that may involve multiple researchers or projects [1].
- Modern Research Structures: The rule introduces streamlined procedures for handling data confidentiality, record sequestration, and international collaborations, addressing common challenges in large, multi-institutional materials science research consortia [1].
Table 1: Key Provisions of the 2025 ORI Final Rule with Implications for Materials Science
| Provision | Key Change | Significance for Materials Science |
|---|---|---|
| Definition Clarification | Explicit exclusion of self-plagiarism from federal misconduct definition | Clarifies boundaries for reusing methodological descriptions in multiple papers |
| Investigation Flexibility | Ability to add respondents/allegations without restarting process | Efficient handling of multi-project, multi-researcher misconduct cases |
| International Collaboration | Streamlined procedures for cross-border investigations | Addresses complexities in global materials research partnerships |
| Implementation Timeline | Full compliance required by January 1, 2026 | Allows institutions time to adapt policies and training programs |
Quantitative Landscape of Research Misconduct
Global Disparities in Research Integrity
Recent data reveals significant patterns in research misconduct and integrity training across the global research ecosystem. A 2025 Springer Nature white paper analyzing surveys from seven countries demonstrated substantial variations in research integrity training access, with China (79%) and Japan (73%) reporting the highest access rates, followed by the United States (56%), and Brazil showing the lowest at 27% [3]. Despite these disparities, an overwhelming majority of researchers (84-94%) across all surveyed countries support mandatory research integrity training at some point in their careers [3].
Analysis of exclusion patterns from Clarivate's Highly Cited Researchers list reveals field-specific integrity challenges. In 2024, 2,045 unique individuals were excluded from the list due to behaviors indicative of research misconduct or metric manipulation, a dramatic increase from approximately 300 researchers (4.5% of candidates) excluded in 2021 [4]. Engineering had the highest exclusion rate at 8.9%, highlighting particular challenges in fields adjacent to materials science [4].
Table 2: Research Integrity Training Access and Outcomes by Country (2025)
| Country | Access to Training | Support for Mandatory Training | Retraction Rate Context |
|---|---|---|---|
| China | 79% | 84-94% (range across all countries) | Higher retraction rates despite high training access |
| Japan | 73% | 84-94% | Moderate retraction rates |
| United States | 56% | 84-94% | Moderate retraction rates |
| United Kingdom | 51% | 84-94% | Lower retraction rates despite lower training access |
| Brazil | 27% | 84-94% | Lower retraction rates despite lowest training access |
The persistence of citations to retracted research represents a significant integrity challenge across scientific disciplines, including materials science. Multiple studies confirm that retracted papers continue to be cited extensively after retraction, with most citations failing to acknowledge the retraction status [5]:
- In radiation oncology, 34 retracted papers were cited 576 times after retraction, with 92% of citing studies treating the work as legitimate [5].
- Exercise physiology saw 9 retracted papers cited 469 times after retraction, with no citations in a 20% sample acknowledging the retraction [5].
- COVID-19 literature demonstrated similar patterns, with 212 retracted papers cited approximately 650 times after retraction, and 80% of citations treating the retracted work as valid [5].
These citation patterns highlight the critical need for improved notification systems and researcher awareness regarding retracted literature, particularly in fast-moving fields like materials science where prior work heavily influences subsequent research directions.
Detection Methodologies and Experimental Protocols
Image Manipulation Detection in Materials Characterization
Image manipulation represents a prevalent form of falsification in materials science, particularly involving characterization techniques such as electron microscopy and spectroscopy. The following experimental protocol outlines a standardized approach for detecting image manipulation:
Protocol: Forensic Analysis of Scanning Electron Microscopy (SEM) Images
- Metadata Analysis: Extract and examine EXIF metadata from digital image files, verifying consistency between reported instrument settings and image characteristics [5].
- Error Level Analysis (ELA): Identify regions of inconsistent compression levels that may indicate copy-paste manipulation or alteration.
- Clone Detection Algorithm: Apply pixel-based duplication detection algorithms (e.g., using ImageTwin, Proofig) to identify copied and pasted image elements within or between figures.
- Background Consistency Analysis: Examine background noise patterns across different image regions for inconsistencies suggesting manipulation.
- Instrument Verification: Cross-reference reported magnification scales with known feature sizes and confirm consistency of instrumental signatures.
A 2025 forensic scan of 11,314 materials-science papers containing SEM images found that 2% had mismatched instrument metadata, and these papers were significantly more likely to contain analytic errors, establishing a link between poor reporting and potential fraud [5].
Data Fabrication Detection Through Statistical Forensics
Statistical analysis provides powerful tools for identifying potentially fabricated data in materials science research:
Protocol: Benford's Law Analysis for Experimental Data
- Data Extraction: Compile numerical data from reported measurements (e.g., material properties, synthesis yields, performance metrics).
- First-Digit Distribution: Apply Benford's Law to analyze the frequency distribution of leading digits in reported numerical values.
- Deviation Analysis: Calculate the chi-square statistic to quantify conformity between observed digit frequencies and expected Benford distribution.
- Contextual Interpretation: Consider field-specific contextual factors that may legitimately influence digit distributions before concluding potential fabrication.
This methodological approach is particularly valuable for identifying anomalies in large datasets reporting material properties or performance metrics that may indicate selective reporting or outright fabrication.
Emerging Threats: Paper Mills and AI in Materials Science
The Paper Mill Threat to Materials Science
Paper mills—fraudulent organizations that produce and sell fabricated research papers—represent an increasingly sophisticated threat to research integrity. A 2025 study detailed the scope of just one paper mill, Tanu.pro, which was linked to 1,517 fraudulent papers across 380 journals, involving more than 4,500 scholars from 46 countries [5]. Springer Nature reported receiving 8,432 submissions tied to this single paper mill, with nearly 80 making it into print despite detection efforts [5].
Paper mills targeting materials science research often exhibit specific characteristics:
- Citation Networks: Fabricated author identities cite each other's work, creating closed networks of validation that can artificially inflate perceived impact [5].
- Methodological Templates: Reuse of similar methodological approaches with minor variations across multiple papers.
- Image Recombination: Repurposing of legitimate characterization images with manipulated labels or contexts.
Artificial Intelligence: Dual-Use Potential
AI technologies present both challenges and solutions for research integrity in materials science:
Threats:
- AI-generated text can produce plausible-sounding but scientifically meaningless manuscripts [6].
- AI-powered image generation and manipulation tools can create convincing but fabricated characterization data [7].
- Automated paraphrasing tools can obscure plagiarized content through "tortured phrases"—unusual word substitutions that evade traditional plagiarism detection [7].
Solutions:
- AI-driven screening tools can flag suspicious phrasing patterns indicative of automated paraphrasing [7].
- Network analysis algorithms can identify anomalous citation patterns and authorship networks characteristic of paper mills [6].
- Automated image forensics can detect manipulation patterns across large publication volumes that would be impractical for human reviewers [5].
Table 3: Research Reagent Solutions for Integrity Verification
| Tool/Category | Specific Examples | Function in Integrity Verification |
|---|---|---|
| Image Analysis Tools | ImageTwin, Proofig | Detect image duplication and manipulation in microscopy data |
| Plagiarism Detection | iThenticate, Turnitin | Identify textual plagiarism and inappropriate duplication |
| AI-Anomaly Detection | Problematic Paper Screener, Springer Nature's tortured phrase detector | Flag AI-generated text and manipulated phrasing |
| Data Forensics | STM Integrity Hub, Benford's Law analysis | Identify statistical anomalies in reported data |
| Citation Analysis | Clarivate analytics, Citation network mapping | Detect citation cartels and anomalous citation patterns |
Prevention Frameworks for Materials Science Research
Institutional Responsibility and Culture
Creating a culture of research integrity requires committed engagement from research institutions. The Association for Practical and Professional Ethics (APPE) recommends several evidence-based strategies for institutions [8]:
- Periodic Program Inventory: Conduct regular internal, institution-wide inventories of Responsible Conduct of Research (RCR) programs to assess coverage and effectiveness.
- Adequate Resource Allocation: Assess the cost of effective RCR education and commit appropriate funding and resources to integrity initiatives.
- Tailored Training: Provide and encourage participation in appropriate, engaging RCR training tailored to specific researcher roles and career stages.
- Climate Assessment: Leverage existing tools to conduct periodic assessments of both the research integrity climate on campus and the effectiveness of RCR training programs.
Effective Training Methodologies
The 2025 Springer Nature white paper on research integrity training revealed that few researchers (7-29%) in any surveyed country are required to demonstrate understanding via mandatory testing; assessments often rely instead on simpler measures of self-awareness or participation in training discussions [3]. This highlights a critical gap in training effectiveness that materials science institutions should address through:
- Competency-Based Assessment: Implement mandatory testing with passing thresholds to verify comprehension of key integrity concepts.
- Case-Based Learning: Utilize real-world scenarios relevant to materials science research practices.
- Hybrid Delivery Models: Combine consistent core curriculum delivered online with practical, discipline-specific components delivered in person.
- Career-Stage Appropriateness: Tailor training content to researcher experience levels, from graduate students to principal investigators.
Addressing research misconduct in materials science requires a multi-faceted approach that combines clear definitions, robust detection methodologies, and preventative institutional cultures. The 2025 regulatory updates provide a more flexible framework for addressing misconduct, while technological advances offer both new challenges and powerful detection capabilities. For materials science researchers and drug development professionals, maintaining vigilance against FFP is not merely about compliance, but about preserving the foundational trust that enables scientific progress and the translation of research into practical applications that benefit society. As research practices continue to evolve, particularly with the integration of AI tools, the materials science community must remain proactive in developing and implementing integrity safeguards that match the sophistication of both legitimate research practices and emerging forms of misconduct.
In the field of materials science and engineering, the complex journey from hypothesis to validated knowledge requires a structured framework to ensure both scientific rigor and societal impact. Transitioning to independent research can be a culture shock for students and early-career professionals who may only understand research through the simple framework of the scientific method [9]. A comprehensive research cycle extends far beyond experimentation to include the dissemination, discussion, and further refinement of results, allowing them to become part of the collective body of knowledge [9]. Research integrity—guided by principles of honesty, transparency, and respect for ethical standards—serves as the foundational pillar supporting this entire process, upholding society's trust in science and fostering genuine scientific progress [10] [11]. This whitepaper outlines an explicit model for the materials science research cycle, integrating research integrity as a core component to advance the field's reliability and impact.
The Research+ Cycle: A Structured Framework for Knowledge Creation
To address the challenges of modern materials research, a refined model known as the Research+ cycle has been proposed. This model explicitly outlines the steps researchers can use to advance their field's collective knowledge [9]. It is based on an idealized six-step process but incorporates critical enhancements to reflect the real-world complexities of scientific inquiry.
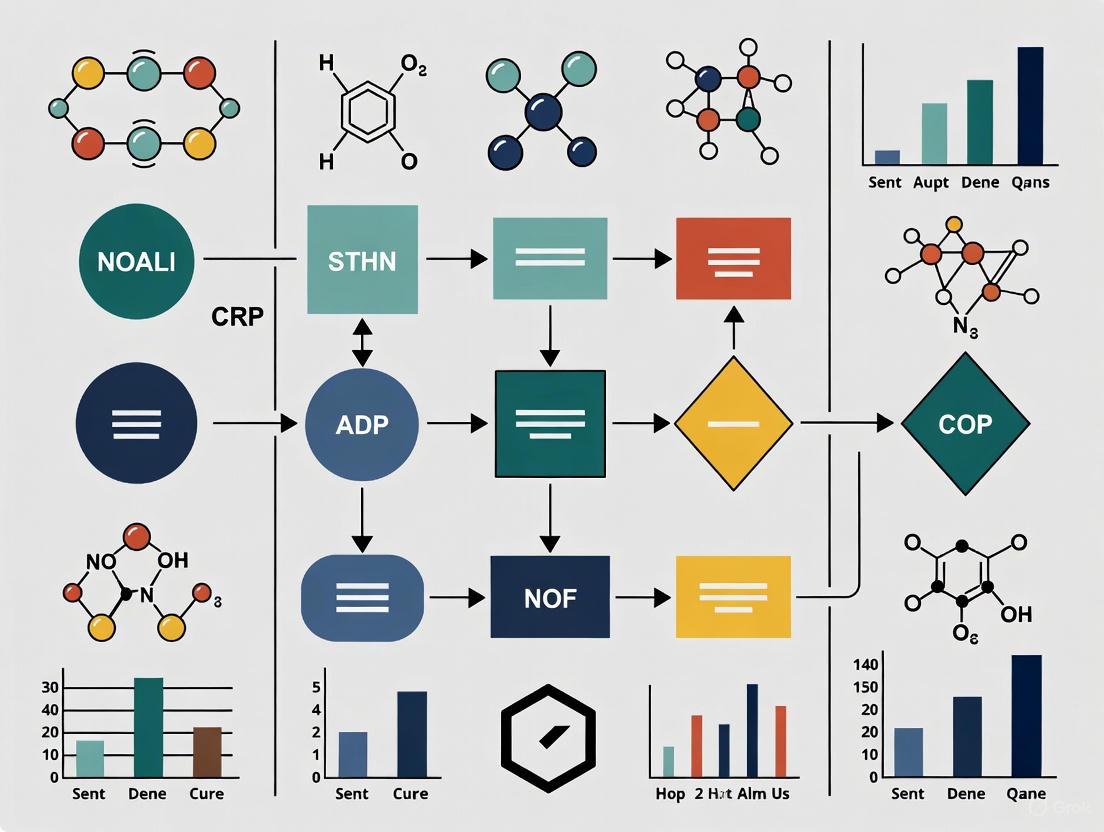
The following diagram illustrates the integrated Research+ Cycle, which places the understanding of the existing knowledge base at its core.
This model enhances the traditional research process with three critical, often overlooked steps [9]:
- Understand the existing body of knowledge: This foundational activity is placed at the center of the methodology, informing all aspects of being a researcher.
- Explicitly state how research questions align with societal goals: Research agendas often shift with societal focus, making this alignment crucial for relevance and funding.
- Refine methodologies and replicate results: Tacit knowledge is often used to iteratively refine methods; making this explicit helps early-career researchers develop critical evaluation skills.
A key strength of this framework is its inclusive definition of a researcher as "one who engages with any part of the research cycle with the intent of developing new structure–properties–performance–processing knowledge," regardless of whether they participate in all aspects [9]. This acknowledges the collaborative and specialized nature of modern materials science.
Quantitative Data Collection and Analysis in Materials Science
Methods for Quantitative Data Collection
Quantitative research in materials science relies on objective measurements and the statistical analysis of numerical data to quantify variables of interest and uncover patterns [12]. The table below summarizes the primary quantitative data collection methods relevant to materials science research.
Table 1: Quantitative Data Collection Methods for Materials Science
| Method | Description | Application in Materials Science |
|---|---|---|
| Online Surveys | Closed-ended questions distributed digitally to gather comparable data from large audiences [13]. | Collecting standardized performance data on new materials from multiple research institutions. |
| Structured Observations | Systematic recording of behaviors or processes using set parameters, focusing on numerical counts and measurements [13]. | Documenting the number of times a material fails under specific stress conditions in a controlled test. |
| Document Review & Secondary Data | Analysis of existing research, public records, company databases, and published literature [13]. | Leveraging existing material property databases to establish baseline performance metrics. |
| Structured Interviews | Verbal administration of surveys with mainly closed-ended questions (yes/no, multiple choice, rating scales) [13]. | Gathering standardized feedback from experts on the practical applicability of a new material synthesis technique. |
Statistical Analysis Techniques
Once collected, quantitative data undergoes statistical analysis to draw meaningful conclusions. The choice of technique depends on the research questions and the nature of the data.
Table 2: Statistical Techniques for Materials Science Data Analysis
| Technique | Purpose | Materials Science Application Example |
|---|---|---|
| Descriptive Statistics | Summarize and describe data features through measures of central tendency and dispersion [12]. | Calculating mean tensile strength, median fatigue cycles, and standard deviation of ceramic hardness measurements. |
| Inferential Statistics | Make predictions about a population based on a sample using hypothesis testing and confidence intervals [12]. | Determining if observed differences in alloy corrosion resistance are statistically significant between treatment groups. |
| Multivariate Analysis | Explore complex relationships between multiple variables simultaneously [12]. | Understanding how processing temperature, pressure, and cooling rate collectively affect polymer crystallinity and strength. |
Integrating Research Integrity Throughout the Research Cycle
Defining Research Integrity and Misconduct
Research integrity refers to a set of moral and ethical standards that serve as the foundation for executing research activities. It incorporates principles of honesty, transparency, and respect for ethical standards and norms throughout all research stages, from design and data collection to analysis, reporting, and publishing [11] [14]. The core of research misconduct is traditionally defined by three primary violations [11] [14]:
- Fabrication: Making up data or results and recording or reporting them.
- Falsification: Manipulating research materials, equipment, processes, or changing/omitting data or results such that the research is not accurately represented.
- Plagiarism: Appropriating another person's ideas, processes, results, or words without giving appropriate credit.
The following diagram illustrates how integrity principles are integrated into each stage of the Research+ Cycle to create a self-correcting, ethical research ecosystem.
Institutional Frameworks Supporting Research Integrity
Multiple stakeholders share responsibility for maintaining research integrity throughout the research cycle [11]:
- Researchers must adhere to the highest ethical standards, self-regulate, and assume responsibility for promoting scientific knowledge with integrity.
- Research Supervisors and Mentors should arrange comprehensive discussions about scientific misconduct and guide students through challenges, serving as role models and treating errors as teaching opportunities [11].
- Research Institutions play a crucial role in establishing an atmosphere that supports integrity ideals, providing guidance, instruction, and assistance to researchers. This includes establishing RI departments, creating mechanisms for preventing misconduct, and protecting whistleblowers [11].
- Journals and Editors act as protectors of quality and ethical standards in the dissemination of research results through enhanced peer review processes [11].
Experimental Protocols and Methodologies in Materials Science
Quantitative Research Workflow
The following diagram outlines a generalized experimental workflow for quantitative research in materials science, highlighting key stages from hypothesis development through data analysis and validation.
Essential Research Reagents and Materials
Table 3: Essential Research Reagent Solutions for Materials Science Experimentation
| Item | Function in Research | Application Example |
|---|---|---|
| Validated Measurement Tools | Instruments with proven reliability and accuracy for quantifying material properties. | Nanoindenters for hardness testing, spectrophotometers for optical properties, SEM for microstructural analysis. |
| Standard Reference Materials | Certified materials with known properties used for instrument calibration and method validation. | NIST standard reference materials for calibrating thermal analysis equipment. |
| Data Collection Instruments | Structured tools for gathering quantitative data according to research design. | Standardized survey instruments for collecting lab performance data across multiple research sites. |
| Statistical Analysis Software | Tools for performing descriptive, inferential, and multivariate analysis on research data. | Software like R, Python with scientific libraries, or specialized packages for analyzing structure-property relationships. |
| Laboratory Notebooks | Detailed, chronological records of experimental procedures, observations, and results. | Maintaining rigorous documentation for replication studies and intellectual property protection. |
Effective Data Visualization and Communication
Principles for Tables and Figures
Effective communication of research findings requires careful consideration of data presentation. Tables and figures should be used to present complicated information in ways that are accessible and understandable to the reader [15].
Table 4: Guidelines for Effective Data Presentation in Materials Science
| Element | Tables | Figures |
|---|---|---|
| Primary Purpose | Present lists of numbers or text in columns; synthesize literature; explain variables; present raw data [15]. | Visual presentations of results; show trends and patterns; communicate processes; display complicated data simply [15]. |
| Key Considerations | Organize so like elements read down, not across; ensure decimal points align; use clear column titles with units [15]. | Choose the simplest effective visualization; ensure sufficient size and resolution; consider color blindness [15] [16]. |
| Title/Caption Placement | Above table, left-justified [15]. | Below figure, left-justified [15]. |
| Accessibility Requirements | Use clear demarcation between parts; avoid gridlines in printed versions [15]. | Maintain minimum color contrast ratio of 3:1 for graphical objects and 4.5:1 for text [17] [16]. |
Color Contrast Requirements for Accessibility
When creating figures for publication, adherence to Web Content Accessibility Guidelines (WCAG) ensures that visual materials are accessible to all readers, including those with visual impairments [17] [16]:
- Normal text should have a contrast ratio of at least 4.5:1 (AA rating) or 7:1 (AAA rating)
- Large-scale text (120-150% larger than body text) should have a contrast ratio of at least 3:1 (AA) or 4.5:1 (AAA)
- Graphical objects and user interface components (such as graphs and icons) require a contrast ratio of at least 3:1 (AA)
These guidelines help ensure that research findings are communicated effectively to the broadest possible audience, a key component of research integrity and transparency.
The Materials Science Research Cycle, particularly the Research+ model, provides a comprehensive framework for robust knowledge creation when integrated with strong research integrity principles. This structured approach—encompassing understanding existing knowledge, identifying gaps, constructing hypotheses, designing methodologies, applying methods, evaluating results, and communicating findings—creates a self-correcting system that advances reliable scientific knowledge. By embedding integrity throughout this cycle and employing rigorous quantitative methods and transparent communication, materials science researchers can enhance the reliability and impact of their work, ultimately contributing to scientific progress that earns and maintains public trust. The collective responsibility of researchers, mentors, institutions, and publishers in upholding these standards ensures that the materials science field continues to develop knowledge that is both scientifically sound and socially beneficial.
The reliability of scientific research, particularly in fields with direct human impact like materials science and drug development, is the cornerstone of progress. However, the ecosystem is increasingly threatened by research misconduct, which encompasses fabrication, falsification, and plagiarism [18]. A 2025 analysis of the integrity landscape reveals that industrial-scale fraud operations, known as "paper mills," now pose a significant threat, having produced over 1,500 fraudulent papers across hundreds of journals [5]. This whitepaper delineates the severe, multi-faceted consequences of misconduct—from staggering financial costs to irreparable reputational harm—and frames them within a broader thesis on building a more resilient and ethical research culture in materials science. The stakes extend beyond individual careers to the very credibility of the scientific enterprise and the safety of the public that relies on its findings.
Quantifying the Impact: Financial and Career Consequences
The consequences of research misconduct are not merely theoretical; they can be measured in millions of wasted dollars and truncated careers. Understanding this quantitative impact is crucial for appreciating the full scope of the problem.
Direct Financial Costs
Public funds allocated for research are significantly squandered when misconduct leads to retraction. An analysis of papers retracted due to misconduct between 1992 and 2012 found they accounted for approximately $58 million in direct funding from the National Institutes of Health (NIH) [19] [18]. The financial burden per retracted paper is substantial, with a mean attributable cost of $392,582 and a median of $239,381 [19]. Furthermore, an estimate of the total funding for all NIH grants that contributed in any way to retracted papers reached nearly $2.3 billion when adjusted for inflation [19]. These figures represent pure waste—resources that could have supported valid, transformative research.
Table 1: Financial Costs of Research Misconduct (NIH, 1992-2012)
| Metric | Value | Details |
|---|---|---|
| Total Direct NIH Funding for Retracted Articles | $58 million | Accounts for articles retracted due to misconduct [19] [18] |
| Mean Attributable Cost per Article | $392,582 | Standard Deviation: $423,256 [19] |
| Median Attributable Cost per Article | $239,381 | More representative of a "typical" case due to skewed distribution [19] |
| Total Grant Funding for Grants Citing Retracted Papers | $2.32 billion | Value in 2012 dollars, accounting for inflation [19] |
Consequences for Research Careers
A finding of misconduct profoundly impacts the productivity and funding of the researchers involved. Analysis of senior authors named in Office of Research Integrity (ORI) findings shows a median 91.8% decrease in publication output after censure [19]. A stark 55% of these authors ceased publishing entirely in the three years following the ORI report [19]. This decline is also reflected in research funding, as censure often includes debarment from contracts with public health services for a period of time [19]. This data indicates that misconduct is typically, though not always, a career-ending event.
Table 2: Impact of Misconduct Finding on Researcher Productivity (ORI Data)
| Analysis Period | Pre-Misconduct Finding Publications | Post-Misconduct Finding Publications | Percentage Change |
|---|---|---|---|
| 3-Year Interval | 256 (Median 1.0/year) | 78 (Median 0/year) | -69.5% [19] |
| 6-Year Interval | 552 (Median 1.2/year) | 140 (Median 0/year) | -74.6% [19] |
| Career-Long Analysis | Median 2.9/year | Median 0.25/year | Median -91.8% [19] |
Detection and Analysis: Methodologies for Upholding Integrity
Combating research fraud requires sophisticated detection protocols. The following methodologies, drawn from current publisher practices, form a frontline defense.
Integrity Screening and Image Forensics
Protocol 1: Scalable Integrity Screening (e.g., PLOS) This multi-layered approach is designed to filter submissions at scale before peer review [5].
- Cross-Publisher Duplicate Submission Check: Utilize the STM Integrity Hub to detect manuscripts submitted simultaneously to multiple publishers.
- Automated Digital Forensics: Employ specialized software to conduct:
- Plagiarism Analysis: Identify textual duplication.
- Image Analysis: Flag potential manipulation in gels, blots, and micrographs (e.g., copy-paste duplication, spliced lanes). A 2025 forensic scan of over 11,000 materials-science papers with SEM images used metadata mismatches to identify papers with a higher likelihood of analytic errors [5].
- Contributor Behavior Audit: Scrutinize requests to add multiple authors post-submission, a known red flag.
- Targeted Screening: Apply pre-review checks to study types prone to misuse, such as systematic reviews and Mendelian randomization studies.
- Outcome: Implementation of this protocol raised desk rejection rates from 13% to 40%, conserving valuable peer-review resources [5].
Protocol 2: Network Analysis for Industrial-Scale Fraud This method identifies coordinated misconduct by mapping digital fingerprints across the literature [6].
- Data Collection: Aggregate data on authors, affiliations, citations, and methodological patterns from thousands of papers.
- Cluster Identification: Use AI and data analytics to map connections and identify closed citation networks, suspicious author clusters, and recurrent methodological templates.
- Pattern Recognition: Identify signals such as "tortured phrases" (awkward, synonym-substituted language to avoid plagiarism detectors) and abnormal citation concentrations around a specific author or journal cluster [5].
- Human Oversight: Expert investigators interpret the flagged patterns to confirm fraud, as AI excels at flagging anomalies but human judgment is required for final determination [5] [6].
Workflow Visualization: Research Integrity Pipeline
The following diagram illustrates the multi-stage defense system for maintaining research integrity, from submission to post-publication, integrating both technological tools and human judgment.
Diagram 1: Research integrity defense workflow.
Research Reagent Solutions for Integrity
Beyond detection, maintaining integrity involves using specific tools and frameworks to ensure transparency and accountability.
Table 3: Essential Tools and Frameworks for Research Integrity
| Tool/Framework | Primary Function | Application in Materials Science |
|---|---|---|
| ORCID ID | Provides a unique, persistent digital identifier for researchers. | Disambiguates author identity, ensures proper attribution of work, and links researchers to their affiliations and publications [20]. |
| CRediT (Contributor Roles Taxonomy) | Standardized taxonomy to clarify the specific contributions of each author. | Eliminates ghost authorship and clarifies roles in complex, multi-disciplinary materials science projects [5]. |
| STM Integrity Hub | A cross-publisher collaboration platform. | Allows journals to detect duplicate submissions across a wide portfolio of publications, a common tactic of paper mills [5]. |
| Image Forensics Software | Automated tools to detect image manipulation. | Scans SEM images, XRD patterns, and other graphical data for duplication, splicing, or inappropriate manipulation [5]. |
| DataSeer & Open Science Platforms | Tools to promote and monitor data sharing. | Encourages deposition of raw data and code for materials characterization and modeling, enabling reproducibility and validation [6]. |
Systemic Consequences and the Path to Improvement
The ripple effects of misconduct extend far beyond the immediate parties involved, damaging the entire scientific ecosystem and public trust.
Erosion of Trust and Persistence of Invalidated Work
Fraud in research undermines the public's trust in science and can lead to real-world harms, such as the release of ineffective drugs or unsafe medical devices [18]. A persistent problem is that even when fraud is uncovered, the scientific record is not always corrected. Fewer than 25% of known paper-mill articles are formally retracted [5]. Consequently, retracted papers continue to be cited as valid evidence. Studies across multiple disciplines (e.g., radiation oncology, dentistry, COVID-19 literature) show that a vast majority of post-retraction citations—often 80-90%—fail to acknowledge the retraction, meaning flawed or fraudulent data continues to pollute the literature and mislead future research [5].
Strategies for a Resilient Research Integrity Framework
Building a more robust system requires coordinated action from all stakeholders in the research enterprise. The following strategies, drawn from recent national dialogues and policy reports, provide a roadmap for improvement [21] [8].
Harmonize and Tier Federal Regulations: Inconsistencies across agencies create confusion and administrative burden. A 2025 National Academies report recommends creating a centralized role in the White House Office of Management and Budget to coordinate requirements and adopting a risk-based approach where oversight is "tiered to the nature, likelihood, and potential consequences of risks" [21]. For materials science, this could mean streamlining oversight for low-risk computational studies while maintaining rigorous oversight for research involving hazardous materials.
Foster Institutional Accountability and Culture: Research institutions must move beyond compliance-based training. The Association for Practical and Professional Ethics (APPE) recommends that institutions conduct periodic internal inventories of their Responsible Conduct of Research (RCR) programs, assess their cost-effectiveness, and leverage tools to evaluate the research integrity climate on campus [8]. Leadership must demonstrate an unwavering commitment to ethics.
Implement a Single Federal Misconduct Policy: Differing standards for research misconduct proceedings across agencies lead to confusion. A key policy option is to establish a single, flexible federal misconduct policy that all agencies adhere to, ensuring clarity in definitions and investigative processes [21].
Accelerate the Adoption of Open Science Practices: Transparency is a powerful antidote to fraud. When researchers openly share data, code, and methodologies, it becomes substantially more difficult to sustain deception [6]. Funders and institutions should create stronger incentives for data sharing and provide the tools to make sharing frictionless.
Reimagine Research Assessment: The current emphasis on publication quantity and journal impact factor perversely incentivizes misconduct. The research community must shift toward multifaceted metrics that consider transparency, reproducibility, and meaningful contribution over mere output [6]. This reduces the pressure to "publish or perish" that drives unethical behavior.
The stakes of research misconduct are unacceptably high, encompassing the massive waste of public funds, devastation of individual careers, erosion of public trust, and persistent contamination of the scientific record. For the fields of materials science and drug development, where progress directly impacts human health and safety, the cost of inaction is intolerable. Addressing this crisis requires a concerted shift from reactive detection to proactive prevention. By implementing harmonized policies, fostering accountable institutional cultures, mandating transparency, and re-evaluating the incentives that drive research, the scientific community can fortify its integrity. The path forward demands collaboration across disciplines, open dialogue between stakeholders, and a collective commitment to an ecosystem where reliability is demonstrated, quality is paramount, and ethical progress is the ultimate measure of success.
In the evolving landscape of academic publishing, retractions serve as a critical mechanism for maintaining the integrity of the scientific record. The year 2025 has provided significant case studies that highlight both persistent challenges and emerging trends in research integrity, particularly relevant for researchers in materials science and drug development. Analysis of the most highly cited retracted papers reveals a troubling pattern: many continue to accumulate citations years after their retraction, perpetuating the dissemination of unreliable science [22]. This comprehensive review examines these recent cases to extract actionable lessons for improving research practices, data integrity, and institutional responses within the materials science community.
Recent data from Retraction Watch reveals several highly cited papers retracted in 2024-2025, demonstrating the significant impact these publications continue to have despite their retracted status [22]. The scale of the problem is substantial; while retractions were once rare (1 in 5,000 papers in 2002), they have increased dramatically to approximately 1 in 500 papers by 2023 [23].
Table 1: Most Highly Cited Retracted Papers (2024-2025)
| Article Title | Journal | Year of Retraction | Citing Articles Before Retraction | Citing Articles After Retraction | Total Cites |
|---|---|---|---|---|---|
| Pluripotency of mesenchymal stem cells derived from adult | Nature | 2024 | 4,491 | 29 | 4,520 |
| Hydroxychloroquine and azithromycin as a treatment of COVID-19 | International Journal of Antimicrobial Agents | 2024 | 3,171 | 27 | 3,198 |
| A specific amyloid-β protein assembly in the brain impairs memory | Nature | 2024 | 2,359 | 31 | 2,390 |
| Predictive Validity of a Medication Adherence Measure | The Journal of Clinical Hypertension | 2023 | 1,931 | 271 | 2,202 |
| MicroRNA signatures of tumor-derived exosomes as diagnostic biomarkers | Gynecologic Oncology | 2023 | 1,868 | 79 | 1,947 |
The concerning trend of post-retraction citation is particularly evident in cases like the 2005 Science paper on visfatin, which received 1,340 citations after its 2007 retraction [22]. This persistent citation of retracted literature represents a significant contamination of the scientific ecosystem that researchers must actively guard against.
Analysis of Notable 2025 Retraction Cases
The "Arsenic Life" Controversy: A 15-Year Journey to Retraction
After nearly 15 years of controversy, Science formally retracted the influential "arsenic life" paper in 2025 [24]. The original 2010 publication claimed the discovery of a microbe, GFAJ-1, capable of using arsenic instead of phosphorus in its biochemical processes—a finding with potential implications for understanding life on Earth and beyond.
Experimental Methodology and Flaws: The researchers employed extreme environment sampling from Mono Lake, California, culturing the bacterium GFAJ-1 in increasingly phosphorus-depleted conditions with high arsenic concentrations. They reported incorporation of arsenic into DNA backbones using:
- Radioactive arsenic-74 tracing experiments
- Mass spectrometry analysis of extracted biomolecules
- Elemental composition analysis of nucleic acids
- Growth measurements under arsenic stress
The fundamental methodological flaw was the inability to completely eliminate trace phosphorus from growth media, creating ambiguity about whether observed growth resulted from arsenic incorporation or phosphorus scavenging. Independent replication attempts in 2012 by two separate research teams failed to reproduce the key findings when using more rigorous purification protocols [24].
Retraction Compromise: The 2025 retraction occurred without a finding of misconduct, with the journal citing experimental error as the reason. The retraction notice states that the "reported experiments do not support its key conclusions" [24]. Notably, the authors maintained their dissent in an accompanying letter, stating: "While our work could have been written and discussed more carefully, we stand by the data as reported" [24]. This case represents a compromise approach to retraction where fundamental methodological limitations undermine confidence in conclusions without evidence of deliberate misconduct.
Stem Cell Pluripotency and Image Manipulation Concerns
The most highly cited retracted paper of 2024, "Pluripotency of mesenchymal stem cells derived from adult" published in Nature, accumulated 4,520 citations despite its retraction [22]. While specific reasons for retraction aren't detailed in the available sources, this case aligns with a broader pattern of image manipulation concerns in high-impact biology and materials science research.
Methodological Considerations for Materials Science: The experimental protocols typically involved in such stem cell research include:
- Isolation and culture of mesenchymal stem cells (MSCs) from adult tissues
- Differentiation assays into multiple cell lineages (osteogenic, adipogenic, chondrogenic)
- Flow cytometry for surface marker characterization
- Gene expression analysis using RT-PCR and RNA sequencing
- Teratoma formation assays in immunodeficient mice
- Immunofluorescence and histochemical staining
The high citation rate post-retraction (29 citations) highlights the ongoing challenge of ensuring the scientific community acknowledges and respects retraction status, particularly for influential papers [22].
The Growing Retraction Crisis: Systemic Challenges
Paper Mills and AI-Enabled Fraud
The retraction landscape is increasingly complicated by sophisticated "paper mills" – for-profit organizations that systematically falsify the scientific record [23]. These operations have evolved into sophisticated businesses producing papers complete with fabricated data, charts, and manipulated images, often making them difficult to distinguish from legitimate research.
Paper Mill Operations: Paper mills typically offer:
- Complete fabricated manuscripts on demand
- Authorship slots on seemingly legitimate papers
- Falsified experimental data and images
- Fabricated peer review reports through suggested reviewer networks
- Guaranteed publication in indexed journals [23]
The emergence of AI tools has further exacerbated this problem by enabling more sophisticated fabrication while simultaneously providing journals with better detection capabilities, creating an "arms race" in research fraud [23].
Impact on Research Careers and Collaboration Networks
Recent research published in Nature Human Behaviour demonstrates that retractions have profound effects on scientific careers, particularly for early-career researchers [25]. The study analyzed over 4,578 retracted papers involving 14,579 authors, revealing that retracted authors often leave scientific publishing, especially when retractions attract significant attention.
Collaboration Network Analysis: The research found that retracted authors who remain active in science maintain and establish more collaborations compared with similar non-retracted counterparts. However, these networks are qualitatively different – retracted authors generally retain less senior and less productive co-authors, though they gain more impactful co-authors post-retraction [25]. This suggests a complex restructuring of professional relationships following retractions.
Research Integrity Framework and Practical Solutions
The Research Integrity Process
The pathway from publication to retraction involves multiple stakeholders and decision points, as illustrated below:
Table 2: Research Integrity Resources for Materials Scientists
| Tool/Resource | Type | Primary Function | Access |
|---|---|---|---|
| Retraction Watch Database | Database | Tracking retracted papers and reasons | Public |
| INSPECT-SR (Available 2025) | Checklist | Identifying problematic randomized trials | Public |
| Problematic Paper Screener | AI Tool | Detecting paper mill products | Journal use |
| Papermill Alarm | AI Tool | Identifying manipulated images/text | Journal use |
| LibKey Nomad | Browser Extension | Retraction alerts during research | Public |
| Edifix | Citation Tool | Identifying retracted references | Subscription |
| Zotero with Retraction Watch | Reference Manager | Flagging retracted papers | Public |
| Committee on Publication Ethics (COPE) | Guidelines | Retraction and ethics standards | Public |
Experimental Protocol Verification Framework
For materials scientists seeking to ensure the integrity of their experimental approaches, the following verification framework provides essential safeguards:
Materials Characterization Protocol:
- Independent Replication Planning: Design experiments with built-in checkpoints for key findings using different instrumentation or methodologies.
- Raw Data Preservation: Maintain complete, unprocessed instrument outputs (XRD patterns, SEM/TEM micrographs, spectroscopic data) with metadata.
- Control Experiment Validation: Include positive and negative controls that can detect reagent contamination or methodological flaws (e.g., trace element contamination).
- Image Integrity Documentation: Maintain original, uncropped microscopy images with consistent processing parameters across compared samples.
- Data Transparency: Share complete datasets through repositories to enable independent verification of analyses.
Recommendations for Strengthening Research Integrity in Materials Science
Institutional and Cultural Reforms
The "publish or perish" research culture remains a significant driver of research misconduct, placing unsustainable pressure on researchers [23] [26]. Addressing this requires systemic changes:
- Revised Incentive Structures: Academic institutions should prioritize research quality over quantity in promotion and tenure decisions, valuing reproducible methodologies and data transparency alongside publication metrics.
- Enhanced Research Integrity Training: Implement evidence-based training programs at multiple career stages, from undergraduate students to senior investigators [27]. The INTEGRITY Project provides scaffolded learning materials tailored to different experience levels.
- Protected Whistleblower Mechanisms: Establish clear, confidential channels for reporting concerns without fear of reprisal, particularly for early-career researchers.
- Dedicated Research Integrity Officers: Empower institutional officials with authority and resources to conduct thorough investigations.
Practical Strategies for Individual Researchers
- Pre-Publication Verification: Utilize tools like the INSPECT-SR checklist (available 2025) to identify potential issues before manuscript submission [23].
- Citation Vigilance: Implement reference manager tools with retraction alerts (Zotero with Retraction Watch integration, LibKey Nomad) to avoid citing retracted literature [23].
- Data Sharing Practices: Embrace open science frameworks by sharing raw data and analytical code through trusted repositories to enable verification.
- Image Management: Maintain original, unprocessed images with detailed metadata and processing documentation for all publications.
- Collaboration Transparency: Clearly define roles, responsibilities, and authorship criteria at project inception using established guidelines like CRediT.
The high-profile retractions of 2025 underscore both the vulnerabilities and resilience of the scientific enterprise. As materials science continues to advance with increasing complexity and interdisciplinary connections, maintaining research integrity requires proactive, multi-level approaches. By learning from these cases, implementing robust verification protocols, and fostering a culture that prioritizes transparency over mere publication metrics, the materials science community can strengthen the foundation upon which scientific progress depends. The tools and frameworks outlined here provide a practical starting point for researchers committed to these principles.
Practical Tools and Techniques for Ensuring Data Integrity
The integrity of scientific imagery forms a cornerstone of credible research, particularly in fields like materials science and drug development where visual data often constitutes primary evidence. The advent of sophisticated digital editing tools and generative artificial intelligence (AI) has introduced profound challenges to upholding this integrity. Studies indicate that approximately one in three life sciences manuscripts submitted for publication are flagged for image-related issues, which are frequently unintentional yet difficult to detect with the naked eye [28] [29]. These issues can lead to misinterpretation of data, flawed conclusions, and a erosion of trust in scientific findings. In response, the research community is increasingly turning to automated tools designed to safeguard image authenticity. This whitepaper provides an in-depth examination of Proofig AI, an AI-powered platform developed to address image duplication, manipulation, and plagiarism in scientific publications. Framed within a broader thesis on enhancing research integrity, this analysis details Proofig's technical capabilities, operational workflow, and specific value for researchers committed to ensuring the highest standards of data veracity.
Understanding Image Integrity Challenges
Image integrity in scientific research is threatened by a spectrum of issues, ranging from unintentional oversights to deliberate misconduct. The risks are particularly acute in data-intensive fields like materials science, where image-based evidence is paramount for validating experimental results, such as characterizing nanomaterial structures or documenting cell-drug interactions.
Common types of image integrity breaches include [30]:
- Image Duplication: Reusing the same image, or parts of it, to represent different experimental conditions or results.
- Image Manipulation: Altering an image through cloning, editing, deletion, or splicing to misrepresent the original data.
- Image Fabrication: Creating entirely non-existent images or data.
- Image Plagiarism: Using another researcher's images without proper permission or citation.
- AI-Generated Images: Substituting synthetic images created by AI models for genuine experimental data.
The consequences of these breaches are severe. A post-publication retraction due to image issues is estimated to cost over $1 million per article when accounting for investigations and associated legal costs [31]. Beyond financial damage, such events inflict lasting reputational harm on researchers and their institutions, potentially jeopardizing future funding and career advancement [28]. Furthermore, they undermine the collective trust in scientific literature and can mislead other researchers, who may waste valuable resources attempting to build upon invalidated findings [30].
Proofig AI: Core Capabilities and Technological Framework
Proofig AI is an AI-powered Software-as-a-Service (SaaS) platform designed to automate the detection of image integrity issues in scientific manuscripts. Its technology is built upon a foundation of advanced machine learning, pattern recognition, and statistical analysis [30] [32]. The system is trained on a vast, ethically sourced dataset comprising material developed in-house and open-source content designated for commercial use, ensuring it does not leverage user-uploaded data for model training [31] [28].
The platform's core detection capabilities are comprehensive, addressing both traditional and emerging threats to image integrity:
Comprehensive Image Integrity Detection
Table 1: Overview of Proofig AI's Primary Detection Capabilities
| Detection Type | Key Functionality | Supported Image Variants |
|---|---|---|
| Duplication & Reuse within a Manuscript | Identifies duplicate sub-images, even when scaled, rotated, flipped, or partially overlapped [31] [28]. | Microscopy, Western blots, FACS, histology slides, cell culture, in-vivo/in-vitro images [31] [33]. |
| Alteration or Manipulation | Detects cloning, editing, deletion, and splicing within a single sub-image [31] [28]. | Western blot bands, gel electrophoresis, microscopies [31] [34]. |
| Plagiarism from Published Works | Cross-references tens of millions of images in the PubMed Source database to identify reused sub-images [31] [28]. | All supported image types. |
| AI-Generated Image Detection | Identifies synthetic images created by the most widely used AI models [31] [34]. | Microscopy, Western blots & gels, histology, cell plates, animal imaging, medical scans [34]. |
| Self-Plagiarism | Compares images against a personalized repository of a researcher's prior work to prevent reuse of their own published images [31] [29]. | All supported image types. |
Performance and Accuracy Metrics
Proofig AI demonstrates high accuracy in its detection tasks. The platform reports a 99.4% success rate in core processing of sub-images and a 96.8% precision in text detection [31]. Its performance in detecting AI-generated images is particularly notable, as shown in the table below.
Table 2: Proofig AI's AI-Generated Image Detection Accuracy
| Image Category | True Positive Rate | False Positive Rate | Validation Basis |
|---|---|---|---|
| Multi-Modal Imaging (Microscopy, Histology, etc.) | 95.41% [34] | 0.0093% [34] | Proprietary benchmark testing [34]. |
| Western Blots | 97.68% [34] | 0.002% [34] | Proprietary curated test dataset [34]. |
| Real-World Validation | Data Not Specified | 0.01% [34] | 250,000+ published research images [34]. |
Workflow and Experimental Protocols
Integrating Proofig AI into a researcher's pre-submission process is a streamlined, four-step operation that ensures thorough image checking without significant time investment [28] [29]. The entire workflow is designed for confidentiality, with all analyses conducted on private, secure servers [31].
Step-by-Step Operational Protocol
- Manuscript Upload: The researcher begins by uploading the complete manuscript in PDF format to the Proofig platform. The system then automatically extracts all images and sub-images contained within the document for analysis [28] [29].
- Automated Image Analysis: Proofig AI initiates a multi-faceted analysis of the extracted images. This process involves several concurrent methodologies [30] [28]:
- Pattern Recognition and Comparison: The core of the duplication detection. The system creates digital fingerprints of each sub-image and compares them against each other within the manuscript. Its algorithms are robust against transformations like rotation, scaling, and flipping [31] [30].
- Forensic Analysis for Manipulation: To detect alterations within a single sub-image (e.g., in a Western blot), the software uses statistical analysis to identify inconsistencies in noise patterns, compression artifacts, and cloning traces that are invisible to the human eye [31] [32].
- AI-Generated Image Detection: This feature leverages machine learning models specifically trained on a vast dataset of known AI-generated scientific images. It identifies subtle, synthetic patterns and anomalies that are characteristic of the most widely used generative AI models [34] [32].
- Plagiarism Check: The system cross-references all extracted images against a database of tens of millions of images from published articles in PubMed, calculating similarity scores to flag potential reuse from existing literature [31] [28].
- Validation and Review of Results: The system generates a report highlighting all suspected integrity issues, each with a similarity score and details of any transformations detected. A crucial step involves human oversight: the researcher or an integrity officer manually reviews each flagged match using Proofig's advanced investigation tools (e.g., filters, image alteration tools) to confirm whether the finding represents a genuine issue [30] [28]. This human-in-the-loop protocol ensures that the final judgment is informed by scientific context.
- Report Generation: After validation, the user selects the confirmed findings, and Proofig AI compiles them into a comprehensive PDF report. This report includes both a page view for context and a detailed view of each specific image issue, providing clear documentation for the researcher's records or for communication with journals [30] [28].
The Scientist's Toolkit: Key Reagents and Materials for Image Integrity
Upholding image integrity is not solely a computational task; it requires a combination of digital tools and rigorous laboratory practices. The following table outlines essential "research reagents" and protocols for maintaining image integrity from data acquisition to publication.
Table 3: Essential Materials and Protocols for Upholding Image Integrity
| Item / Protocol | Function / Purpose in Image Integrity |
|---|---|
| Original, Unprocessed Image Files | Serve as the definitive raw data for verification. Must be retained with all metadata to prove authenticity and provide a baseline for any allowable adjustments [30]. |
| Electronic Lab Notebook (ELN) | Provides a secure, timestamped record of experimental procedures, instrument settings, and the direct linkage between raw image data and specific experiments, ensuring replicability [35]. |
| Journal Guidelines on AI Use | A critical reference document. Researchers must strictly adhere to publisher policies regarding the use of AI-generated images, which often prohibit their use for representing research results [30]. |
| Pre-Submission Image Check Protocol | The standardized operating procedure for using a tool like Proofig AI to scan all figures in a manuscript prior to submission, catching unintentional errors early [28] [36]. |
| Metadata-Rich Image Formats | File formats (e.g., TIFF with metadata) that preserve information about acquisition date, time, and instrument parameters, facilitating traceability and auditability [30]. |
Application in Materials Science and Research Integrity
For the materials science and drug development communities, Proofig AI offers targeted capabilities that align with the field's specific integrity needs. The platform's proficiency in analyzing microscopy images (including confocal, light, and electron) and material characterization data is directly applicable to common workflows in nanomaterials research, metallurgy, and polymer science [31] [33]. The ability to detect duplicated or manipulated microstructural images, for instance, prevents the publication of non-representative data that could mislead the entire community about a material's properties.
Furthermore, the emerging threat of AI-generated microscopy images is a significant concern. A recent article in Nature Nanotechnology highlighted that generative AI can now create nanomaterial images virtually indistinguishable from real ones, raising the risk of sophisticated fabrication [35]. Proofig's dedicated detection module for such synthetic images provides a critical defense, allowing journals and institutions to maintain trust in published data.
Adopting Proofig AI proactively aligns with the broader thesis of improving research integrity. Institutions like The Ohio State University and Stanford University now provide campus-wide access to Proofig, framing it as a resource to support researchers in producing ethical, publication-ready work and to avoid costly post-publication investigations [37] [36]. By integrating such tools into the pre-submission workflow, the materials science community can collectively enhance the credibility, reproducibility, and overall trustworthiness of its scientific output.
For researchers in materials science and drug development, maintaining research integrity is paramount to ensuring the credibility and reproducibility of scientific advancements. Proactive manuscript screening represents a critical step in this process, allowing scientists to identify and address potential integrity concerns before submission to journals. This practice is increasingly vital as publishers employ sophisticated tools to check all incoming manuscripts, and issues discovered post-submission can lead to delays, corrections, or even retractions that damage professional reputations [38].
The scholarly publishing landscape has witnessed growing vigilance concerning research integrity, with journals across disciplines implementing more rigorous checks. A startling statistic indicates that up to one-sixth of manuscripts submitted to journals might be affected by plagiarism, representing a significant waste of peer reviewer resources and potential intellectual property loss [39]. For materials scientists developing novel compounds, characterization methods, or therapeutic agents, ensuring the originality and proper documentation of their work is particularly crucial given the competitive nature and high stakes of the field.
This guide provides comprehensive methodologies for implementing proactive screening protocols within research workflows, detailing specific tools and approaches that can help identify potential issues early in the manuscript preparation process. By adopting these practices, researchers can better uphold the highest standards of academic integrity while streamlining their path to publication.
Essential Screening Tools and Their Functions
| Tool Name | Primary Function | Key Features | Applicability to Materials Science |
|---|---|---|---|
| Proofig [38] | Image duplication and manipulation detection | AI-powered analysis of various image types; handles microscopy, Western blots, in-vivo and in-vitro images | Essential for characterizing material structures, drug formulations, and experimental results |
| iThenticate [38] [39] | Plagiarism and AI detection | Compares manuscripts against academic literature database; generates similarity reports | Critical for literature reviews, methodology descriptions, and ensuring original content |
| Crossref Similarity Check [39] | Plagiarism detection | Powered by iThenticate; specifically designed for scholarly publishing | Useful for verifying originality of experimental procedures and results discussions |
Quantitative Comparison of Screening Tools
| Tool | Detection Capabilities | Output Metrics | Limitations & Considerations |
|---|---|---|---|
| Proofig [38] | • Image duplication• Image manipulation• Various scientific image types | • Visual report of detected issues• Location of potential problems | • Requires clear image quality• May flag acceptable image adjustments |
| iThenticate/Similarity Check [39] | • Text similarity• Potential plagiarism• AI-generated content | • Overall Similarity Score (percentage)• Source-by-source breakdown | • High scores don't automatically indicate plagiarism• Requires contextual interpretation by subject experts |
Implementation Protocols for Proactive Screening
Comprehensive Screening Workflow
Pre-Submission Screening Workflow
Protocol 1: Image Integrity Screening with Proofig
Purpose: To detect unintentional image duplications or manipulations in materials science microscopy, characterization data, and experimental results.
Materials and Equipment:
- Proofig software access (via institutional subscription) [38]
- Complete manuscript draft with all figures
- Original image files from experiments
Procedure:
- Prepare Image Files: Compile all figures included in the manuscript in their intended publication format, ensuring resolution meets journal requirements.
- Configure Analysis Settings:
- Select appropriate image categories (e.g., electron microscopy, spectroscopy, chromatography)
- Enable cross-figure comparison to detect duplication across different figure panels
- Run Analysis: Upload the complete manuscript PDF or image set to Proofig for AI-powered analysis.
- Interpret Results:
- Review flagged areas for potential duplication or manipulation
- Assess whether flagged issues represent:
- Honest errors (e.g., accidental duplicate placement)
- Standard image adjustments (e.g., brightness/contrast optimization)
- Potentially problematic manipulations (e.g., selective removal of artifacts)
- Document Review Process: Maintain records of analysis results and corrective actions taken.
Troubleshooting:
- If numerous false positives occur, verify that image compression hasn't introduced artifacts
- For unclear flags, consult original raw images to verify authenticity
- If uncertain about classification of findings, contact your institution's research integrity office [38]
Protocol 2: Text Originality Screening with iThenticate
Purpose: To identify potential text similarity issues, improper citation, or inadvertent plagiarism in manuscript text.
Materials and Equipment:
- iThenticate software access (institutional subscription) [38] [39]
- Complete manuscript text (including references, figure legends, and supplemental information)
- Journal-specific plagiarism policies
Procedure:
- Prepare Manuscript Text: Compile the complete manuscript text, excluding author identifiers if desired.
- Configure Exclusion Settings:
- Exclude quotes and references (if journal policies permit) [39]
- Exclude bibliographic elements
- Include/exclude preprint repositories based on journal policy
- Run Similarity Analysis: Submit manuscript to iThenticate for comparison against academic database.
- Interpret Similarity Report:
- Review Overall Similarity Score as initial indicator
- Examine source-by-source matches for context
- Differentiate between:
- Address Identified Issues:
- Properly paraphrase matched text with appropriate citation
- Use quotation marks for directly copied text with citation
- Obtain permissions for extensive reproductions
Troubleshooting:
- For high similarity with author's own work, determine if journal requires specific disclosure
- For discipline-specific terminology causing false matches, verify whether rewriting is possible
- Consult journal guidelines if uncertain about acceptable similarity thresholds
Research Reagent Solutions for Integrity Screening
Essential Digital Materials for Screening
| Research Reagent Solution | Function | Application Notes |
|---|---|---|
| Proofig Software [38] | AI-powered image integrity verification | Critical for materials characterization images; ensures microscopy and spectroscopy data authenticity |
| iThenticate Software [38] [39] | Text similarity and plagiarism detection | Essential for literature reviews and methodology sections; helps maintain textual originality |
| Reference Management Software | Citation organization and formatting | Reduces inadvertent citation errors; facilitates proper attribution |
| Institutional Research Integrity Office [38] | Guidance on ambiguous screening results | Consult for cases where error vs. misconduct is uncertain; provides protocol clarification |
Analysis and Interpretation of Screening Results
Evaluating Image Analysis Findings
When reviewing Proofig results, materials scientists must distinguish between acceptable image processing and problematic manipulation. For microscopic characterization of materials, certain adjustments like uniform brightness/contrast enhancement may be acceptable if applied to the entire image and properly disclosed. However, selective modification that misrepresents material structures or properties constitutes serious misconduct [38].
Common image issues in materials science manuscripts include:
- Inadvertent duplication of similar-looking material morphology images
- Inconsistent processing within figure panels showing comparative materials
- Cropping that eliminates important contextual scale information
Researchers should maintain original, unprocessed images for all published figures to verify authenticity if questioned. The screening process should be documented, including how flagged issues were addressed.
Interpreting Text Similarity Reports
iThenticate's Similarity Score requires careful contextual interpretation by subject-matter experts. For materials science manuscripts, certain technical descriptions of standard methodologies may naturally exhibit similarity without indicating plagiarism [39].
Consider these thresholds as guidelines for further investigation:
- <5% similarity: Typically minimal concern unless concentrated in single source
- 5-15% similarity: Requires source-by-source review for proper attribution
- >15% similarity: Warrants comprehensive revision and careful analysis
Materials scientists should pay particular attention to:
- Methodology sections describing standard synthesis protocols
- Literature reviews citing established foundational knowledge
- Descriptions of common characterization techniques (XRD, SEM, TEM, etc.)
When similarity is identified with the author's own previous publications, journals may have specific policies regarding acceptable text reuse, particularly for methods sections [39].
Integration with Broader Research Integrity Framework
Proactive manuscript screening represents one essential component of a comprehensive research integrity strategy for materials science and drug development. This practice aligns with broader initiatives such as the STM Integrity Hub, which provides a modular platform for identifying manuscripts that violate research integrity norms before they enter the publication cycle [40].
Implementing systematic screening protocols demonstrates institutional commitment to research quality and ethical scholarship. When integrated with proper mentorship, documentation practices, and reproducibility measures, pre-submission screening significantly strengthens the credibility of published materials science research.
By adopting these proactive approaches, researchers contribute to safeguarding the scholarly record while accelerating the dissemination of robust, reliable scientific knowledge in the materials science and drug development fields.
In the modern research landscape, particularly in fields like materials science and drug development, upholding research integrity has become increasingly complex. The fundamental principles of research integrity—reliability, honesty, respect, and accountability—form the bedrock of scientific progress [41]. However, these principles now face unprecedented challenges from digital threats, including sophisticated plagiarism and the rapid emergence of AI-generated content. The scientific community publishes over 2.5 million manuscripts annually, with studies indicating that a significant portion may contain integrity issues, including image duplication, manipulation, or textual plagiarism [31]. Furthermore, generative AI tools have introduced new ethical dilemmas, enabling the creation of seemingly original text that may obscure true authorship and originality.
Software solutions like iThenticate have emerged as critical tools for journals, universities, and research institutions to screen for potential misconduct. These tools help maintain the credibility of the scientific record by identifying textual overlaps and, increasingly, AI-generated content. For materials science researchers, whose work often involves substantial public funding and significant implications for technology development, ensuring originality is not merely an administrative requirement but a fundamental ethical obligation. This technical guide examines the capabilities, implementation, and limitations of plagiarism detection software, with a specific focus on iThenticate, within the broader context of research integrity frameworks.
Understanding Plagiarism Detection Software
Core Functionality and Databases
Plagiarism detection software like iThenticate operates by comparing submitted documents against an extensive database of scholarly content to identify textual overlaps. iThenticate's database includes premium scholarly journals, books, law reviews, patents, dissertations and theses, pre-prints, conference proceedings, and internet pages [42]. This comprehensive coverage is crucial for materials science research, where information spans journal articles, conference proceedings, patent literature, and technical reports. The system generates a "Similarity Report" that highlights matching text and provides an overall "Similarity Index" (percentage of overlapping text) while carefully using the term "similarity" rather than "plagiarism" to emphasize that human judgment is required for final assessment [43].
The technical workflow involves document submission in supported formats (including DOC, DOCX, PDF, TXT, and others), after which the system performs automated text extraction and comparison against its database [42]. For research institutions, iThenticate offers the option to establish a private repository to store internal documents, enabling detection of text similarity across submissions within the same organization [42]. This feature is particularly valuable for identifying research misconduct, including self-plagiarism, within large research institutions or corporate R&D departments.
Evolution into AI Detection
With the proliferation of large language models (LLMs), iThenticate has expanded its capabilities beyond traditional text matching to include AI writing detection [44]. This enhancement addresses the emerging challenge of identifying content generated by AI tools rather than human authors. The AI detection feature is available for multiple languages, including English, Spanish, and Japanese, with each language utilizing a separate, specially trained model [45]. The system has been updated to detect content generated by various GPT models, including GPT-4, GPT-4o, and GPT-4o-mini [45].
A significant advancement is the August 2025 update enabling AI bypasser detection, which identifies text that was initially AI-generated but subsequently modified by "humanizer" tools designed to evade detection [44] [45]. This capability addresses an increasingly common practice where users attempt to disguise AI-generated content by making it appear more human-like. The AI writing report categorizes content and highlights text segments that the model predicts were likely AI-generated, using color-coded indicators for easy interpretation [44].
Table 1: iThenticate AI Writing Detection Capabilities by Language
| Language | Available Since | Detectable LLMs | Detection Threshold |
|---|---|---|---|
| English | Already available | GPT-3.5, GPT-4, GPT-4o, GPT-4o-mini | Scores below 20% not surfaced |
| Spanish | September 2024 | GPT-3.5, GPT-4 | Scores below 20% not surfaced |
| Japanese | April 2025 | GPT-4, GPT-4o, GPT-4o-mini | Scores below 20% not surfaced |
iThenticate Technical Specifications and Workflows
System Requirements and Submission Protocols
Implementing iThenticate effectively requires understanding its technical specifications and submission protocols. The system supports major operating systems including Microsoft Windows 7+ and Mac OS X v10.4.11+, with a minimum of 3GB RAM, 1024x768 display resolution, and a broadband internet connection [42]. Supported browsers include the latest and one previous version of Chrome, Firefox, Safari, and Windows browsers, with JavaScript enabled and cookies allowed from ithenticate.com [42].
For document submission, iThenticate accepts multiple file types relevant to researchers:
- Microsoft Word documents (DOC and DOCX)
- Word XML and Rich Text Format (RTF)
- Portable Document Format (PDF) created with Adobe or Microsoft Word
- Plain text (TXT), HTML, and Corel WordPerfect (WPD)
- Adobe PostScript files
Documents must not exceed 800 pages, 100MB file size, or 25,000 words [42]. The system also supports ZIP file uploads containing up to 1,000 files (increased from 100 in September 2025), facilitating batch processing of multiple documents [45]. This enhancement is particularly useful for research institutions screening numerous theses or grant applications simultaneously.
The submission interface has been redesigned in 2025 to provide a clearer, more streamlined experience [45]. Once submitted, documents are typically processed within "one minute to several minutes, depending on document length" [42]. Users can monitor submission status through their account interface, with "pending" indications until results are ready, at which point a percentage "Similarity Index" appears [42].
Administrative Features and Data Management
For institutional administrators, iThenticate provides robust management capabilities. The November 2025 update introduced AI writing detection data export functionality, allowing administrators to download key metrics as CSV files for deeper analysis of AI writing trends and usage within their organization [44] [45]. This feature supports flexible analysis of AI detection data and helps identify patterns in AI writing usage, thereby improving organizational understanding of AI's impact on research integrity.
Administrators also benefit from enhanced access control features. The April 2025 update enabled Single Sign-On (SSO) access restrictions based on user attributes from identity providers (such as department, role, or location) [44] [45]. This allows institutions to streamline access management using existing identity provider groups and attributes, maintaining stronger security by ensuring only authorized team members can access the account.
Additionally, administrators can download user lists as CSV files from the User area of their iThenticate 2.0 account, including Active, Pending, or Deactivated users [45]. This facilitates user management and reporting for institutional compliance purposes.
Diagram 1: iThenticate Administrative Data Flow
Complementary Research Integrity Tools
Image Integrity Detection with Proofig AI
While iThenticate focuses on textual analysis, research integrity encompasses other forms of misconduct, particularly image manipulation. Proofig AI addresses this critical area by automatically detecting image duplication and manipulation in scientific publications [31]. This capability is especially relevant for materials science research, where microscopy images, Western blots, flow cytometry data, and other visual representations are fundamental to reporting findings.
Proofig AI identifies several categories of image integrity issues:
- Detection of alteration or manipulation within a single sub-image, including cloning, editing, deletion, and splicing
- Detection of duplication or reuse within a single manuscript, even when images have been scaled, rotated, flipped, or partially overlapped
- Detection of reuse of sub-images from published manuscripts using a database containing tens of millions of images from PubMed
- Detection of AI-generated microscopy images from the most widely used models
- Detection of self-plagiarism through comparison with a personalized repository of a researcher's previously published work
The platform analyzes entire papers in minutes, scanning for issues across multiple image types common in materials science and life sciences research, including microscopies (confocal, light, fluorescence, and electron), histology slides, pathology slides, Western blot bands, gel electrophoresis, flow cytometry (FC), fluorescence-activated cell sorting (FACS), cell culture, in-vitro, and in-vivo images [31]. According to Proofig's metrics, approximately 25% of analyzed manuscripts contain findings related to image integrity issues [31].
Beyond detection software, educational resources play a crucial role in promoting research integrity. The Office of Research Integrity (ORI) offers online learning tools that explain appropriate image processing practices in science [46]. These resources provide twelve guidelines for best practices in image processing, with illustrative videos, common mistakes, and interactive case studies.
Similarly, Springer Nature's Research Integrity in Science and Education (RISE) initiative provides free access to research integrity training resources, aiming to empower early career researchers with the knowledge and tools needed to practice and promote research integrity [47]. Such educational interventions are essential for preventing integrity breaches before they occur, moving beyond mere detection to cultural change within research communities.
Table 2: Research Integrity Software Solutions Comparison
| Tool | Primary Function | Detection Capabilities | Relevance to Materials Science |
|---|---|---|---|
| iThenticate | Text similarity and AI writing detection | Textual overlap, AI-generated content, AI bypasser tools | High for manuscripts, theses, grant proposals |
| Proofig AI | Image integrity verification | Image duplication, manipulation, AI-generated images | Critical for microscopy, spectrometry, experimental data |
| Crossref Similarity Check | Text similarity checking | Textual overlap across scholarly content | High for publication preparation |
Implementation Framework for Research Institutions
Developing Effective Plagiarism Detection Protocols
Implementing an effective research integrity strategy requires more than simply acquiring software tools. Research institutions should develop comprehensive protocols that define different forms of plagiarism and establish clear procedures for addressing them. According to best practices outlined in scholarly publishing resources, there are four main categories of potential plagiarism that institutions should address [39]:
- Direct plagiarism: Unattributed verbatim or nearly verbatim copying of sentences and paragraphs from another's work
- Duplicate or redundant publication: Direct or nearly verbatim copying of one's own work without citing the original publication
- Text recycling or self-plagiarism: Copying parts of one's published works into a new manuscript without citation
- Salami slicing or minor overlap: Including elements similar to one's published works without clear recycling
For materials science research, particular attention should be paid to standard terminology and common methodological descriptions that may legitimately appear similar across multiple papers. As noted in a 2025 opinion paper, high similarity indexes can sometimes result from the legitimate use of common terms and phrases in scientific research rather than actual plagiarism [43]. This includes standard terminology for describing materials, methods, instrumentation, and statistical analyses.
Diagram 2: Research Integrity Screening Workflow
Interpretation Guidelines for Similarity Reports
Proper interpretation of similarity reports is crucial for effective implementation. Institutions should train staff to understand that:
- High similarity scores do not automatically indicate plagiarism – they may result from properly quoted and cited material, standard scientific terminology, or mandatory statements (ethics, disclosures, funding) [43] [39]
- Low similarity scores do not guarantee originality – sophisticated plagiarism may involve translation, paraphrasing, or concept theft that evades text matching
- Similarity Index should be considered alongside contextual factors – overlaps in introduction and method sections may be more acceptable than in results and discussion sections
The iThenticate system allows administrators to configure exclusion criteria to filter out certain types of content (such as quotes, references, or preprints) from similarity calculations, helping to focus attention on more substantive matches [39]. Institutions should establish clear guidelines for when and how to use these exclusions based on their specific needs and policies.
For AI writing detection, users should understand that scores below 20% are not surfaced to minimize potential false positives, and any AI detection should not be used as the sole basis for adverse actions against researchers [45]. The system is designed to facilitate further investigation and human judgment rather than provide definitive conclusions about misconduct.
Limitations and Ethical Considerations
Technical and Interpretive Limitations
While software tools like iThenticate provide valuable screening capabilities, they have important limitations that institutions must recognize. A significant challenge is the potential for falsely inflated similarity indexes due to common scientific terminology, standard methodological descriptions, or mandatory statements [43]. In materials science, standard terms for material synthesis, characterization techniques, and analytical methods may appear similar across multiple papers without indicating plagiarism.
Additionally, these tools cannot detect paraphrased plagiarism where ideas or concepts are stolen but reworded, particularly when sophisticated paraphrasing tools or "back translation" (translating to another language and back to English) are used [43]. The August 2025 update addressing AI bypasser tools represents progress against some evasion techniques, but the cat-and-mouse game between detection and evasion continues.
Perhaps most importantly, these tools cannot assess whether overlapping text is properly attributed – they highlight matches but cannot determine if those matches are appropriately cited [43] [39]. Human judgment remains essential for determining whether matching text represents plagiarism or legitimate scholarly practice.
Ethical Implementation Framework
The use of plagiarism detection software raises important ethical considerations for research institutions. Firstly, there is a risk of over-reliance on quantitative metrics like the Similarity Index, which may lead to bureaucratic, numbers-driven assessments rather than qualitative evaluation of research integrity [43]. Institutions should use these tools as screening aids rather than decision-makers.
Secondly, transparency with researchers about the use of these tools is essential. Authors should generally be informed when their work will be screened using plagiarism detection software and understand the principles being applied [39]. This promotes a culture of integrity rather than simply punishment.
Finally, institutions should balance detection with education and prevention. Resources like the Springer Nature RISE initiative [47] and ORI educational materials [46] can help researchers, particularly early-career scientists, understand and adhere to integrity standards before submitting their work.
Table 3: Research Reagent Solutions for Integrity Implementation
| Component | Function | Implementation Considerations |
|---|---|---|
| iThenticate Software | Text similarity and AI detection | Integrate with existing manuscript tracking systems; train administrators on interpretation |
| Proofig AI | Image integrity verification | Particularly valuable for experimental sciences; implement pre-submission screening |
| Educational Resources | Preventative training | Utilize ORI and RISE materials; develop discipline-specific examples |
| Institutional Policies | Framework for implementation | Define plagiarism types clearly; establish investigation procedures |
| SSO Integration | Access management | Leverage existing identity providers; configure attribute-based access |
Software tools like iThenticate play an increasingly sophisticated role in combating plagiarism and AI-generated text in materials science research and related fields. Their evolution from simple text-matching systems to AI-writing detectors capable of identifying bypasser tools reflects the rapidly changing landscape of research integrity threats. When implemented as part of a comprehensive research integrity strategy—including complementary image checking tools like Proofig AI, clear institutional policies, and ongoing researcher education—these tools provide valuable support for maintaining scholarly standards.
However, technology alone cannot ensure research integrity. The limitations of these systems, including potentially inflated similarity indexes from standard scientific terminology and the inability to assess proper attribution, mean that human expertise and judgment remain irreplaceable. For materials science researchers and drug development professionals, whose work has significant scientific and societal implications, combining technological tools with ethical training and institutional support offers the most promising path toward sustaining research integrity in the digital age. As the scholarly community continues to grapple with emerging challenges like generative AI, maintaining this balance between technological assistance and human judgment will be crucial for fostering trust in research outcomes.
Research integrity (RI) is defined as the adherence to ethical principles, deontological duties, and professional standards necessary for the responsible conduct of scientific research [48]. It incorporates principles of honesty, transparency, and respect for ethical standards throughout all research stages, from design and data collection to analysis, reporting, and publication [11]. In the fast-evolving field of materials science—where breakthroughs in metamaterials, aerogels, and sustainable composites promise to transform industries from construction to communications—upholding these principles is not merely an ethical obligation but a practical necessity for sustaining scientific progress and public trust [49].
The consequences of research misconduct extend beyond individual careers, eroding public confidence in science, wasting valuable resources, and undermining evidence-based policymaking [1]. For materials science researchers, whose work often directly impacts product safety, building integrity, and environmental sustainability, maintaining the highest standards of integrity is particularly crucial. This guide provides a comprehensive framework for establishing a robust culture of research integrity through effective training, committed leadership, and transparent policies, specifically contextualized for the materials science research community.
Core Principles and Regulatory Framework
Foundational Values and Definitions
The responsible conduct of research is built upon a foundation of shared values that bind all researchers together, regardless of their specific discipline. According to the Office of Research Integrity (ORI), these core values include [50]:
- Honesty: Conveying information truthfully and honoring commitments
- Accuracy: Reporting findings precisely and taking care to avoid errors
- Efficiency: Using resources wisely and avoiding waste
- Objectivity: Letting facts speak for themselves and avoiding improper bias
Research misconduct is specifically defined as fabrication, falsification, or plagiarism (FFP) in proposing, performing, reviewing, or reporting research [1]. It is crucial to note that honest errors or differences in scientific opinion do not constitute misconduct.
Table 1: Categories of Research Misconduct and Their Definitions
| Category | Definition | Example in Materials Science Context |
|---|---|---|
| Fabrication | Making up data, results, or scientific details without actual observation or experiment | Inventing characterization data for a new metamaterial's electromagnetic properties |
| Falsification | Manipulating research materials, equipment, processes, or changing/omitting data or results | Manipulating electron microscopy images to show improved porosity in aerogel structures |
| Plagiarism | Appropriating another person's ideas, processes, results, or words without giving appropriate credit | Copying another researcher's methodology for self-healing concrete without citation |
Evolving Regulatory Landscape
The regulatory framework governing research integrity is continually evolving to meet the demands of modern research environments. Significant updates include:
The 2024 ORI Final Rule: In January 2025, the U.S. Office of Research Integrity implemented a comprehensive update to the Public Health Service (PHS) Policies on Research Misconduct, marking the first major overhaul since 2005 [51]. Key enhancements include:
- Clarified definitions for key terms like recklessness, honest error, and self-plagiarism
- Extended timeline for institutional inquiries from 60 to 90 days
- Flexibility in expanding investigations without restarting the entire process
- Streamlined procedures for international collaborations and multi-institutional studies [1]
Institutions receiving PHS funding must comply with these updated regulations by January 1, 2026, and must submit new policies and procedures with their 2025 Annual Report, due April 30, 2026 [51].
Effective Research Integrity Training Methodologies
Evidence-Based Training Approaches
Effective research integrity training moves beyond simple compliance to foster genuine understanding and adoption of ethical research practices. Recent meta-reviews indicate that the most effective RI training incorporates:
- Longer cases with moderate complexity that reflect real-world research dilemmas
- Multiple instructors who are experts in their professional domains
- Frequent practice opportunities spaced throughout the instructional period
- Active learning methods including debates, role-plays, computer simulations, and self-reflection [52]
A study on early-career researchers attending an institutional RI course demonstrated significant improvements in understanding after targeted training. The percentage of participants reporting high understanding of rules and procedures related to research misconduct increased from 38.5% to 61.5% after course completion [48].
Table 2: Pre- and Post-Training Perceptions of Early-Career Researchers
| Perception Area | Pre-Course Percentage | Post-Course Percentage |
|---|---|---|
| High understanding of rules and procedures related to research misconduct | 38.5% | 61.5% |
| Lack of awareness on the extent of misconduct | 46.2% | 69.2% |
| Belief that lack of research ethics consultation services strongly affects research misconduct | 15.4% | 61.5% |
The Taxonomy for Research Integrity Training (TRIT)
The Taxonomy for Research Integrity Training (TRIT), based on Kirkpatrick's four levels of evaluation, provides a structured framework for designing and evaluating RI training programs [52]. This model enables institutions to align training activities with specific outcomes across multiple levels:
Figure 1: The Kirkpatrick evaluation model applied to research integrity training demonstrates a progression from immediate reactions to broader societal impact.
Experimental Protocol: Implementing a Virtue Ethics Approach
The VIRT2UE project, a Horizon 2020 train-the-trainer program, has developed an evidence-based protocol for RI training that emphasizes virtue ethics [48]. The methodology includes:
Session 1: Independent Preparation (4 hours)
- Participants consult introductory materials (articles, videos) from the Embassy of Good Science platform
- Complete pre-course questionnaire assessing baseline perceptions of RI issues
Session 2: Facilitated Online Training (8 hours)
- Trainers provide an overview of virtue ethics and its application to RI
- Presentation of real-world ethical dilemmas from materials science research
- Facilitated discussions where participants share personal experiences and perspectives
- Small-group exercises analyzing case studies specific to materials characterization, data interpretation, and authorship
- Completion of post-course questionnaire to measure attitude changes
This approach has demonstrated statistically significant improvements in participants' understanding of RI principles and their ability to recognize and address ethical dilemmas in their research [48].
Leadership Commitment and Institutional Structures
The Critical Role of Leadership
Institutional leadership represents the single most important component in establishing a culture of research integrity. As noted by Gunsalus (1993), "If the institution's leaders are committed to integrity in research and act on that commitment, the campus will follow that lead; conversely, if the perception develops that the leaders pay only lip service to ethical conduct, the campus will adopt the same attitude" [53].
Effective leadership in research integrity involves:
- Modeling ethical behavior in all research activities and decisions
- Allocating sufficient resources for RI training, oversight, and compliance
- Establishing clear accountability structures with defined roles and responsibilities
- Creating an environment where ethical concerns can be raised without fear of retaliation
Institutional Reporting and Investigation Workflow
A transparent, fair, and efficient process for addressing allegations of research misconduct is essential for maintaining institutional credibility. The following diagram illustrates an optimal workflow based on updated ORI guidelines:
Figure 2: Institutional workflow for handling research misconduct allegations, reflecting updated ORI guidelines including extended inquiry timeline.
Whistleblower Protection Mechanisms
Protecting individuals who report potential research misconduct is critical for maintaining institutional integrity. Research institutions should establish mechanisms that allow whistleblowers to expose unethical conduct without fear of retaliation [11]. Effective protection includes:
- Clear confidentiality policies governing the handling of misconduct reports
- Explicit non-retaliation commitments for good-faith reporters
- Multiple reporting channels to accommodate different comfort levels
- Support services for individuals involved in misconduct proceedings
Transparent Policies and Prevention Strategies
Implementing the ORI Final Rule Requirements
The updated 2024 PHS Policies on Research Misconduct provide institutions with greater flexibility while maintaining rigorous standards. Key implementation requirements include:
- Policy Revision: Institutions must revise their research misconduct policies to comply with the updated regulations by January 1, 2026 [54]
- Documentation Standards: Clarified requirements for documenting the assessment phase as a pre-investigation component
- Confidentiality Obligations: Specific guidance on maintaining confidentiality throughout misconduct proceedings
- Journal Notification: Institutional discretion to notify journals about corrections to the research record due to misconduct findings [51]
Prevention Through Education and Infrastructure
Preventing research misconduct requires a proactive approach that combines education, clear policies, and modern research infrastructure:
Comprehensive Education Programs
- Integrate RI training into graduate curricula and mentor development programs
- Provide discipline-specific case studies relevant to materials science, such as data handling in high-throughput materials characterization or authorship standards in multi-disciplinary collaborations
- Offer regular updates on evolving ethical standards and regulatory requirements
Robust Research Infrastructure
- Implement electronic research administration (eRA) systems to automate compliance checks and track training completion [1]
- Establish secure data management platforms with appropriate version control and access logging
- Develop research methodology consultation services to support proper experimental design and statistical analysis
Clear, Accessible Policies
- Define authorship criteria explicitly, addressing disciplinary norms in materials science
- Establish data retention protocols appropriate for different types of materials research data
- Outline procedures for addressing conflicts of interest, particularly in industry-academia collaborations
Materials Science-Specific Integrity Considerations
Emerging Technologies and Ethical Challenges
The rapid advancement of materials science presents unique integrity challenges that require specialized attention:
Metamaterials Research
- Verification challenges: The exotic properties of metamaterials (e.g., negative refractive index, electromagnetic wave manipulation) require rigorous validation protocols [49]
- Reproducibility issues: Complex fabrication processes using nanoscale patterning can lead to significant sample-to-sample variation
- Data interpretation: Sophisticated simulation data must be clearly distinguished from experimental results
Sustainable Materials Development
- Environmental claims: Lifecycle assessments and sustainability assertions for new materials (e.g., bamboo composites, self-healing concrete) must be supported by comprehensive data [49]
- Standardized testing: Performance claims for sustainable alternatives must be evaluated using consistent methodologies across studies
High-Throughput Materials Discovery
- Data management: Automated experimentation generates massive datasets requiring careful curation and documentation
- Methodology transparency: Screening algorithms and selection criteria must be fully disclosed to enable replication
Research Reagent Solutions for Materials Science
Table 3: Essential Research Reagents and Materials in Advanced Materials Science
| Reagent/Material | Function/Application | Integrity Considerations |
|---|---|---|
| MXenes and MOFs | Used in aerogel composites to enhance electrical conductivity and specific capacitance [49] | Proper characterization of composition and purity; disclosure of commercial sources |
| Polyvinylidene difluoride (PVDF) | Base material for metamaterials used in energy harvesting applications [49] | Consistent reporting of material properties and processing conditions |
| Phase-change materials (paraffin wax, salt hydrates) | Thermal energy storage mediums for decarbonizing buildings [49] | Accurate reporting of thermal cycling stability and degradation metrics |
| Bamboo fiber composites | Sustainable alternative to pure polymers in consumer products [49] | Transparent lifecycle assessments and mechanical property testing protocols |
| Tungsten trioxide and nickel oxide | Electrochromic materials for smart window technologies [49] | Standardized performance testing under realistic environmental conditions |
Establishing a robust culture of research integrity in materials science requires a multifaceted, sustained approach that integrates effective training, committed leadership, and transparent policies. The recent updates to research misconduct policies provide an opportunity for institutions to revitalize their commitment to research integrity with greater clarity and flexibility.
For the materials science community specifically, this means:
- Developing discipline-specific training that addresses the unique ethical challenges of advanced materials research
- Implementing robust data management practices suitable for complex characterization data and computational simulations
- Fostering mentor-mentee relationships that emphasize ethical research practices alongside technical skills
- Creating collaborative environments where ethical discussions are integrated into regular research activities
By embracing these principles, the materials science research community can not only comply with regulatory requirements but also advance the quality, reliability, and societal impact of their groundbreaking work—from metamaterials and aerogels to sustainable building solutions and thermally adaptive fabrics [49]. Ultimately, a culture of integrity protects both individual researchers and the collective scientific enterprise, ensuring that materials science continues to contribute responsibly to technological progress and societal well-being.
Identifying and Addressing Common Integrity Challenges
Understanding and Avoiding Self-Plagiarism and Duplicative Publication
Research integrity constitutes the foundation of credible scientific endeavor, encompassing a set of moral and ethical standards that guide all research activities, from study design and data collection to analysis, reporting, and publication [11]. At its core, research integrity incorporates principles of honesty, transparency, and respect for established ethical standards, serving to maintain the credibility of scientific research and prevent scientific misconduct [11]. Within this framework, self-plagiarism and duplicative publication represent significant challenges that compromise these principles, particularly in fields like materials science and drug development where the accurate accumulation of knowledge is paramount.
Self-plagiarism, often termed "text recycling," involves improperly reusing one's own prior written work without appropriate attribution [55]. For example, a researcher might take sections of a previously published methods description, recycle substantial portions of text in a new introduction, or submit what is substantially the same paper to multiple venues with minor modifications. Unlike traditional plagiarism, which involves appropriating others' work, self-plagiarism involves recycling one's own intellectual property [55]. A closely related concept is redundant or duplicate publication, which occurs when an author publishes identical or nearly identical content in multiple journals without alerting editors or readers to its prior publication [56] [57]. This practice is sometimes called 'double-dipping' in academic contexts, analogous to submitting the same paper for credit in multiple courses [56].
The distinction between proper and improper use of one's prior work hinges on deception and transparency. When authors transparently disclose their reuse of previous work with proper citation, they maintain academic honesty. However, when such reuse occurs without disclosure, it misleads readers and editors into believing they are encountering entirely new scholarly work [55]. This deception fundamentally undermines research integrity by distorting the scientific record and misrepresenting the novelty of the research.
The Problem Spectrum: From Text Recycling to Salami Slicing
Self-plagiarism and duplicative publication manifest in several forms with varying degrees of ethical severity. Understanding this spectrum is crucial for researchers seeking to maintain ethical standards. The table below categorizes and describes the primary forms of this misconduct.
Table 1: Types and Characteristics of Self-Plagiarism and Duplicative Publication
| Type | Description | Common Manifestations | Ethical Severity |
|---|---|---|---|
| Text Recycling | Reusing one's own previously published text, either verbatim or with minor modifications, without quotation or citation [58]. | Methods sections, literature reviews, boilerplate descriptions [57]. | Moderate - violates copyright and transparency standards. |
| Duplicate Publication | Publishing an identical paper in multiple journals, sometimes with changes to title, author order, or abstract [56]. | Submitting same research to different journals; publishing same study in different languages without disclosure [56]. | High - directly misrepresents novelty and wastes resources. |
| Salami Slicing | Dividing a single coherent research study into multiple smaller publications to artificially increase publication count [57]. | Publishing results from one experiment across several papers; dividing a comprehensive study by minor variables [57]. | High - distorts the research record and misleads the scientific community. |
| Redundant Publication | Publishing new work that contains substantial portions of previously published work without appropriate referencing [57]. | Adding small amount of new data to previously published paper; reusing substantial portions of methodology or results [57]. | Moderate to High - depends on the extent and nature of duplication. |
The materials and methods section is particularly susceptible to text recycling allegations, as researchers often use similar methodologies across multiple studies [57]. However, the ethical evaluation depends on both the extent and nature of the duplication. According to the Committee on Publication Ethics (COPE), duplication spread across a paper in short phrases may be less concerning than duplication concentrated in several paragraphs, and the limited use of identical phrases describing common methodology may not require investigation [57].
Table 2: Acceptable versus Unacceptable Recycling of Research Content
| Research Component | Potentially Acceptable Reuse | Unacceptable Reuse |
|---|---|---|
| Methods Description | Limited, identical phrases for common methods; detailed citation of previous methodology [57]. | Copying extensive, unique methodological descriptions without attribution. |
| Literature Review | Building upon previous reviews with proper citation; summarizing essential background again with new synthesis. | Reproducing substantial portions of text from previous reviews without significant addition. |
| Data Analysis | Re-analysis of research data with new tools or new research questions [57]. | Presenting the same analysis and interpretation as previously published. |
| Overall Study | Publishing from a thesis or dissertation depending on journal policy; transparent secondary analysis of large datasets [57]. | Publishing the same core study in multiple journals without cross-reference. |
Why Self-Plagiarism Matters: Consequences for the Scientific Ecosystem
Ethical and Philosophical Implications
The most fundamental objection to self-plagiarism concerns its violation of the implicit contract between researchers and the scientific community. Each published manuscript is expected to contribute new knowledge and results that advance our collective understanding [58]. When manuscripts contain uncited recycled information, they violate this expectation and misrepresent the novelty of the research. This erosion of trust extends beyond individual researchers to the broader scientific enterprise, potentially diminishing public confidence in science [11] [10].
Self-plagiarism and redundant publications also distort the scientific record by creating an inaccurate perception of productivity and progress. Salami slicing, in particular, makes it difficult for other researchers to grasp the full scope of a study and can lead to the overestimation of evidence through multiple counting of the same research [57]. This waste of limited scientific resources—editorial time, peer review effort, and journal space—represents an inefficient allocation that could otherwise support genuinely novel research.
Practical and Professional Consequences
From a practical standpoint, self-plagiarism constitutes copyright infringement in many cases. When researchers publish in traditional journals, they typically transfer copyright to the publisher [58]. Consequently, even reusing one's own words without permission violates copyright law, not merely ethical norms. Open access journals using Creative Commons licenses may allow reuse with attribution, but the requirement for proper citation remains [58].
Journals actively combat this problem using sophisticated similarity detection software like iThenticate [58]. When self-plagiarism is detected, consequences can include immediate rejection, retraction of published articles, and notification of the authors' institution [57]. Such events can severely damage a researcher's reputation, potentially affecting promotion, tenure, and future funding opportunities [57]. In extreme cases, redundant publication has become a significant factor in the growing phenomenon of scientific paper retractions [57].
Methodologies for Prevention: A Technical Guide for Researchers
Experimental Design and Documentation Protocols
Preventing self-plagiarism begins with rigorous experimental design and documentation practices that clearly delineate the novel contributions of each study.
- Define Research Questions Precisely: Each research project should address a unique, well-defined question that represents a distinct contribution to the field. Document this research question explicitly at the study design phase to maintain focus throughout the research process.
- Establish Comprehensive Documentation Systems: Maintain detailed laboratory notebooks or electronic records that clearly track which data and analyses have been previously published. This practice creates an audit trail that helps researchers avoid inadvertent reuse of already published material.
- Implement Version Control for Methodologies: When methodologies are reused or modified across studies, maintain version-controlled descriptions that highlight innovations and differences from previous applications. This practice facilitates appropriate citation of previous methodological work.
The actual writing process presents critical opportunities for preventing improper text recycling.
- Create New Documents for Each Manuscript: Rather than starting from previous drafts, begin each new manuscript with a blank document to avoid the temptation of copying existing text [58]. This practice encourages fresh articulation of ideas and methods.
- Practice Transparent Self-Citation: When building upon previous work, cite your own publications as thoroughly as you would cite others' work. Directly acknowledge when descriptions of methods or background draw substantially from prior publications.
- Employ Quotation for Verbatim Text: If reusing specific, uniquely descriptive text from a previous publication is necessary, employ quotation marks with a citation, though this should be rare in scientific writing.
The following flowchart illustrates a recommended decision process for appropriately reusing one's own prior content:
Table 3: Research Reagent Solutions for Maintaining Documentation and Integrity
| Tool Category | Specific Examples | Function in Preventing Self-Plagiarism |
|---|---|---|
| Similarity Detection Software | iThenticate, Turnitin, Grammarly, Copyleaks [57] | Pre-submission checking for unintended text recycling; identifying proper citation needs. |
| Reference Management Tools | Zotero, Mendeley, EndNote | Systematic tracking of all relevant publications, including researcher's own work. |
| Document Versioning Systems | Git, Overleaf Version History | Maintaining clear records of manuscript development and content evolution. |
| Laboratory Notebooks | Electronic Lab Notebooks (ELNs), Physical Notebooks | Documenting which data and methodologies have been previously published. |
Institutional Responsibilities and Systemic Solutions
Upholding research integrity requires more than individual researcher effort; institutions must create environments that support ethical conduct through clear policies, education, and appropriate incentives.
Research institutions play a crucial role in establishing atmospheres that support integrity ideals while providing practical guidance and assistance to researchers [11]. This includes developing and enforcing clear protocols and guidelines for ethical publication practices [11]. Some institutions have established dedicated research integrity departments to monitor research projects, peer review evaluations, and dissemination of research results [11]. These departments can also protect research participants' rights and uphold standards of data recording.
Perhaps most importantly, institutions must reconsider incentive structures that prioritize quantity over quality in publications. The "publish or perish" culture and pressure to publish represent the most common reasons why authors produce redundant publications despite understanding the potential consequences [56] [57]. Institutional recognition systems that value the true scientific impact of research rather than mere publication counts can significantly reduce this pressure [57].
The following diagram illustrates the multi-stakeholder approach required to effectively address self-plagiarism:
Eliminating self-plagiarism and duplicative publication requires a fundamental commitment to authenticity throughout the research process. For materials science researchers and drug development professionals, whose work often builds incrementally on previous findings, this means practicing scrupulous transparency about what is genuinely new in each publication. It necessitates a cultural shift from measuring success by publication volume to valuing substantive contributions that advance the field.
The solutions combine individual responsibility with systemic support. Researchers must commit to rigorous self-citation practices, fresh articulation of methods and concepts, and transparent communication with editors about related publications. Simultaneously, institutions and funders must create reward systems that recognize ethical conduct and research quality rather than mere quantity. Journals must maintain clear policies and consistent enforcement while using similarity detection tools judiciously—focusing on the nature and significance of duplication rather than applying rigid percentage thresholds [57].
By embracing these practices, the materials science community can uphold the highest standards of research integrity, ensuring that the scientific record accurately reflects genuine progress and maintains the trust of both the scientific community and the public that ultimately benefits from its discoveries.
In the pursuit of scientific advancement, the human element introduces vulnerabilities that can compromise research integrity. This is particularly critical in fields like materials science and drug development, where methodological rigor directly impacts safety, efficacy, and reproducibility. Human factors in research span a continuum from unintentional errors—unplanned mistakes occurring despite adequate skill and knowledge—to questionable research practices (QRPs)—questionable methodological or analytical choices that introduce bias, often driven by systemic pressures [59] [60] [61]. Addressing this spectrum is essential for improving research integrity, as both ends threaten the validity of scientific findings, albeit through different mechanisms.
The prevalence of QRPs is alarmingly common. A 2022 article noted that approximately one in two researchers has engaged in at least one QRP over a three-year period [61]. These practices, while sometimes motivated by the "publish or perish" culture, collectively contribute to issues like the replication crisis, undermining trust in scientific literature [62] [60] [61]. Conversely, unintentional errors, stemming from factors like fatigue, high workload, or imperfect judgment, are an inherent part of human performance and require systematic management rather than blame [59] [63]. This guide provides a technical framework for identifying, managing, and mitigating these human factors to foster a more robust and reliable research environment.
Defining the Problem Space: Error Typologies and QRPs
A Taxonomy of Human Failure in Research
Understanding the specific nature of human failure is the first step toward effective mitigation. The following taxonomy, adapted from human factors engineering and research integrity literature, categorizes these failures for clearer analysis.
Diagram 1: A Taxonomy of Human Failure in Research
Inventory of Common Questionable Research Practices
QRPs are defined as "ways of producing, maintaining, sharing, analyzing, or interpreting data that are likely to produce misleading conclusions, typically in the interest of the researcher" [60]. A 2025 study systematically identified and classified 40 distinct QRPs across the research lifecycle [60]. The table below summarizes some of the most common practices, their typical phase in the research process, and their primary impact.
Table 1: Common Questionable Research Practices (QRPs) and Their Impacts
| Research Phase | QRP Name | Description | Primary Harm |
|---|---|---|---|
| Planning | Choosing biased measurements | Selecting measurement tools or methods that are likely to produce a desired outcome. | Compromised generalizability [60]. |
| Data Collection | Selective sampling | Manipulating participant selection or inclusion criteria to achieve a specific result. | Biased error rates, reduced replicability [60]. |
| Data Analysis | p-hacking | Running multiple statistical tests on data until a statistically significant result is found [61]. | Inflated false-positive rates, contributes to replication crisis [61]. |
| Data Analysis | HARKing | Hypothesizing After the Results are Known; presenting a post-hoc hypothesis as if it were a priori [60] [61]. | Inflated effect sizes, misleading literature [60]. |
| Writing & Publication | Selective Reporting | Only reporting results, variables, or studies that are significant or consistent with predictions; also called "cherry-picking" [60] [61]. | Skews meta-analyses, creates a biased published record [61]. |
| Writing & Publication | Improper referencing | Failing to credit the original source of an idea or concept, leading to plagiarism [61]. | Misattribution of credit, ethical breaches [61]. |
Quantitative Insights into QRP Prevalence and Drivers
Recent large-scale studies have provided quantitative data on the factors associated with QRPs. A 2025 survey of 3,005 social and medical researchers at Swedish universities revealed critical insights into the organizational and normative drivers.
Table 2: Factors Associated with QRP Prevalence from an Organizational Survey
| Factor Category | Specific Factor | Association with QRP Prevalence | Notes |
|---|---|---|---|
| Normative Environment | Counter Norm of "Biasedness" | Positive (40-60% of prevalence) | Opposite of universalism and skepticism; most important factor [62]. |
| Organizational Climate | Internal Competition | Positive association | Creates pressure that encourages QRPs [62]. |
| Organizational Climate | Group-level Ethics Discussions | Negative association | Consistent protective factor against QRPs [62]. |
| Policy & Training | Ethics Training & Policies | Marginal impact | Had only a minor effect on reducing QRP prevalence [62]. |
Mitigation Strategies: A Multi-layered Defense System
Foundational Principles: Fostering a Culture of Integrity
Creating a robust defense against human fallibility begins with the organizational culture and normative environment. Empirical evidence suggests that top-down measures like ethics training alone are insufficient if the underlying culture is flawed [62]. The "counter norm of Biasedness"—which opposes Mertonian principles of universalism and organized skepticism—was found to be the single most important factor, associated with 40-60% of the prevalence of questionable practices [62].
Key Cultural and Organizational Strategies:
- Promote Collaborative Climates: Actively reduce internal competition, which was positively associated with QRP prevalence [62].
- Facilitate Bottom-up Ethics Discussions: Encourage regular, group-level conversations about ethical dilemmas and integrity. This practice consistently displays a negative association with QRP prevalence [62].
- Leadership Commitment: Academic leaders should prioritize creating and maintaining an open, unbiased research environment where integrity is valued over mere output [62].
Technical and Methodological Solutions
For materials scientists and drug development professionals, implementing specific technical protocols and open science practices is a critical line of defense against both errors and QRPs.
1. Pre-registration and Registered Reports
- Protocol: Draft a detailed research plan including hypotheses, experimental design, materials and methods, and a statistical analysis plan before data collection begins.
- Rationale: This commitment device prevents practices like p-hacking and HARKing by locking in the research plan, ensuring the hypothesis is truly a priori [61].
- Execution: Submit the protocol to a registry such as the Open Science Framework (OSF) or seek a Registered Report from a participating journal, which provides peer review of the method before data collection [61].
2. Blind Data Analysis
- Protocol: A researcher not involved in data collection analyzes the data according to a pre-defined plan while blinded to experimental conditions. This can involve coding group assignments or using automated analysis scripts.
- Rationale: Reduces confirmation bias and analytical flexibility, preventing the analyst from subtly influencing results to match expectations [60].
3. Robust Experimental Documentation
- Protocol: Maintain a detailed, timestamped laboratory notebook (electronic or physical) that records all procedures, reagent details, instrument calibrations, environmental conditions, and any deviations from the protocol.
- Rationale: Mitigates unintentional errors by creating an audit trail, facilitates replication, and ensures proper attribution of concepts and techniques [63] [61]. This is crucial for complex materials synthesis and characterization workflows.
4. Power Analysis and Transparent Reporting
- Protocol: Conduct an a priori power analysis using statistical packages (e.g., the
pwrpackage in R) to determine the sample size required to detect an effect [61]. - Rationale: Ensures studies have sufficient statistical power, reducing the temptation to engage in p-hacking or selective reporting due to underpowered, non-significant initial results [61].
The following workflow diagram illustrates how these technical solutions integrate into a robust materials characterization study to mitigate human factors at key stages.
Diagram 2: An Integrated Workflow for Mitigating Human Factors in Research
Implementing the above strategies requires a suite of practical tools and resources. The following table details key solutions that support rigorous and transparent research practices.
Table 3: Research Reagent Solutions for Enhancing Integrity
| Tool Category | Specific Tool / Resource | Primary Function | Application in Materials Science / Drug Development |
|---|---|---|---|
| Pre-registration Platforms | Open Science Framework (OSF) Registries, BMJ Open | Publicly archive and timestamp research plans, hypotheses, and analysis protocols. | Register synthesis parameters, characterization methods, and analysis plans for new material development. |
| Citation Management | Zotero, Mendeley | Organize references, ensure proper attribution, and generate accurate bibliographies. | Manage literature on material properties or drug mechanisms, preventing improper referencing [61]. |
| Statistical Power Tools | pwr package in R, Superpower |
Calculate the necessary sample size or replicates to achieve sufficient statistical power. | Determine the number of independent synthesis trials or biological replicates needed for a reliable effect size. |
| Data & Code Repositories | Zenodo, Figshare, GitHub | Publicly share raw data, analysis code, and supplementary materials. | Share X-ray diffraction datasets, microscopy images, or synthesis codes to enable replication and scrutiny [60]. |
| Reporting Guidelines | CRediT (Contributor Roles Taxonomy) | Clearly define and attribute each contributor's role in the research process. | Specify contributions to conceptualization (e.g., catalyst design), methodology, investigation, and data analysis [61]. |
Managing the human factor in research requires a concerted shift from reactive blame to proactive system design. The empirical evidence is clear: while individual responsibility is crucial, the organizational climate and normative environment exert a far greater influence on the prevalence of detrimental practices [62]. A holistic strategy that combines cultural change—fostering collaboration, reducing biased norms, and encouraging ethics dialogues—with the widespread adoption of technical safeguards—like pre-registration, blind analysis, and transparent reporting—offers the most robust defense. For the fields of materials science and drug development, where the stakes of unreliable research are exceptionally high, embedding these practices into the core of the research workflow is not merely an ethical imperative but a fundamental requirement for scientific and technological progress.
Within materials science and drug development, research integrity is the foundation of scientific progress and societal trust. It is guided by a set of principles that ensure research is conducted with reliability and rigor. A breach of these principles can have a domino effect, potentially impacting patient care, medical interventions, and the successful implementation of healthcare policies [10]. The increasing concerns over reproducibility and questionable research practices underscore the critical need to systematically embed integrity checks throughout the experimental process. This whitepaper provides a technical guide for integrating these checks, fostering a culture that proactively ensures the validity and trustworthiness of scientific outputs.
Core Principles and Definitions
Research integrity extends beyond the mere avoidance of fabrication, falsification, and plagiarism. It encompasses a positive duty to adhere to a set of principles that ensure the robustness of the scientific record.
- Research Integrity: The practice of research in a way that ensures its reliability and rigor, serving as a pillar for societal trust and scientific advancement [10].
- Reproducibility: The ability of a research team or others to duplicate the results of a prior study using the same materials and procedures. Challenges in this area are a key indicator of integrity concerns [10].
- Questionable Research Practices (QRPs): Practices that violate the traditional norms of scientific research but do not necessarily amount to outright misconduct. Examples may include selective reporting of results, p-hacking, or inadequate data management [10].
Upholding these principles requires a framework supported by institutional guidelines, robust training, and mentorship, all of which are crucial for fostering a sustainable culture of integrity [10].
A Framework for Integrity Checks in the Research Workflow
Integrity checks should not be an afterthought but an integral, scheduled part of the research lifecycle. The following workflow provides a high-level overview of this integrated process, from initial planning to final data archiving.
Diagram 1: Integrity Check Workflow
This continuous cycle ensures that potential issues are identified and rectified early, preventing the propagation of errors and reinforcing the reliability of the research.
Quantitative Data Management and Presentation
Proper handling and presentation of quantitative data are fundamental to research integrity. Ineffective representations can mislead, while clear, honest graphs convey accurate information.
Data Summarization and Frequency Tables
Grouping quantitative data into class intervals is a critical first step for clear visualization, especially when dealing with a large number of widely varying data values. Defining intervals of equal size, typically between 5 and 20 classes, helps reveal underlying patterns without overwhelming detail [64].
Table: Frequency Table for Male Subject Weights
| Weight Interval (pounds) | Frequency |
|---|---|
| 120 – 134 | 4 |
| 135 – 149 | 14 |
| 150 – 164 | 16 |
| 165 – 179 | 28 |
| 180 – 194 | 12 |
| 195 – 209 | 8 |
| 210 – 224 | 7 |
| 225 – 239 | 6 |
| 240 – 254 | 2 |
| 255 – 269 | 3 |
Choosing the Correct Graph Type
The choice of graphical representation has a direct impact on the accurate interpretation of data.
- Histograms: Used for quantitative data where the horizontal axis is a number line. Unlike bar charts, histograms illustrate the distribution of continuous data, showing where values are concentrated [64].
- Comparative Bar Charts: Effective for comparing quantities between two groups, for example, by placing bars for an experimental group and a control group next to each other for direct visual comparison [64].
- Frequency Polygons: An alternative to histograms where a point is placed at the midpoint of each interval at a height equal to the frequency. Connecting these points with straight lines is particularly useful for emphasizing the distribution and comparing multiple datasets on the same graph [64].
Experimental Protocols and Methodologies
This section outlines detailed methodologies for key experiments, emphasizing the points where integrity checks must be incorporated.
Protocol for High-Throughput Material Synthesis and Characterization
Objective: To synthesize and characterize a library of novel alloy compositions and assess their electrochemical properties for battery electrode applications.
Materials and Reagents:
- Precursor Salts: High-purity (≥99.99%) metal chlorides and nitrates.
- Solvent: Anhydrous N-Methyl-2-pyrrolidone (NMP), stored over molecular sieves.
- Reducing Agent: Sodium borohydride (NaBH₄), freshly weighed in an inert atmosphere glovebox.
Integrity-Checked Procedure:
- Weighing (Check 1): Precisely weigh precursor salts using a calibrated microbalance. Integrity Check: A second researcher independently verifies and records all mass measurements.
- Synthesis: Dissolve precursors in NMP under argon. Add the reducing agent dropwise with vigorous stirring.
- Purification (Check 2): Centrifuge the product and wash three times with ethanol. Integrity Check: The supernatant from the final wash is tested for residual chloride ions; the test must be negative to proceed.
- Characterization: Analyze the material using XRD, SEM, and BET surface area analysis.
- Data Collection (Check 3): Perform cyclic voltammetry in a 3-electrode cell. Integrity Check: A standard reference material is tested concurrently to validate the instrument calibration. All raw data files are immediately backed up to a secure, version-controlled repository.
Data Visualization and Integrity Verification Workflow
The process of moving from raw data to a published figure must be transparent and verifiable. The following diagram details the steps and their associated integrity checks.
Diagram 2: Data Visualization Workflow
The Scientist's Toolkit: Essential Research Reagent Solutions
The following table details key reagents and materials used in materials science research, with an emphasis on how proper management of these resources underpins research integrity.
Table: Essential Materials for Materials Science Research
| Item | Function | Integrity Consideration |
|---|---|---|
| High-Purity Precursors | Source of elemental composition in synthesized materials. | Certificate of Analysis (CoA) must be archived. Batch-to-batch variability must be documented. |
| Calibrated Reference Materials | Validation of analytical instrument performance (e.g., SEM, XRD). | Regular calibration checks against certified standards are mandatory for data validity. |
| Stable Electrolyte Solutions | Medium for electrochemical testing of battery or fuel cell materials. | Storage conditions and expiration dates must be strictly adhered to; decomposition can invalidate results. |
| Annotated Electronic Lab Notebook (ELN) | Permanent record of procedures, observations, and data. | Must be date-stamped and use immutable entries to ensure an auditable trail and prevent data tampering. |
Technical Implementation of Integrity Checks
Automated Data Validation Scripts
Implementing automated checks at the point of data entry or analysis can flag anomalies. For instance, scripts can verify that measured values fall within physically possible ranges (e.g., a porosity percentage is between 0 and 100) or that control measurements match expected values.
Visualization and Color Contrast Standards
To ensure accessibility and accurate interpretation of graphical data, sufficient color contrast is critical. The WCAG 2.1 guidelines state that for normal text, the contrast ratio between foreground (e.g., text) and background should be at least 4.5:1, and for large-scale text, at least 3:1 [65]. For graphical elements in charts and diagrams, a high contrast ratio ensures that all viewers can distinguish the information.
A common technique for ensuring legibility, such as when placing text over a colored background in a bar chart, is to automatically choose the text color based on the brightness of the background. The W3C-recommended formula for perceived brightness is: ((Red * 299) + (Green * 587) + (Blue * 114)) / 1000 [66]. A resulting value greater than 125 suggests that black text would be appropriate, otherwise white text should be used [66]. This logic can be implemented in data visualization software (e.g., Python's prismatic::best_contrast or similar functions in R [67]) to dynamically ensure optimal contrast.
Integrating systematic integrity checks into every stage of the research workflow is not merely a defensive measure against misconduct; it is a proactive strategy to enhance the reliability, reproducibility, and overall impact of scientific research. By adopting the frameworks, protocols, and tools outlined in this guide, researchers in materials science and drug development can fortify their work against error and ambiguity, thereby accelerating genuine scientific progress and maintaining the vital trust of society.
Validating Research and Comparing Institutional Approaches
Benchmarking has evolved from a simple performance measurement tool into a sophisticated methodology driving quality improvement, strategic decision-making, and research integrity across academic and scientific institutions. In the specific context of materials science research, where advancements in artificial intelligence (AI) and computational methods are accelerating the pace of discovery, robust benchmarking practices are becoming increasingly critical for maintaining scientific validity and reproducibility. These practices enable researchers to navigate the complex landscape of emerging methodologies while safeguarding against new forms of academic misconduct that can arise from AI misuse [68]. For materials scientists and drug development professionals, implementing comprehensive benchmarking protocols ensures that research outcomes remain trustworthy, comparable, and ethically sound, even as analytical techniques grow more computationally complex.
The current academic environment, with its heavy emphasis on publication metrics, generates pressures that can potentially compromise research integrity [69]. Properly designed benchmarking frameworks serve as a counterbalance to these pressures by establishing objective performance standards that prioritize methodological rigor over mere output volume. As materials science increasingly intersects with AI capabilities, the development of domain-specific benchmarks—such as those evaluating large language models on graduate-level materials science reasoning—represents a proactive response to the unique challenges posed by technological advancement [70]. This whitepaper examines how leading universities and publishers are implementing benchmarking best practices to uphold research quality while fostering innovation in materials science and related disciplines.
Benchmarking Methodologies: Frameworks for Excellence
Typology of Benchmarking Approaches
Institutional benchmarking practices generally fall into two primary categories, each with distinct applications and advantages. Metrics benchmarking focuses on quantitative performance indicators and is particularly valuable for diagnosing strengths and weaknesses within departments or research programs. However, this approach has inherent limitations—while it excels at identifying performance gaps, it typically does not provide prescriptions for improvement. In contrast, best practice benchmarking specifically investigates the processes and strategies that enable top-performing entities to achieve their results, offering actionable pathways for enhancement [71].
The most effective benchmarking initiatives combine both approaches, creating a comprehensive evaluation framework that not only measures performance but also illuminates the methods for its improvement. For research integrity specifically, benchmarking can be further categorized based on focus area: procedural benchmarking examines research conduct and methodology; output benchmarking assesses publication quality and impact; and ethical benchmarking evaluates institutional safeguards against misconduct [68]. This multifaceted approach is particularly relevant in materials science, where research spans theoretical, computational, and experimental domains, each requiring distinct evaluation criteria.
Implementation Framework for Research Benchmarking
Successful benchmarking implementation follows a structured methodology that maintains scientific rigor while remaining adaptable to specific research contexts. The following workflow outlines key stages in developing a comprehensive benchmarking program for materials science research:
Figure 1: Research Benchmarking Implementation Workflow
The benchmarking process begins with a meticulous planning phase where objectives are clearly defined and metrics aligned with strategic goals. For materials science research, this typically involves selecting both general research quality indicators and field-specific measurements. The data collection phase employs multiple methodologies to ensure comprehensive coverage, including quantitative performance tracking, process documentation, and expert consultation. Importantly, the process is cyclical rather than linear, with regular review periods enabling continuous refinement of benchmarks based on evolving research priorities and ethical considerations [72] [71].
University Benchmarking Initiatives: Current Landscape and Best Practices
Structural and Operational Benchmarking in Higher Education
Leading universities are implementing sophisticated benchmarking practices across multiple operational domains, with particular emphasis on online education, research administration, and career services. The 2025 UPCEA Benchmarking Online Enterprises Study reveals that institutions are increasingly using key performance indicators (KPIs) to guide strategic decisions, with metrics encompassing budgets, staffing ratios, technology integration, and student outcomes [73]. These benchmarks help academic leaders identify effective practices while maintaining financial sustainability in competitive educational markets.
The North Carolina Benchmarking Project exemplifies long-term commitment to comparative performance assessment, having provided operational benchmarks for local governments and educational institutions for over 25 years [71]. Similarly, UNESCO's guidelines for open universities promote benchmarking as a methodology for quality assessment and improvement, emphasizing the development of a "quality culture" that extends beyond basic compliance requirements [72]. These initiatives demonstrate how structured benchmarking creates frameworks for continuous improvement rather than simply serving as periodic evaluation exercises.
Domain-Specific Benchmarking in Materials Science
In materials science specifically, benchmarking efforts have evolved to address the field's unique methodological challenges. The MSQA benchmark represents a particularly advanced approach, evaluating large language models on graduate-level materials science reasoning through 1,757 questions across seven sub-fields, including structure-property relationships, synthesis processes, and computational modeling [70]. This initiative addresses a critical gap in domain-specific assessment by testing both factual knowledge and complex multi-step reasoning abilities essential for advanced materials research.
Table 1: Performance Metrics of LLMs on MSQA Materials Science Benchmark
| Model Type | Representative Models | Accuracy (%) | Strengths | Limitations |
|---|---|---|---|---|
| Proprietary API-based | GPT-4, Gemini-2.0-Pro | Up to 84.5% | Strong reasoning capabilities, better handling of complex questions | Limited transparency, potential data privacy concerns |
| Open-source | Various community models | Up to 60.5% | Greater transparency, customization options | Lower performance on complex reasoning tasks |
| Domain-specific fine-tuned | Materials science specialized models | Variable, often underperforms | Domain-aware terminology | Overfitting, distributional shift issues |
The benchmarking results reveal significant performance variations between model types, with proprietary models generally outperforming open-source alternatives on complex reasoning tasks. However, the research indicates that retrieval augmentation—enhancing models with relevant contextual data—significantly improves performance across all categories, suggesting an important strategy for practical implementation [70]. These findings have profound implications for materials science research, where AI assistance is increasingly employed for literature analysis, experimental design, and data interpretation.
Publisher-Led Initiatives: Safeguarding Research Integrity
Evolving Roles in Research Integrity Assurance
Academic publishers are increasingly recognizing their responsibility in safeguarding research integrity through enhanced vetting processes, both pre- and post-publication. This evolving role reflects concerns about emerging forms of misconduct, particularly those facilitated by AI technologies. As noted in recent literature, "Investment in tools and training is a critical measure in addressing the concerns, but enhanced collaboration between cross-industry stakeholders is also necessary" [74]. This collaborative approach is essential for addressing integrity challenges that transcend institutional boundaries, especially in interdisciplinary fields like materials science.
The Asian Council of Science Editors' survey of 720 researchers globally revealed that 38% of respondents felt pressured to compromise research integrity due to publication demands, while 40% reported awareness of data fabrication or falsification [69]. These findings highlight the critical need for robust benchmarking of research quality and integrity measures. Publishers are responding by implementing more sophisticated screening tools, establishing clearer ethical guidelines for AI use in research, and developing frameworks for consistent handling of integrity concerns across different publications and disciplines.
Addressing AI-Specific Integrity Challenges
The integration of AI in research processes has introduced novel integrity challenges that require specialized benchmarking approaches. These include data fabrication through AI-generated datasets, text plagiarism via automated content generation, and opacity in AI-assisted methodologies [68]. In response, forward-looking publishers are developing AI-specific benchmarking protocols that address these emerging concerns while recognizing AI's potential to enhance research efficiency when properly implemented.
Table 2: Taxonomy of AI-Related Academic Misconduct in Research
| Misconduct Type | Description | Common Motivations | Detection Challenges |
|---|---|---|---|
| Data fabrication using AI | Generation of realistic but fictitious datasets using AI algorithms | Publication pressure, pursuit of prestige | Sophisticated outputs difficult to distinguish from genuine data |
| AI-assisted plagiarism | Use of AI to generate "pseudo-original" content by rephrasing existing literature | Shortening research cycles, increasing output quantity | Evades traditional plagiarism detection tools |
| Lack of AI methodology disclosure | Failure to adequately document AI's role in research processes | Protecting competitive advantage, technological secrecy | Difficult to assess impact on results without full disclosure |
| Inappropriate application of AI models | Use of AI tools without sufficient understanding of limitations | Rapid results, reducing analytical burden | Requires domain expertise to identify misapplications |
A critical development in publisher responses is the emphasis on transparency benchmarking—evaluating whether research adequately discloses the extent and nature of AI tool usage. This includes requirements for detailed methodological descriptions of AI implementation, data processing procedures, and algorithm decision-making processes [68]. For materials science research, where AI is increasingly employed for materials discovery, characterization, and simulation, these transparency standards help maintain reproducibility and scientific rigor despite the "black box" nature of some advanced algorithms.
Experimental Protocols for Benchmarking Studies
Methodological Framework for Research Quality Assessment
Implementing effective benchmarking in materials science requires rigorous experimental protocols that ensure valid, comparable results. The MSQA benchmark development process offers an exemplary methodology, employing a three-stage quality assurance process: (1) regular expression-based filtering, (2) LLM-driven refinement, and (3) expert annotation [70]. This multi-layered approach balances efficiency with methodological rigor, particularly important when benchmarking complex research capabilities.
For materials science research integrity specifically, benchmarking protocols should incorporate both process metrics (evaluating research conduct) and output metrics (assessing research quality). Process metrics might include documentation completeness, methodological transparency, and data sharing practices, while output metrics typically encompass publication quality, reproducibility, and citation impact. The integration of both categories provides a more comprehensive assessment than either approach alone, reflecting the multifaceted nature of research integrity.
Table 3: Research Reagent Solutions for Benchmarking Studies
| Tool/Resource | Function | Application in Benchmarking |
|---|---|---|
| Sentence Transformers | Generate embeddings for document similarity analysis | Clustering research publications for diversity assessment in benchmark development |
| Chemistry Paper Parser | Extract and preserve complex scientific notation from publications | Maintain integrity of materials science concepts and formulas during data processing |
| Regular Expression Filters | Identify and flag potentially problematic content patterns | Initial screening for data quality issues in benchmark datasets |
| K-means Clustering | Group similar items based on feature similarity | Ensure representative diversity in benchmark content selection |
| Expert Annotation Platforms | Facilitate domain expert evaluation of content quality | Validate benchmark questions and answers for accuracy and relevance |
| Retrieval-Augmented Generation Frameworks | Enhance AI models with external knowledge sources | Improve benchmark performance by providing contextual materials science knowledge |
The tools and methodologies outlined in Table 3 represent essential components for implementing robust benchmarking protocols in materials science research. These "research reagents" enable the development of domain-specific benchmarks that accurately reflect the field's complexity while maintaining methodological rigor. Particularly important is the inclusion of specialized tools for handling materials science nomenclature and concepts, such as chemistry-aware text parsers that preserve the integrity of complex formulas and relationships [70].
Implementation Roadmap: Integrating Benchmarking into Research Ecosystems
Strategic Integration Pathways
Successful benchmarking implementation requires careful planning and cross-functional collaboration. Based on successful initiatives across universities and publishers, the most effective approaches include phased implementation that allows for iterative refinement, stakeholder engagement at multiple organizational levels, and alignment with existing quality assurance processes rather than creating parallel systems [72] [73]. For materials science departments specifically, integration might begin with benchmarking computational research methods before expanding to experimental techniques, allowing lessons learned from more standardized domains to inform more complex applications.
The UPCEA benchmarking study identifies several key success factors, including "interrogating financial models, benchmarking for efficiency not just scale, developing a clear AI strategy, aligning staffing with strategy, and investing in organizational clarity" [73]. These principles apply equally to research benchmarking, where strategic alignment ensures that benchmarking activities directly support broader research integrity goals rather than becoming perfunctory compliance exercises.
Measuring Impact and Continuous Improvement
Effective benchmarking initiatives include mechanisms for evaluating their own impact and identifying improvement opportunities. The UNESCO benchmarking guidelines emphasize that benchmarking "should be considered an opportunity for improvement and a starting point for reviewing and enhancing processes, not as an end in itself" [72]. This philosophy requires regular assessment of how benchmarking data informs decision-making, enhances research quality, and addresses integrity challenges.
For materials science research, impact measurement might track changes in reproducibility rates, methodological transparency in publications, or adoption of best practices identified through benchmarking activities. Critically, these impact assessments should themselves be subject to benchmarking, creating a cycle of continuous refinement that maintains relevance as research methodologies evolve. This approach is particularly important given the rapid advancement of AI tools in materials science, where benchmarking frameworks must regularly adapt to address emerging capabilities and associated integrity considerations [68].
Benchmarking practices in universities and publishing are evolving from simple performance measurement to comprehensive frameworks that address research quality, integrity, and innovation simultaneously. For materials science researchers, this evolution offers powerful methodologies for navigating an increasingly complex research landscape while maintaining the ethical standards essential to scientific progress. The integration of domain-specific benchmarks—such as those evaluating AI capabilities in materials science reasoning—represents a particularly promising development, addressing field-specific challenges while contributing to broader research integrity goals.
As benchmarking practices mature, their potential extends beyond quality assurance to become enabling structures that support accelerated discovery and innovation. Properly implemented benchmarking creates environments where methodological rigor and ethical standards provide foundations for creative exploration rather than constraints. For materials science researchers and drug development professionals, embracing these evolving benchmarking approaches offers a pathway to maintaining research integrity while fully leveraging the unprecedented analytical capabilities offered by advanced computational methods, including AI. In this context, benchmarking transforms from an administrative requirement to a fundamental component of exemplary scientific practice in the 21st century.
In the demanding field of materials science and drug development, where research findings form the basis for critical decisions, research integrity is paramount. Electronic Research Administration (eRA) systems are comprehensive software platforms that digitize and manage the entire lifecycle of sponsored research projects. For scientists and researchers, these systems are not merely administrative tools; they are a foundational component of a modern, rigorous, and ethical research enterprise. A robust eRA system ensures that the complex workflow from proposal development to grant management, protocol oversight, and reporting is conducted with the highest standards of scientific integrity—defined as adherence to professional practices, ethical behavior, and the principles of honesty and objectivity [75]. By enforcing consistent procedures, creating transparent audit trails, and safeguarding sensitive data, eRA systems provide the structural framework necessary to uphold these standards, thereby strengthening the validity and reliability of research outcomes in materials science.
The Core Functions of an eRA System
An eRA system integrates and streamlines a multitude of research administration tasks. Understanding its core functions is key to appreciating its role in ensuring compliance and oversight. The following diagram illustrates the typical workflow and major components of an eRA system.
Pre-Award Management
This initial phase involves the preparation and submission of research proposals. The eRA system guides researchers through institutional approvals, ensures all required components are complete, and facilitates electronic submission to funding agencies. This creates a formal, documented starting point for the research project.
Post-Award Compliance and Protocol Management
Once a grant is awarded, the eRA system becomes central to managing compliance. It helps ensure adherence to the specific terms and conditions of the award. A critical function is the formalization of the experimental protocol within the system. Documenting the methodology, materials, and procedures in the eRA establishes a "single source of truth" that is time-stamped and version-controlled, preventing deviation and promoting reproducibility.
Data Management and Integrity
The eRA system often integrates with or provides a framework for data management. While raw experimental data may reside in specialized systems, the eRA catalogs data outputs, links them to the approved protocol, and manages access. This creates a clear chain of custody for research data, which is a cornerstone of research integrity and a requirement under evolving research misconduct regulations [76].
Reporting and Audit Trails
Automated reporting is a vital function. eRA systems can generate progress and financial reports for funders, ensuring timely and accurate disclosure. Most importantly, every action within the eRA—from protocol modifications to data access—is logged in an immutable audit trail. This provides a complete history for internal reviews or external audits, demonstrating rigorous oversight.
The Regulatory and Policy Landscape for 2025-2026
The compliance environment is rapidly evolving. Researchers and administrators must be aware of new and updated regulations that directly impact how research must be conducted and administered.
Table 1: Key Regulatory Changes Impacting Research Administration
| Regulation / Policy | Issuing Agency | Key Focus | Compliance Date / Status |
|---|---|---|---|
| Final Rule on Research Misconduct [76] | HHS Office of Research Integrity (ORI) | Procedures for addressing research misconduct allegations; institutional flexibility with organized documentation. | Effective January 1, 2026 for allegations received on or after this date. |
| CMS Interoperability Framework [77] [78] | Centers for Medicare & Medicaid Services (CMS) | Voluntary standards for seamless, secure health data exchange using FHIR APIs. | Early adopter goals set for July 4, 2026. |
| Updated HIPAA Security Rule [79] | U.S. Department of Health & Human Services | Making encryption of electronic protected health information a mandatory requirement. | Proposed for 2025; final rule pending. |
| NIST Post-Quantum Cryptography (PQC) [79] | National Institute of Standards and Technology | Transitioning encryption standards to be resistant to future quantum computer attacks. | Phasing out RSA/ECC by 2030; planning should begin now. |
A significant change is the updated Research Misconduct Regulations (42 C.F.R. part 93). The new rules, which take full effect in January 2026, provide institutions with greater flexibility but also emphasize the need for meticulous documentation throughout misconduct proceedings [76]. An eRA system is instrumental in meeting these demands by automatically maintaining the required records, such as protocol versions, data access logs, and authorship confirmations.
Furthermore, the push for data interoperability, exemplified by the CMS Interoperability Framework and the widespread adoption of FHIR (Fast Healthcare Interoperability Resources) standards, is critical for collaborative materials science and clinical research [77] [78]. eRA systems that support these modern API-based standards enable secure and efficient data sharing between unaffiliated systems, breaking down silos and accelerating discovery while maintaining compliance.
Implementing eRA for Enhanced Oversight: A Practical Guide
Core Compliance Workflow
To visualize how an eRA system actively enforces compliance, the following diagram traces the pathway of a research protocol from inception through to potential audit, highlighting key oversight checkpoints.
The Researcher's Toolkit: Essential Components for Compliance
For a materials scientist or drug development professional, certain tools and concepts are non-negotiable for maintaining integrity and compliance within an eRA framework.
Table 2: Essential Research Reagent Solutions for Compliance and Integrity
| Tool / Solution | Primary Function | Role in Research Integrity & Compliance |
|---|---|---|
| Electronic Lab Notebook (ELN) | Digital record of experiments, procedures, and raw data. | Serves as the primary, timestamped record of research activities, crucial for reproducibility and defending against misconduct allegations [76]. |
| FHIR-Compatible API [77] [78] | Standardized interface for exchanging healthcare and research data. | Enables seamless, secure integration of clinical or patient-derived data into the research workflow, ensuring compliance with interoperability mandates. |
| Continuity of Care Document (CCD) [77] | Standardized summary of clinical patient information. | Provides a consistent, human- and machine-readable format for clinical data used in research, reducing errors and misinterpretation. |
| Encryption & Key Management [79] | Securing data at rest and in transit using cryptographic algorithms. | Protects sensitive research data from breaches. Encryption is increasingly a mandatory compliance requirement under HIPAA and other regulations [79]. |
| Controlled Vocabularies (e.g., SNOMED CT) | Standardized terms for diseases, findings, and procedures. | Ensures semantic consistency across datasets, enabling valid aggregation, analysis, and AI deployment, which is a key challenge in interoperability [78]. |
Experimental Protocol for a Compliance-Driven Workflow
This methodology outlines the steps for conducting research within an eRA-supervised environment to maximize integrity and meet regulatory expectations.
- Objective: To execute a materials science research project with full traceability, from approved protocol to reported result, ensuring compliance with institutional and funding agency policies.
Background: New research misconduct regulations (42 C.F.R. § 93.106) emphasize institutional flexibility but also the necessity of organized documentation and confidentiality management during any inquiry [76]. A well-documented process in an eRA system is the best defense.
Step 1: Protocol Finalization and Submission. The research team finalizes the study protocol, including detailed methodologies, materials specifications (e.g., polymer sources, nanoparticle synthesis methods), and data collection plans. This document is submitted for review within the eRA system.
- Step 2: Institutional Review and Approval. The protocol undergoes review by the relevant committees (e.g., IACUC for animal research, Institutional Biosafety Committee). The eRA system tracks review progress, records approval, and links the approval to the protocol.
- Step 3: Protocol Lock-in and Version Control. Upon approval, the protocol is "locked" as version 1.0 in the eRA. Any subsequent amendments must follow a formal change control process within the system, creating a new version and preserving the original. This practice aligns with the need for meticulous record-keeping as outlined in the updated misconduct regulations [76].
- Step 4: Data Generation with Provenance. All experimental data generated must be recorded in an ELN integrated with the eRA. The system should automatically capture metadata (e.g., timestamp, user ID, instrument calibration logs) to establish data provenance.
- Step 5: Data Analysis and Reporting. Data analysis is performed, and results are compiled into reports or manuscripts. The eRA system should link the final outputs (e.g., draft manuscripts, published papers) directly back to the approved protocol and the underlying source data.
- Step 6: Audit Trail Generation. Throughout this process, the eRA system automatically maintains an immutable audit trail, logging every action from protocol modification to data access. This trail is the definitive record for demonstrating compliance during internal or external audits.
For the modern materials scientist or drug developer, Electronic Research Administration is far more than a grants management portal. It is the central nervous system for research integrity, providing the structure and documentation needed to navigate an increasingly complex regulatory landscape. By formally integrating experimental protocols, enforcing data security standards like encryption, facilitating interoperable data exchange via FHIR, and generating comprehensive audit trails, eRA systems empower researchers to conduct their work with the highest degree of rigor and transparency. As policies continue to evolve, a strategic investment in and mastery of the eRA ecosystem is not just a best practice for compliance—it is a fundamental requirement for producing trustworthy, impactful science.
The Role of Continuous Literature Review in Validating Research Gaps and Directions
This whitepaper examines the critical function of continuous literature review in upholding research integrity within materials science and engineering. Moving beyond the traditional view of literature review as a mere initial step, we articulate a framework where it serves as an ongoing process that validates research gaps, ensures methodological rigor, and fortifies the credibility of scientific directions. By integrating principles of responsible research conduct with practical, data-driven methodologies for gap analysis, this guide provides researchers with a structured approach to navigating the modern research landscape, thereby fostering a culture of integrity and reliability in scientific innovation.
Research integrity, defined by adherence to principles of Rigor, Reproducibility, and Responsibility (the 3R’s), forms the bedrock of credible scientific inquiry [80]. In the field of materials science and engineering—a discipline pivotal to technological progress—any compromise in integrity can have a domino effect, impacting everything from experimental validity to the application of new materials in critical technologies [10] [81]. The materials science community has historically relied on implicit models of the research process, often passed down through mentorship, leading to varied experiences and standards among researchers [81]. An explicit, shared model of the research cycle is therefore indispensable for training novice researchers, establishing common expectations, and ensuring the robust development of new knowledge [81].
Central to this research cycle is the practice of continuous literature review. Traditionally viewed as a preliminary step, a modern understanding reframes it as a persistent activity that spans the entire research lifecycle. This ongoing process is vital for:
- Validating Research Gaps: Ensuring that proposed research directions address genuine, evidence-based gaps in the community's knowledge.
- Ensuring Methodological Soundness: Allowing researchers to continuously align their methods with the state-of-the-art.
- Preventing Redundancy and Misconduct: Mitigating the risks of "re-inventing the wheel" and unintentional questionable research practices [80] [68]. This paper provides a technical guide for implementing a continuous literature review process, thereby strengthening research integrity from the ground up.
The Continuous Research Cycle in Materials Science
The research process in materials science and engineering is best conceptualized as a cycle, where literature review is not a one-time task but an integral, repeating component of each phase [81]. This cycle systematically transforms a perceived knowledge gap into a validated community contribution.
The following diagram illustrates this iterative process, highlighting how literature review is embedded at every stage to maintain direction and integrity.
Figure 1: The Materials Science Research Cycle with Continuous Literature Review. The yellow nodes highlight the critical, ongoing role of literature review in informing each stage of research (red) and contributing to new knowledge (green).
As depicted in Figure 1, the cycle begins with a literature review to identify a meaningful gap, which is refined into a research question using frameworks like the Heilmeier Catechism [81]. The literature review continues to inform methodological design, data analysis, and the communication of results, ensuring the research remains relevant and grounded in established knowledge. The publication of results then feeds back into the community's knowledge, restarting the cycle.
A Framework for Continuous Literature Review
A continuous literature review is guided by core principles of responsible science communication: Objectivity, Honesty, Openness, and Accountability [80]. These principles translate into a practical, multi-stage process for conducting the review itself.
The Process of a Continuous Review
The workflow for a continuous literature review can be broken down into six key steps [82]:
- Define Your Research Question: Formulate a clear, focused, and answerable question.
- Search Relevant Sources: Use academic databases, journals, and patent libraries to gather literature.
- Document References: Use citation management software to systematically record all relevant sources.
- Evaluate & Analyze Literature: Critically assess the quality, methodology, and findings of each source.
- Organize & Synthesize: Structure the information to identify overarching themes, conflicts, and gaps.
- Publish Your Results (Recommended): Share your synthesized review to contribute to the community's knowledge base [83].
This process is not linear; as new research is published, the cycle from steps 2 through 5 repeats, ensuring the researcher's understanding remains current.
Quantitative and Qualitative Analysis in Literature Review
A robust literature review employs both quantitative and qualitative analysis methods to derive meaningful insights.
Quantitative Analysis Methods involve using statistics to understand patterns in the collected literature or data reported in studies. This can include:
- Descriptive Analysis: Summarizing trends, such as the number of publications per year on a topic or the average reported performance of a class of materials.
- Meta-analysis: Statistically combining results from multiple independent studies to arrive at a composite conclusion [83].
Qualitative Analysis Methods are used to interpret conceptual content and thematic developments:
- Thematic Analysis: Identifying and analyzing recurring themes or concepts across different studies.
- Content Analysis: Systematically categorizing text from publications to identify focus areas [84].
- Gap Analysis through Causal Mapping: A powerful technique for visualizing the logical structure of existing knowledge to pinpoint where connections are missing [85].
Validating Research Gaps through Structured Gap Analysis
The core purpose of a continuous literature review is to move from a superficial "what's missing" to a validated, structured research gap. Gap analysis through causal mapping provides a rigorous methodology for this.
The Causal Mapping Methodology
A causal map is a visual representation of the theories and relationships found in the existing literature [85]. It depicts key concepts as nodes and causal influences as arrows. Constructing such a map involves:
- Extracting Key Concepts: Identify the main variables, factors, and outcomes from the literature.
- Drawing Causal Links: For each study, map the proposed causal relationships between these concepts.
- Tagging with Evidence: Briefly note the type of data or reference that supports each causal arrow.
Identifying and Classifying Gaps
Once a causal map of current knowledge is built, gaps become visually apparent. These can be systematically classified into three types [85]:
- Logic/Structure Gaps: Places where two concepts are NOT connected by a causal arrow. The most significant structural gaps exist around concepts with only one or no incoming arrows.
- Data/Evidence Gaps: Instances where a causal link is proposed but the supporting evidence is weak, absent, or based on a limited type of study.
- Relevance/Meaning Gaps: Situations where the existing research lacks perspectives from key stakeholder groups (e.g., industrial partners, specific academic disciplines).
The diagram below illustrates how these gaps can be identified within a causal map.
Figure 2: Visualizing Research Gaps in a Causal Map. Green nodes are well-connected, while yellow nodes have significant structural gaps (red dashed lines). Data/evidence gaps are also highlighted, showing where support for a relationship is weak.
Gap Analysis in Action: A Materials Science Example
Consider a researcher investigating the "impact of cooling rate (A) on tensile strength (B) in a new aluminum alloy." A causal map of the literature might show a strong, well-evidenced arrow from A to B. However, a gap analysis could reveal:
- Structural Gap: No connection from "alloying element segregation (E)" to "tensile strength (B)," suggesting a potential second causal factor.
- Data Gap: The A->B link is supported only by computational models, lacking robust experimental data.
- Relevance Gap: All studies are from academia, with no input from industrial casting facilities.
This structured analysis validates the research gap and provides clear, actionable directions for new research.
Quantitative Frameworks for Literature Analysis
Integrating quantitative data analysis into the literature review process adds a layer of objectivity, helping to confirm trends and patterns suspected from qualitative reading.
Fundamentals of Quantitative Data Analysis from Literature
When extracting numerical data from published studies, understanding basic statistical measures is crucial for accurate interpretation. The table below summarizes key descriptive statistics commonly encountered.
Table 1: Key Descriptive Statistics for Analyzing Quantitative Data from Literature
| Statistical Measure | Description | Role in Literature Analysis |
|---|---|---|
| Mean | The mathematical average of a set of values. | Provides a central tendency for reported data (e.g., average reported strength). |
| Median | The midpoint in a range of numerically ordered values. | Offers a better measure of central tendency when data is skewed by outliers. |
| Mode | The most frequently occurring value in a data set. | Identifies the most common outcome or value reported across studies. |
| Standard Deviation | A metric indicating how dispersed a range of numbers is around the mean. | Helps assess the consistency and reliability of reported results across different studies. A high standard deviation indicates high variability. |
| Skewness | Indicates how symmetrical a data distribution is. | Helps identify if the literature reports a balanced set of results or if findings are biased towards very high or very low values. |
Advanced Quantitative Methods
Beyond descriptive statistics, more advanced inferential methods can be applied to synthesized literature data:
- Regression Analysis: Used to understand and quantify the relationship between variables reported across multiple studies (e.g., how annealing temperature correlates with hardness across 20 different papers) [84].
- Time Series Analysis: Helps track the evolution of a key metric (e.g., solar cell efficiency) in the literature over time, identifying progress trends and performance plateaus [84].
Maintaining a continuous literature review and upholding research integrity requires a set of conceptual and practical tools. The following table details key resources and their functions in the research process.
Table 2: Essential "Research Reagent Solutions" for Validating Research Directions
| Tool / Resource | Category | Primary Function in Research |
|---|---|---|
| Heilmeier Catechism | Conceptual Framework | A series of questions (e.g., "What are you trying to do? Who cares?") used to rigorously evaluate and articulate the value and risks of a proposed research direction [81]. |
| Causal Map | Analytical Tool | A visual diagram that makes the logical structure of existing knowledge explicit, enabling the systematic identification of research gaps [85]. |
| Citation Manager | Software Tool | Software (e.g., Zotero, Mendeley) used to systematically collect, manage, and cite references throughout the research cycle [82]. |
| Systematic Review Protocol | Methodology | A pre-defined, rigorous plan for identifying, evaluating, and synthesizing all relevant literature on a specific question, minimizing bias [83]. |
| Meta-analysis | Statistical Tool | A quantitative data analysis method that combines results from multiple independent studies to produce a more precise and reliable estimate of an effect [83]. |
| AI Ethics Checklist | Governance Tool | A guideline to ensure transparent disclosure and responsible use of AI tools in research, mitigating risks of opacity and misconduct [68]. |
In an era marked by rapidly evolving scientific evidence and the emergence of new challenges like AI-generated content, the role of continuous literature review as a guardian of research integrity is more critical than ever [80] [68]. For the materials science community and related fields, adopting the structured, ongoing process outlined in this guide is not merely an academic exercise. It is a fundamental practice that ensures research is directed toward genuine gaps, built upon a foundation of rigorous methodology, and communicated with honesty and accountability. By integrating continuous literature review into the very fabric of the research cycle, scientists and researchers can fortify the integrity of their work, enhance its impact, and steadfastly uphold society's trust in science.
The field of materials science research, which is fundamental to advancements in drug development and nanotechnology, faces a growing threat to its credibility: the erosion of research integrity. With over 2.5 million scientific manuscripts published annually, studies indicate that 20-35% are flagged for image-related problems, and hundreds of thousands of papers are published each year with such issues [31]. The damage caused by a single post-publication retraction—including investigations and legal costs—is estimated at over $1 million per article [31]. For researchers, scientists, and drug development professionals, maintaining the highest standards of integrity has shifted from a compliance obligation to an existential necessity for securing funding and public trust [35]. This whitepaper provides a comparative analysis of leading research integrity tools—Proofig, imageTwin, iThenticate, and broader ecosystem initiatives—framed within a practical methodology to strengthen integrity protocols in materials science research.
Tool-Specific Capabilities and Quantitative Comparison
Core Functional Capabilities
- Proofig AI: This AI-powered platform specializes in automated image proofing. Its capabilities include detecting image duplication (including scaling, rotation, and flipping), manipulation within single sub-images (cloning, editing, splicing), and plagiarism by checking against a database of tens of millions of images from PubMed. A key differentiator is its dedicated detection of AI-generated images, specifically for microscopy, Western blots, and gels [31] [34]. It is trusted by major publishers and institutions and can process entire papers in minutes [31] [36].
- Imagetwin: This AI tool also focuses on image integrity, detecting duplication, manipulation, plagiarism, and AI-generated content. It leverages a vast database of over 100 million published figures for plagiarism checking and provides users with confidence scores for each analysis. It is used by some of the world's largest academic publishers and integrates with existing peer-review workflows [88].
- iThenticate: A cornerstone for text integrity, this software screens for textual plagiarism and similarity. It compares submissions against millions of full-text research articles, preprints, and conference proceedings to generate similarity reports and scores, helping to identify direct plagiarism, duplicate publication, and text recycling [39].
- STM Integrity Hub: This initiative represents a broader, modular platform designed to act as an early warning system. It allows publishers to integrate a wide range of specific screening tools to identify manuscripts that violate research integrity norms before they proceed further in the publication cycle [40].
- Access Integrity Research Tools: This suite provides a different type of integrity tool, focusing on semantic and nomenclature integrity. It offers APIs to provide scientifically accurate, consensus-agreed names for entities like medicinal plants (via the Medical Plant Names Service), human genes (TaxoGene), and to flag the use of known contaminated biological cell lines, preventing research based on faulty data [89].
Performance Metrics and Accuracy Data
Table 1: Quantitative Performance Metrics of Research Integrity Tools
| Tool | Primary Focus | Database Scale | Reported Accuracy / Performance Metrics | Key Strengths |
|---|---|---|---|---|
| Proofig AI | Image Integrity | Tens of millions of PubMed images [31] | AI-Generated Image Detection: 95.41% True Positives, 0.0093% False Positives (Microscopy) [34]Western Blot Analysis: 97.68% True Positives, 0.002% False Positives [34] | Specialized detection for FACS images & AI-generated content; high accuracy in life science image types |
| Imagetwin | Image Integrity | Over 100 million published figures [88] | Information Not Specified in Search Results | Extensive published figure database; confidence scores for analysis; forensic toolbox for manual checks |
| iThenticate | Text Integrity | Millions of full-text documents (articles, preprints, proceedings) [39] | Information Not Specified in Search Results | Industry standard for text similarity; configurable exclusion criteria (e.g., quotes, preprints) |
| Access Integrity | Nomenclature & Data Quality | 34,000+ Medicinal Plants; 22,300+ Human Genes; 1,245+ Bad Cell Lines [89] | 16.7 synonyms per plant entry; 19 synonyms per gene name on average [89] | Prevents research on contaminated cell lines; ensures consistent terminology for precise communication |
Detailed Methodologies and Experimental Protocols
Image Integrity Screening Protocol
The detection of image integrity issues is a multi-stage, AI-driven process. For tools like Proofig and imageTwin, the workflow is automated but follows a consistent forensic methodology.
- Step 1: Image Segmentation and Pre-processing. The software first decomposes all figures within a submitted manuscript (PDF or image files) into individual sub-images or panels. This step involves standardizing image properties to normalize for subsequent analysis [31].
- Step 2: Feature Extraction and Digital Fingerprinting. Advanced algorithms analyze each sub-image to create a unique digital fingerprint. This fingerprint is robust against common alterations like rotation, flipping, scaling, and minor color adjustments, allowing the tool to identify duplicates despite these transformations [31] [88].
- Step 3: Comparative Analysis. The extracted features are used in a multi-pronged detection process:
- Internal Duplication Check: The tool compares all sub-images within the manuscript against each other to find reuse, even when modified [31].
- External Plagiarism Check: The digital fingerprints are queried against a massive database of published figures (e.g., PubMed's tens of millions or imageTwin's 100 million) to identify potential plagiarism from the existing literature [31] [88].
- Manipulation Detection: Algorithms scan for signs of inappropriate editing, such as copy-move forgery (cloning), splicing, or deletion of image elements [31] [88].
- AI-Generated Image Detection: Proprietary AI models, trained on known real and synthetic images, analyze visual patterns to flag content likely generated by models such as those creating fake microscopy or Western blots [34]. Proofig, for instance, tests its models on proprietary datasets and over 250,000 published research images for validation [34].
- Step 4: Report Generation. The software compiles all potential findings into a comprehensive report, highlighting suspect images and providing tools for manual verification by a human expert, such as side-by-side comparisons and forensic filters [31] [88].
Text Similarity Screening Protocol
The protocol for screening textual plagiarism, as implemented by iThenticate and Similarity Check, is a critical first line of defense.
- Step 1: Document Submission and Text Extraction. The manuscript text is extracted, excluding elements like references and quotes if configured to do so [39].
- Step 2: Database Query and Pattern Matching. The extracted text is disaggregated into smaller chunks and compared against a massive database of scholarly content. The software uses complex pattern-matching algorithms to identify verbatim or nearly verbatim text, as well as paraphrased content [39].
- Step 3: Similarity Report Generation. The tool generates a detailed report comprising:
- An Overall Similarity Score, which is a cumulative percentage of the manuscript's text that overlaps with one or more published works.
- A color-coded document viewer that highlights overlapping text and links directly to the suspected source(s) [39].
- Step 4: Human Interpretation and Investigation. This is the most critical step. An editor with subject-matter expertise reviews the report. They must determine if the overlaps constitute a serious breach of ethics (e.g., direct, unattributed copying of another's work) or are acceptable (e.g., a properly quoted and cited methods section, or text from a preprint authored by the same team). A high similarity score does not automatically mean plagiarism, and a low score does not guarantee originality [39].
Diagram: Text Similarity Screening and Investigation Workflow
Integrated Workflows for a Multi-Layered Defense
No single tool can address all integrity threats. A robust defense requires an integrated workflow that combines textual, image-based, and data-level checks. The following diagram illustrates how these tools can be orchestrated within a research institution or publisher's workflow to create a comprehensive integrity shield.
Diagram: Multi-Layered Research Integrity Screening
The Scientist's Toolkit: Essential Research Reagent Solutions
For materials scientists and drug development professionals, ensuring integrity goes beyond the written manuscript to the foundational reagents and materials used in research. The following table details key solutions for maintaining integrity at the experimental level.
Table 2: Essential Research Reagent Solutions for Integrity
| Reagent / Material | Function | Integrity Application & Rationale |
|---|---|---|
| Authenticated Cell Lines | Fundamental units for in vitro testing of material biocompatibility and drug efficacy. | Using non-authenticated or contaminated cell lines is a primary source of irreproducible research. Tools like the "Bad Cell Lines" database help verify that cell lines are valid and not from a known contaminated line, preventing the perpetuation of bad science [89]. |
| Standardized Reference Materials | Certified materials with defined properties used to calibrate instruments and validate experiments. | Essential for ensuring reproducibility and cross-comparison of data, particularly in nanomaterials characterization. They provide a benchmark for verifying that experimental setups are yielding accurate measurements. |
| Validated Antibodies | Key reagents for detecting specific proteins (e.g., via Western Blot) in biological samples interacting with materials. | Inappropriate or unvalidated antibodies are a major source of unreliable data. Using validated antibodies from reputable sources ensures that reported protein expressions are accurate and not artifacts. |
| Electronic Lab Notebooks (ELNs) | Digital systems for recording experimental procedures, parameters, and raw data in a secure, time-stamped manner. | Protects intellectual property and provides an auditable trail for reproducibility. ELNs help prevent data fabrication and falsification by preserving original data, which is crucial during integrity investigations [35]. |
The escalating complexity of research misconduct, now amplified by sophisticated generative AI, demands an equally sophisticated and proactive response. Relying on a single tool or post-publication sleuthing is no longer tenable. As the analysis shows, a layered defense—integrating specialized tools like Proofig for images, iThenticate for text, and semantic tools for data quality—is critical for creating a credible "immune system" for scientific literature [34]. For the materials science and drug development community, where reproducibility and reliability are paramount, the adoption of these integrated protocols is not merely a best practice but a fundamental component of modern scientific rigor. By implementing these methodologies, researchers, institutions, and publishers can collectively safeguard their reputation, protect financial investments, and, most importantly, uphold the public trust in science.
Conclusion
Upholding research integrity is not a one-time task but a continuous commitment embedded throughout the materials science research cycle. By combining a solid understanding of ethical principles with modern AI-powered tools, robust training, and clear institutional policies, the research community can effectively safeguard its work. A proactive approach to integrity—where checks are integrated into the workflow rather than being a final hurdle—is paramount. This not only protects individual reputations but also fortifies the foundation of scientific knowledge, ensuring that breakthroughs in materials science, from metamaterials to sustainable composites, are built on credible and reproducible data. Ultimately, this fosters greater public trust and accelerates the safe and effective translation of research from the lab to clinical and commercial applications.
References
- 1. Research Misconduct in 2025: New Definitions, Cases & ... [https://www.kuali.co/post/what-is-research-misconduct-new-definitions-cases-and-how-to-prevent-it-in-2025]
- 2. Definition of Research Misconduct | ORI [https://ori.hhs.gov/definition-research-misconduct]
- 3. press releases [https://www.springernature.com/gp/group/media/press-releases/research-integrity-training-white-paper/27783258]
- 4. Evolving the Highly Cited Researchers List [https://clarivate.com/academia-government/blog/the-continuing-evolution-of-the-highly-cited-researchers-list-to-promote-fairness-accuracy-and-research-integrity/]
- 5. Insights from PRC 2025 on Fraud, Paper Mills & Peer Review [https://www.highwirepress.com/blog/scaling-integrity-peer-review-prc2025]
- 6. What experts are saying about the future of research ... [https://dataseer.ai/2025/03/12/what-experts-are-saying-about-the-future-of-research-integrity-in-an-ai-driven-world/]
- 7. Science Integrity Digest Summer 2025 [https://scienceintegritydigest.com/2025/07/25/science-integrity-digest-summer-2025/]
- 8. Improving Research Integrity: The Role of Accountability ... [https://www.appe-ethics.org/researchintegrity/]
- 9. New model explicitly outlines each step of the materials ... [https://ceramics.org/ceramic-tech-today/model-outlines-materials-science-research-process/]
- 10. Research Integrity definitions and challenges [https://www.sciencedirect.com/science/article/pii/S0895435624001227]
- 11. Research Integrity: Where We Are and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10695751/]
- 12. Mastering Metrics: A Guide to Quantitative Data Collection ... [https://research-rebels.com/blogs/how-to-write-thesis/mastering-metrics-a-guide-to-quantitative-data-collection-methods]
- 13. 5 Methods of Data Collection for Quantitative Research [https://www.quantilope.com/resources/glossary-data-collection-methods-quantitative-research]
- 14. Research Integrity [https://research.mit.edu/security-integrity-and-compliance/research-integrity]
- 15. Figures and Charts - UNC Writing Center [https://writingcenter.unc.edu/tips-and-tools/figures-and-charts/]
- 16. Color contrast - Accessibility - MDN Web Docs - Mozilla [https://developer.mozilla.org/en-US/docs/Web/Accessibility/Guides/Understanding_WCAG/Perceivable/Color_contrast]
- 17. Contrast Checker [https://webaim.org/resources/contrastchecker/]
- 18. Fraud and Deceit in Medical Research | Voices in Bioethics [https://journals.library.columbia.edu/index.php/bioethics/article/view/8940]
- 19. Financial costs and personal consequences of research ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC4132287/]
- 20. Research Integrity Metrics - Research Analytics [https://researchanalytics.northwestern.edu/or-unit-metrics/research-integrity-metrics.html]
- 21. New Report Identifies Policy Options to Improve Federal ... [https://www.nationalacademies.org/news/2025/09/new-report-identifies-policy-options-to-improve-federal-research-regulations-bolster-u-s-scientific-competitiveness]
- 22. Top 10 most highly cited retracted papers [https://retractionwatch.com/the-retraction-watch-leaderboard/top-10-most-highly-cited-retracted-papers/]
- 23. Retractions Increase 10-Fold in 20 Years - and Now AI is ... [https://www.aapsnewsmagazine.org/aapsnewsmagazine/articles/new-page3/feb25/meetings-feb25?]
- 24. Controversial 'arsenic life' paper retracted from 'Science' - C&EN [https://cen.acs.org/policy/publishing/Controversial-arsenic-life-paper-retracted/103/web/2025/07]
- 25. Characterizing the effect of retractions on publishing careers [https://www.nature.com/articles/s41562-025-02154-0]
- 26. What a Declining System Looks Like: Fraud Crisis in ... [https://scienceandculture.com/2025/11/what-a-declining-system-looks-like-fraud-crisis-in-science-grows/]
- 27. INTEGRITY Training Guide [https://embassy.science/wiki/Guide:39eb092a-b4be-41a3-a070-872cbfbcc6ca]
- 28. Automated Image Integrity Detection for Researchers [https://www.proofig.com/proofig-for-researchers]
- 29. Automated Image Integrity Detection for Research institution [https://www.proofig.com/proofig-for-research-institutions]
- 30. Proofig AI: Ensuring Research Integrity with AI-Powered ... [https://mdpiblog.wordpress.sciforum.net/2025/09/10/proofig-ai/]
- 31. Proofig AI | Upholding Research Integrity with AI Image ... [https://www.proofig.com/]
- 32. AI-Generated Image Detection: A Leap in Scientific Integrity [https://intercom.help/proofig/en/articles/9545784-ai-generated-image-detection-a-leap-in-scientific-integrity]
- 33. Generative AI Guide: Proofig - AI Image Detection - GalterGuides [https://libguides.galter.northwestern.edu/c.php?g=1389126&p=10769974]
- 34. Protecting Integrity with Proofig's AI-Generated Image ... [https://www.proofig.com/ai-in-research-proofig-ai-s-microscopy-ai-generated-image-detection]
- 35. Proofig AI News | Advancements in Research Integrity & ... [https://www.proofig.com/newsroom]
- 36. New tool supports researchers and enhances research integrity [https://research.osu.edu/new-tool-supports-researchers-and-enhances-research-integrity]
- 37. Research Integrity Tools [https://laneguides.stanford.edu/research-integrity/tools]
- 38. New Research Integrity Tools Available to Feinberg Faculty ... [https://galter.northwestern.edu/news/new-research-integrity-tools-available-to-feinberg-faculty-and-staff-proofig-ithenticate]
- 39. Research Integrity Tools for Journals: Plagiarism detection ... [https://blog.scholasticahq.com/post/research-integrity-toolkit-plagiarism-detection/]
- 40. STM Integrity Hub [https://stm-assoc.org/what-we-do/strategic-areas/research-integrity/integrity-hub/]
- 41. Research integrity | Resources [https://toolsuite.diamas.org/research-integrity]
- 42. Resources [https://www.ithenticate.com/resources]
- 43. Exploring the Need to Use “Plagiarism” Detection Software ... [https://www.mdpi.com/2304-6775/13/1/1]
- 44. iThenticate Product Updates [https://guides.ithenticate.com/hc/en-us/articles/34065932643597-iThenticate-Product-Updates]
- 45. iThenticate release notes [https://guides.ithenticate.com/hc/en-us/articles/27871174228365-iThenticate-release-notes]
- 46. Online Learning Tool for Research Integrity and Image ... [https://ori.hhs.gov/education/products/RIandImages/default.html]
- 47. Research Integrity in Science and Education(RISE) [https://www.springernature.com/gp/researchers/campaigns/research-integrity-in-science-and-education]
- 48. Educating and Training in Research Integrity (RI): A Study ... [https://link.springer.com/article/10.1007/s10805-023-09497-1]
- 49. Materials science breakthroughs 2025: Trends to watch [https://www.cas.org/resources/cas-insights/materials-science-trends-2025]
- 50. Part I. Shared Values | ORI [https://ori.hhs.gov/content/part-i-shared-values]
- 51. ORI is Updating its Policies on Research Integrity to Meet ... [https://ori.hhs.gov/blog/ori-updating-its-policies-research-integrity-meet-demands-modern-research-environment]
- 52. A Taxonomy for Research Integrity Training [https://pmc.ncbi.nlm.nih.gov/articles/PMC10129911/]
- 53. Institutional structure to ensure research integrity [https://pubmed.ncbi.nlm.nih.gov/8373489/]
- 54. Research Integrity & Misconduct [https://www.cogr.edu/topics/research-integrity-misconduct]
- 55. Self-Plagiarism - Office of Academic Integrity - Mizzou [https://oai.missouri.edu/students/self-plagiarism/]
- 56. Duplicate (Dual) Publications | ORI [https://ori.hhs.gov/duplicate-dual-publications]
- 57. Self-Plagiarism and Redundant Publications: A True ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12474262/]
- 58. Self-Plagiarism: How to Define It and Why You Should ... [https://www.aje.com/arc/self-plagiarism-how-to-define-it-and-why-to-avoid-it]
- 59. Unintentional Error - an overview [https://www.sciencedirect.com/topics/engineering/unintentional-error]
- 60. International Team Constructs Definition, Inventory of ... [https://www.psychologicalscience.org/publications/observer/questionable-research-practices.html]
- 61. Questionable Research Practices (and ... [https://www.aje.com/arc/questionable-research-practices]
- 62. Minimizing Questionable Research Practices – The Role of ... [https://link.springer.com/article/10.1007/s10805-024-09520-z]
- 63. Understanding human failures in maintenance [https://humanfactors101.com/topics/maintenance-error/]
- 64. Presenting Quantitative Data Graphically [https://courses.lumenlearning.com/waymakermath4libarts/chapter/presenting-quantitative-data-graphically/]
- 65. Text has enhanced contrast | ACT Rule | WAI [https://www.w3.org/WAI/standards-guidelines/act/rules/09o5cg/]
- 66. Change text color based on brightness of the covered ... [https://stackoverflow.com/questions/11867545/change-text-color-based-on-brightness-of-the-covered-background-area]
- 67. How can I set a text color to always contrast with the fill ... [https://stackoverflow.com/questions/62800823/how-can-i-set-a-text-color-to-always-contrast-with-the-fill-color-of-a-chart]
- 68. Research integrity in the era of artificial intelligence [https://pmc.ncbi.nlm.nih.gov/articles/PMC11224801/]
- 69. Publication Pressure vs Research Integrity: Global Insights ... [https://www.csescienceeditor.org/article/publication-pressure-vs-research-integrity-global-insights-from-an-asian-council-of-science-editors-survey/]
- 70. MSQA: Benchmarking LLMs on Graduate-Level Materials ... [https://arxiv.org/html/2505.23982v1]
- 71. David Ammons answers questions about new benchmarking ... [https://www.sog.unc.edu/about/news/david-ammons-answers-questions-about-new-benchmarking-publication]
- 72. Benchmarking for Open Universities: Guidelines and Good ... [https://iite.unesco.org/publications/benchmarking-for-open-universities-guidelines-and-good-practices/]
- 73. UPCEA's 2025 Online Education Benchmarking Report ... [https://upcea.edu/upceas-2025-online-education-benchmarking-report-provides-vital-data-for-university-leaders/]
- 74. Trends in research integrity concerns and the evolving role of ... [https://insights.uksg.org/articles/10.1629/uksg.663]
- 75. Outreach, Training, and Scientific Integrity Materials [https://www.epa.gov/scientific-integrity/outreach-training-and-scientific-integrity-materials]
- 76. The Final Rule on Research Misconduct Regulations [https://www.ebglaw.com/insights/publications/the-final-rule-on-research-misconduct-regulations-what-institutions-need-to-know-as-implementation-looms]
- 77. New Efforts to Advance Electronic Health Information Sharing [https://www.kff.org/patient-consumer-protections/charting-the-way-forward-new-efforts-to-advance-electronic-health-information-sharing/]
- 78. Health Data Interoperability & Integration in 2025 [https://talencio.com/breaking-barriers-health-data-interoperability-integration-in-2025/]
- 79. Compliance Trends of 2025 [https://www.encryptionconsulting.com/compliance-trends-of-2025/]
- 80. Improving research integrity: a framework for responsible ... [https://bmcresnotes.biomedcentral.com/articles/10.1186/s13104-022-06065-5]
- 81. Conceptualizing the research cycle for the field of materials ... [https://link.springer.com/article/10.1557/s43577-025-00931-w]
- 82. Materials Science & Engineering: Literature Reviews [https://lib.guides.umd.edu/materialsscience/tips-tools/lit-rev]
- 83. Writing a Scientific Review Article: Comprehensive Insights for ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10807936/]
- 84. A Practical Guide to Quantitative Data Analysis Methods ... [https://www.looppanel.com/blog/quantitative-data-analysis-methods]
- 85. Gap analysis for literature reviews and advancing useful ... [https://www.researchtoaction.org/2020/06/gap-analysis-for-literature-reviews-and-advancing-useful-knowledge/]
- 86. Quantitative Data Analysis Methods & Techniques 101 [https://gradcoach.com/quantitative-data-analysis-methods/]
- 87. An Overview of the Fundamentals of Data Management ... [https://www.sciencedirect.com/science/article/pii/S0749208123000293]
- 88. Imagetwin: Image Analysis AI Software for Research [https://imagetwin.ai/]
- 89. Research Integrity Tools [https://www.accessinn.com/research-integrity-tools/]